Question: How do anomaly - based detection methods in NSM work? By using predefined threat signatures By identifying deviations from established normal behavior patterns By scanning
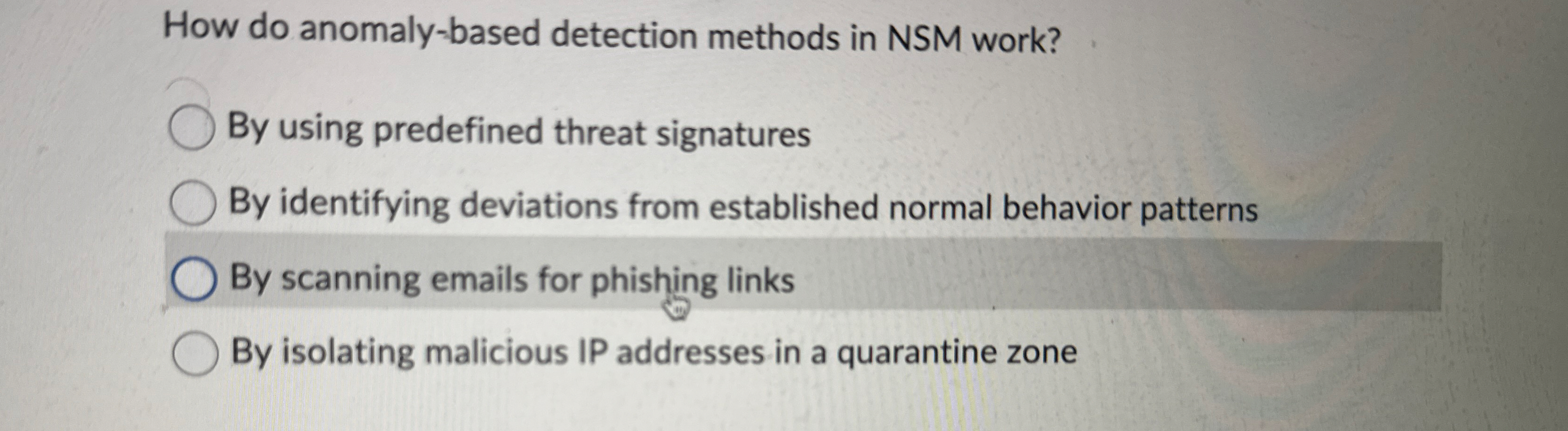
How do anomalybased detection methods in NSM work?
By using predefined threat signatures
By identifying deviations from established normal behavior patterns
By scanning emails for phishing links
By isolating malicious IP addresses in a quarantine zone
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


