Question: How does excessive privilege abuse differ from legitimate privilege abuse? Select one or more: O A. Excessive privilege abuse occurs when a user abuses
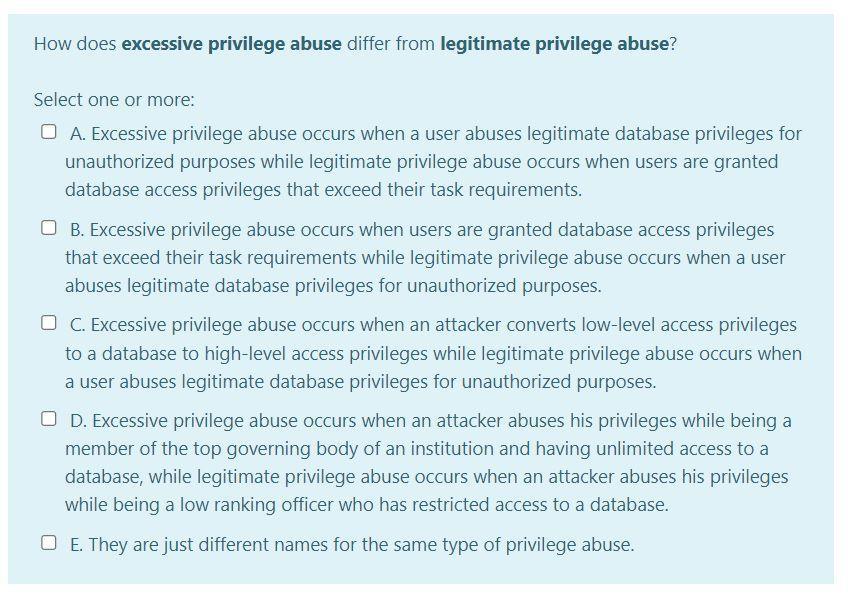
How does excessive privilege abuse differ from legitimate privilege abuse? Select one or more: O A. Excessive privilege abuse occurs when a user abuses legitimate database privileges for unauthorized purposes while legitimate privilege abuse occurs when users are granted database access privileges that exceed their task requirements. O B. Excessive privilege abuse occurs when users are granted database access privileges that exceed their task requirements while legitimate privilege abuse occurs when a user abuses legitimate database privileges for unauthorized purposes. O C. Excessive privilege abuse occurs when an attacker converts low-level access privileges to a database to high-level access privileges while legitimate privilege abuse occurs when a user abuses legitimate database privileges for unauthorized purposes. OD. Excessive privilege abuse occurs when an attacker abuses his privileges while being a member of the top governing body of an institution and having unlimited access to a database, while legitimate privilege abuse occurs when an attacker abuses his privileges while being a low ranking officer who has restricted access to a database. O E. They are just different names for the same type of privilege abuse.
Step by Step Solution
3.40 Rating (150 Votes )
There are 3 Steps involved in it
The correct options that highlight the differences between excessive privilege abuse and legitimate ... View full answer

Get step-by-step solutions from verified subject matter experts


