Question: How do attackers proceed after identifying service accounts in a Kerberoasting attack? Check All That Apply They request TGS tickets from the Kerberos KDC They
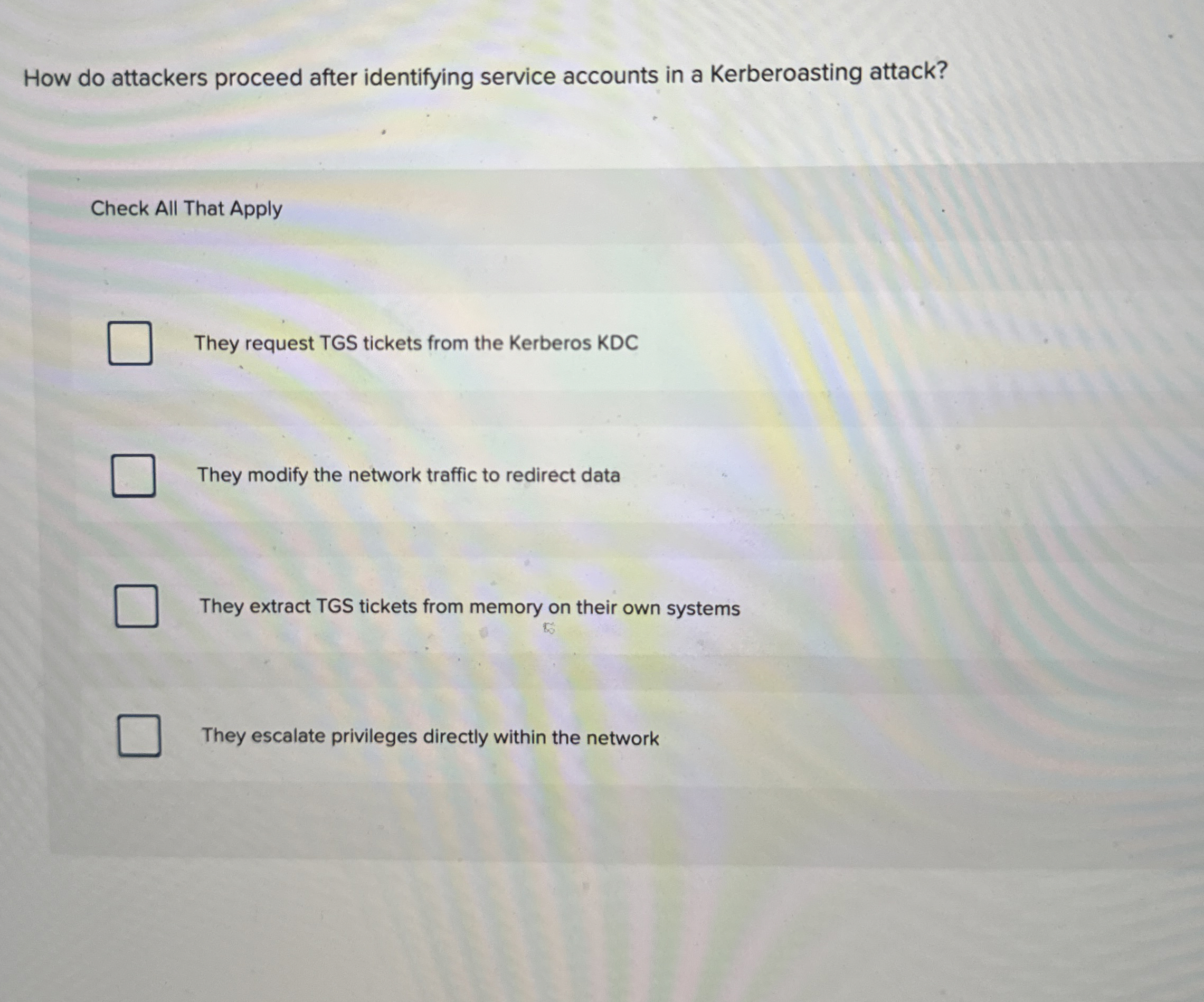
How do attackers proceed after identifying service accounts in a Kerberoasting attack?
Check All That Apply
They request TGS tickets from the Kerberos KDC
They modify the network traffic to redirect data
They extract TGS tickets from memory on their own systems
They escalate privileges directly within the network
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


