Question: Cryptography - Cryptography is the art of writing or solving codes (en.oxforddictionaries.com). - In this assignment, you are given some ciphertext in the form
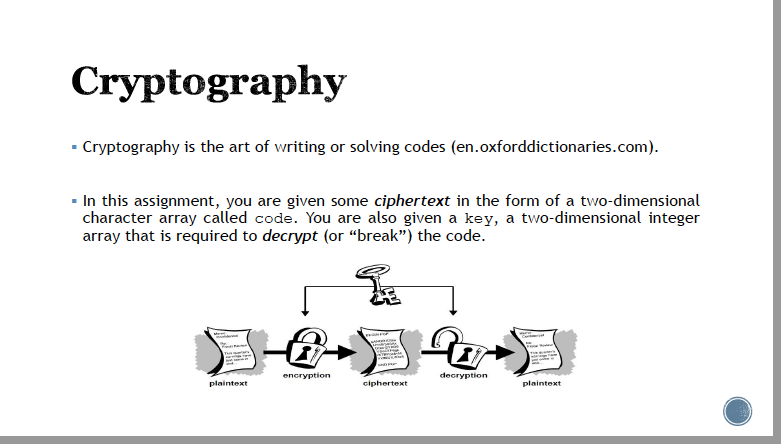
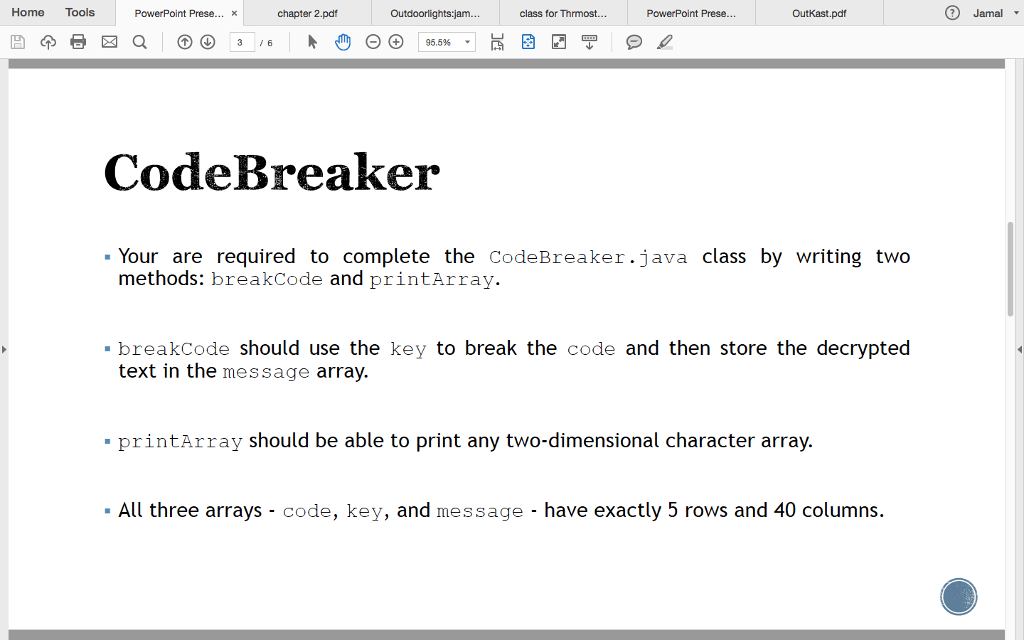
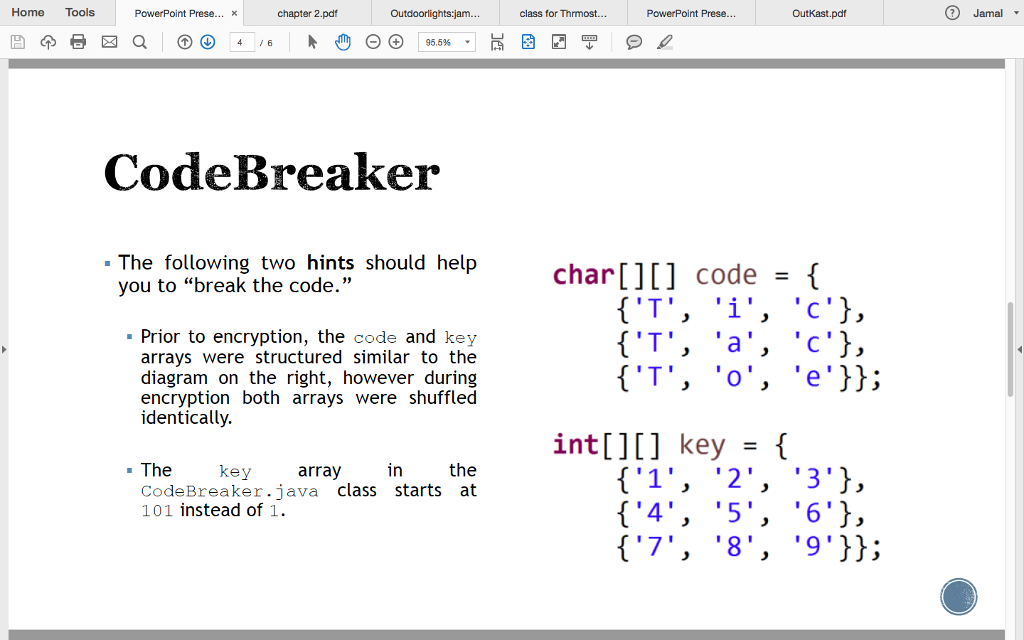
Cryptography - Cryptography is the art of writing or solving codes (en.oxforddictionaries.com). - In this assignment, you are given some ciphertext in the form of a two-dimensional character array called code. You are also given a key, a two-dimensional integer array that is required to decrypt (or "break") the code. plaintext encryption ciphertext 2 decryption plaintext Home Tools 3 a PowerPoint Prese... x 3 /6 chapter 2.pdf Outdoorlights:jam... (-) (+) 95.5% class for Thrmost... PowerPoint Prese... Outkast.pdf CodeBreaker Your are required to complete the CodeBreaker.java class by writing two methods: breakCode and printArray. breakCode should use the key to break the code and then store the decrypted text in the message array. printArray should be able to print any two-dimensional character array. All three arrays - code, key, and message - have exactly 5 rows and 40 columns. Jamal Home Tools 3 a PowerPoint Prese... x /6 chapter 2.pdf The Outdoorlights:jam... CodeBreaker - The following two hints should help you to "break the code." (-) (+) 95.5% Prior to encryption, the code and key arrays were structured similar to the diagram on the right, however during encryption both arrays were shuffled identically. key in the CodeBreaker.java class starts at 101 instead of 1. array class for Thrmost... PowerPoint Prese... Outkast.pdf char[][] code = { {'T', 'i', 'c'}, {'T', 'a', 'c'}, {'T', 'o', 'e'}}; int[][] key = { {'1', '2', '3'}, {'4', '5', '6'}, {'7', '8', '9'}}; Jamal
Step by Step Solution
3.40 Rating (153 Votes )
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


