Question: How can an attacker exploit the following SQL query? SELECT * FROM users WHERE username = 'input' AND password = 'password'; By creating a new
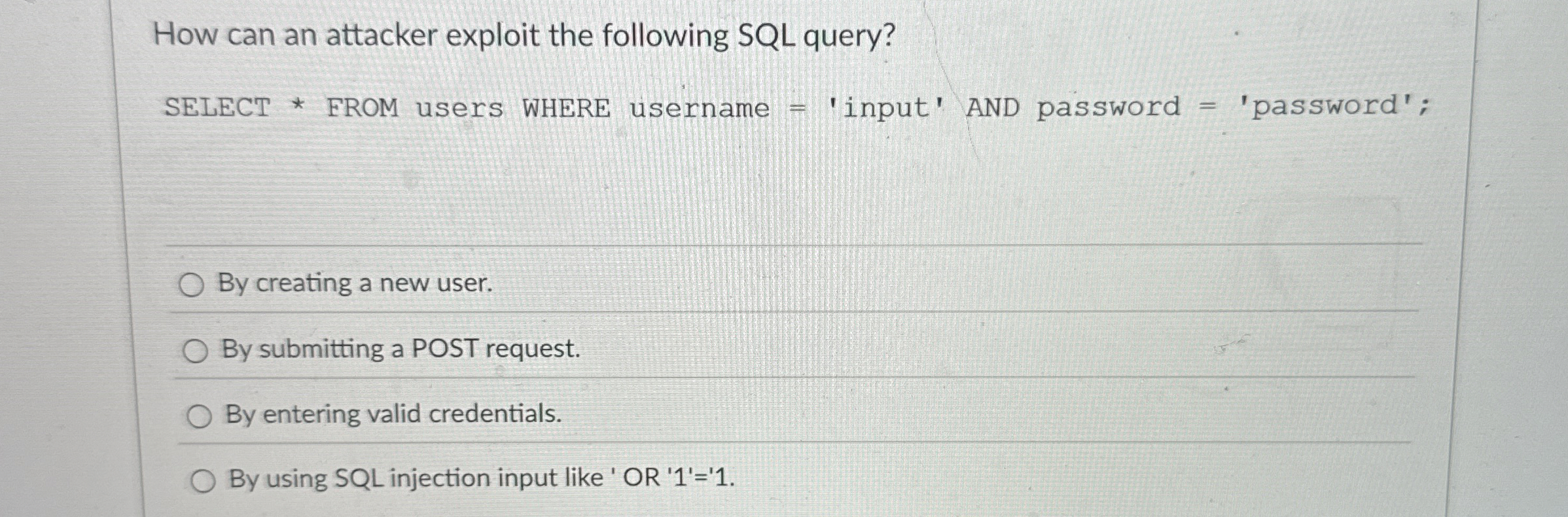
How can an attacker exploit the following SQL query?
SELECT FROM users WHERE username 'input' AND password 'password';
By creating a new user.
By submitting a POST request.
By entering valid credentials.
By using SQL injection input like OR
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


