I need help because I am very struggling with the homework, so I need to understand. Even
Fantastic news! We've Found the answer you've been seeking!
Question:
I need help because I am very struggling with the homework, so I need to understand. Even though I have other work to do, I still need help, so I can understand and give me some very helpful explanations.
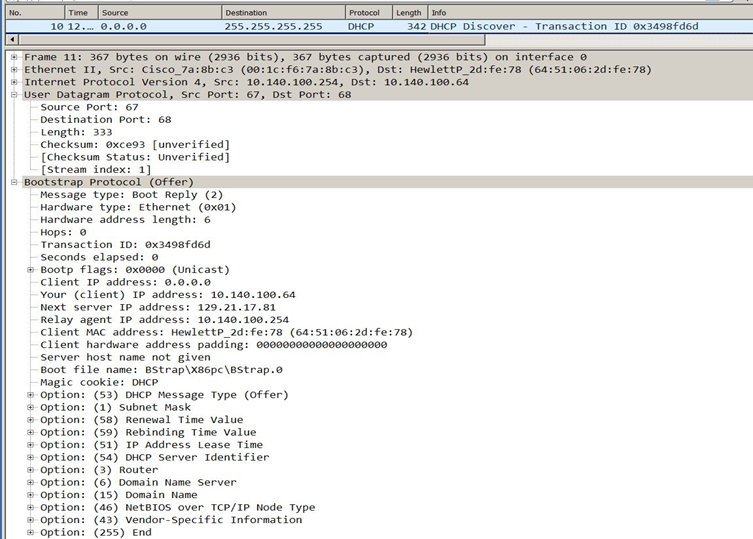
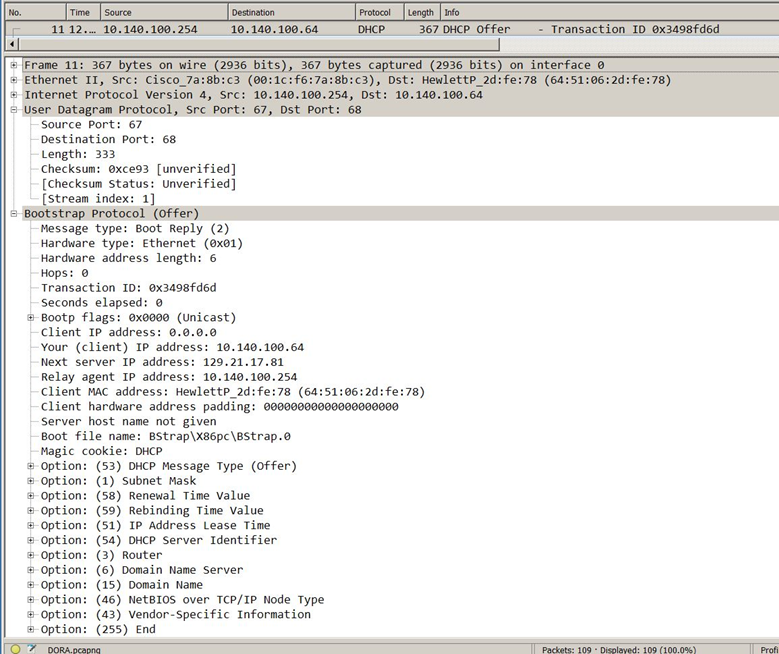
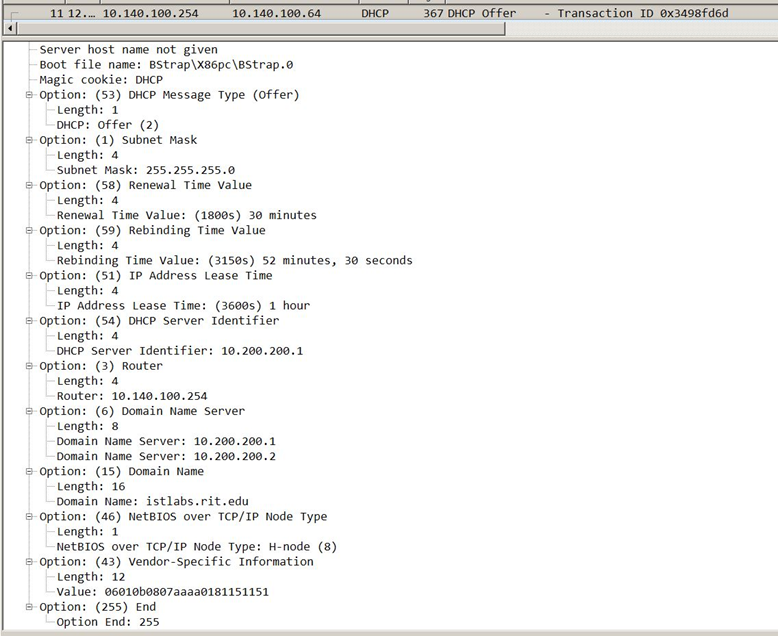
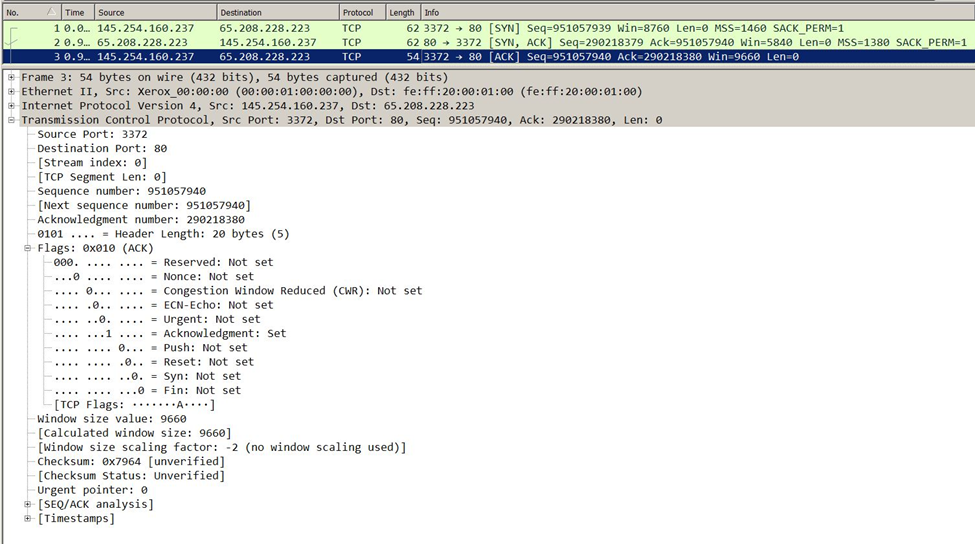
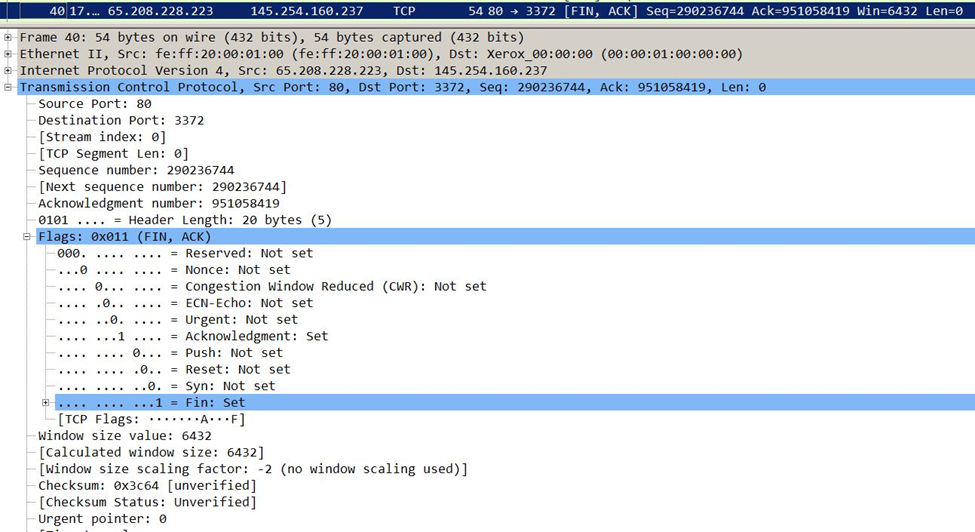
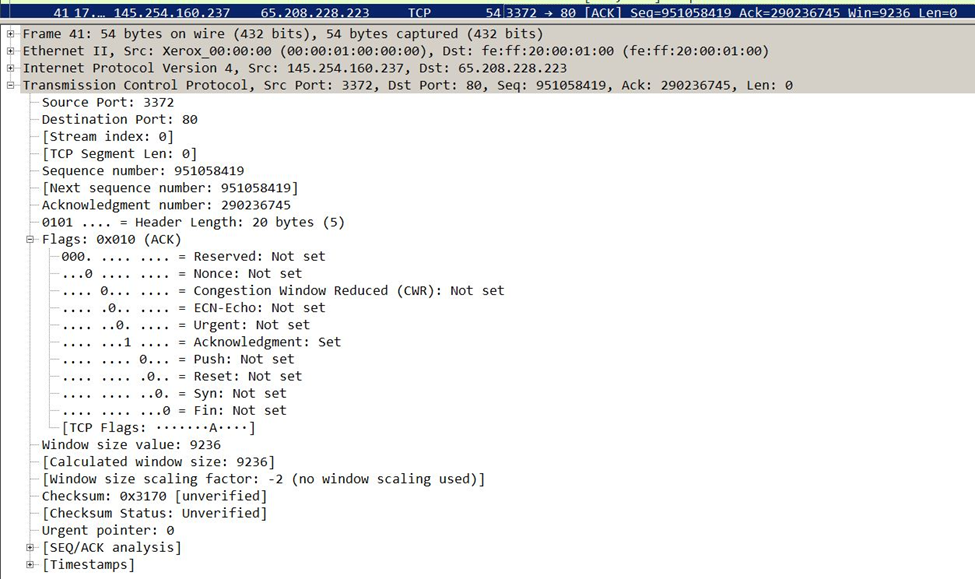
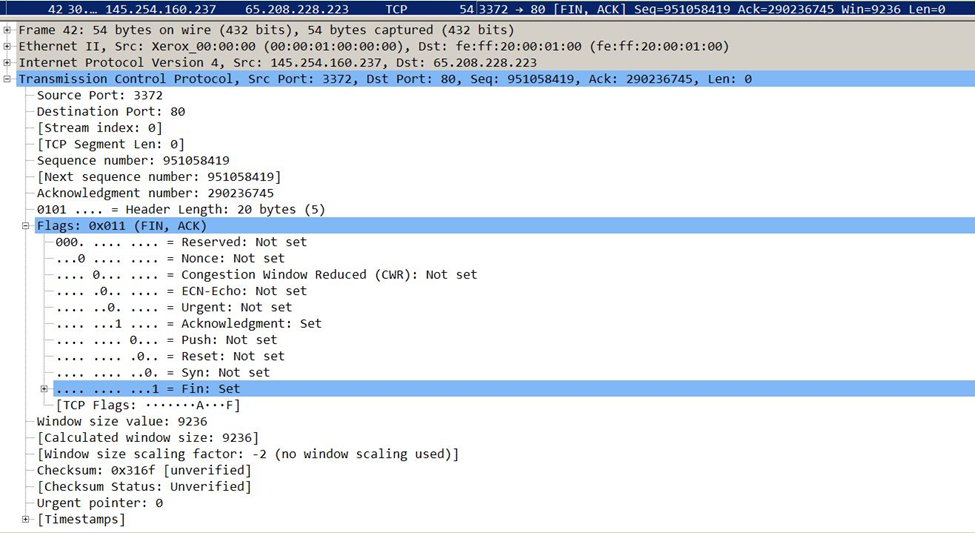
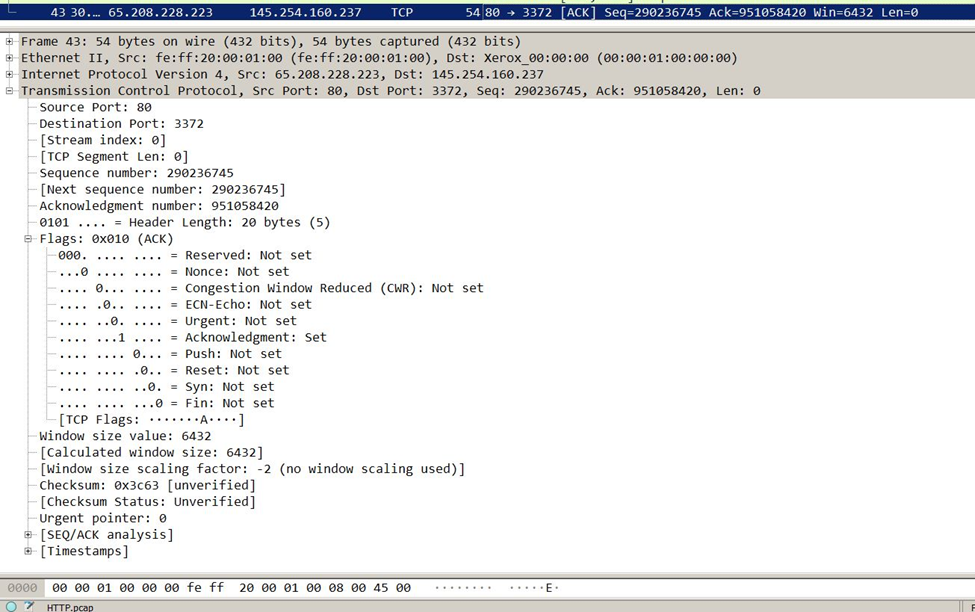
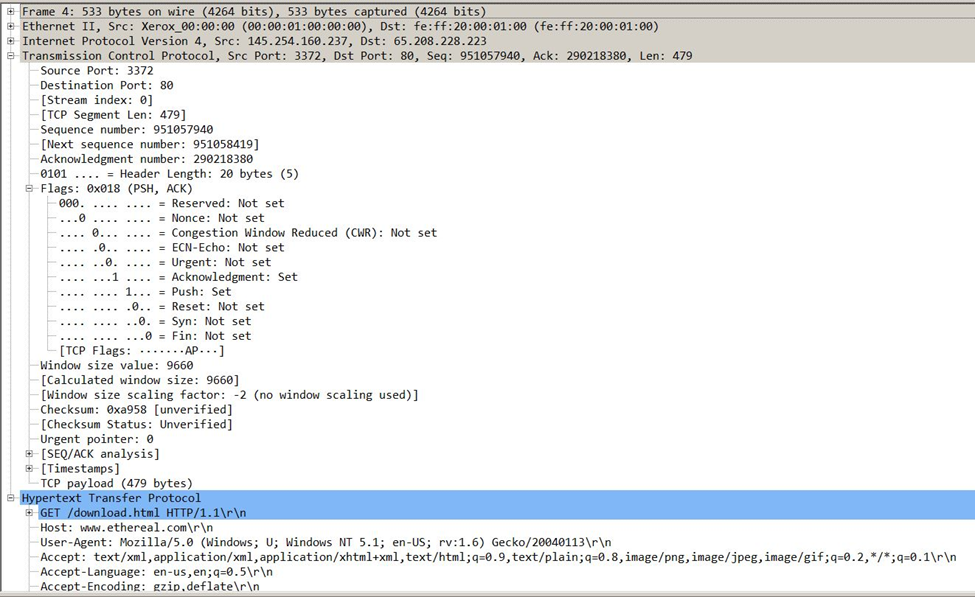
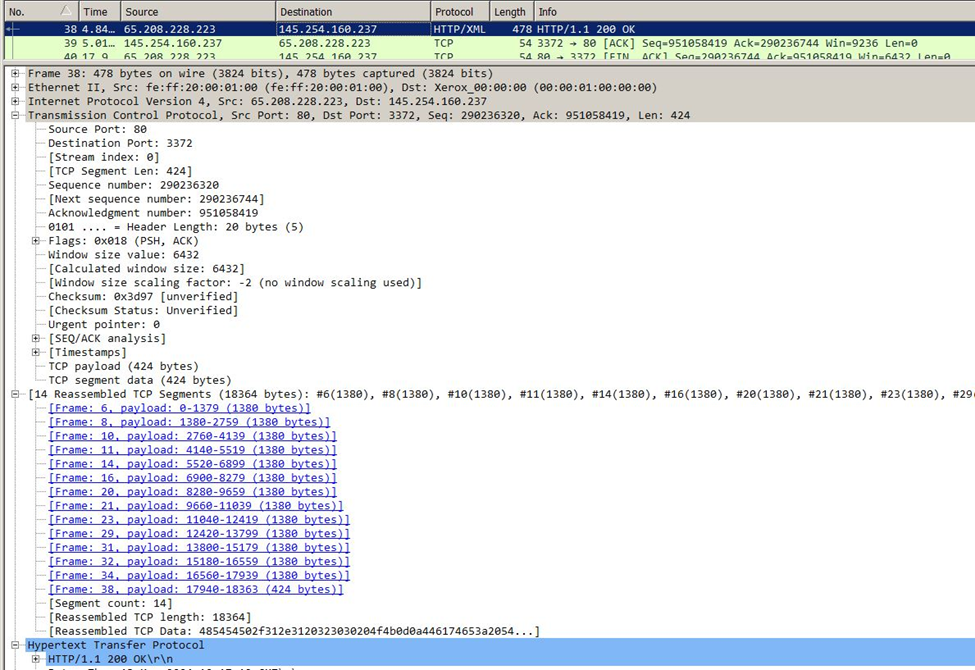
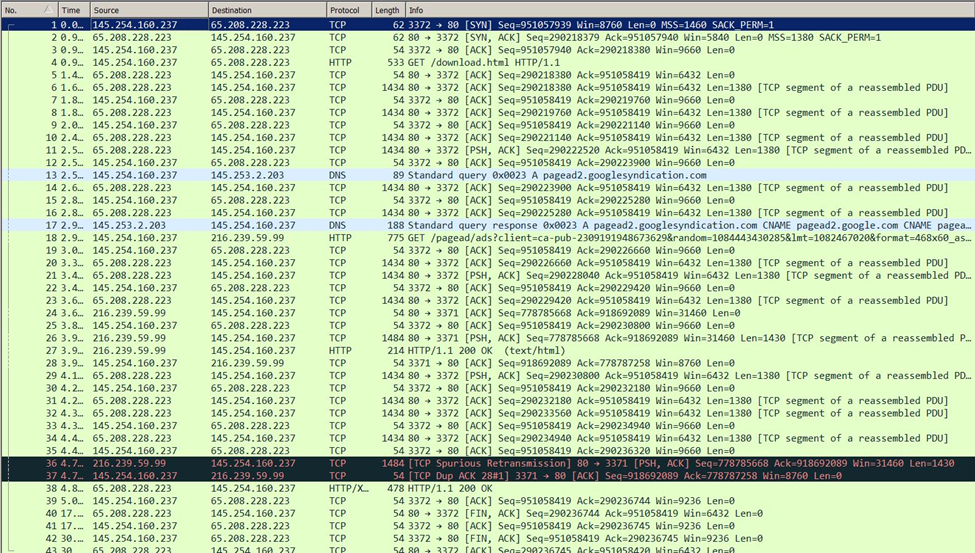
Transcribed Image Text:
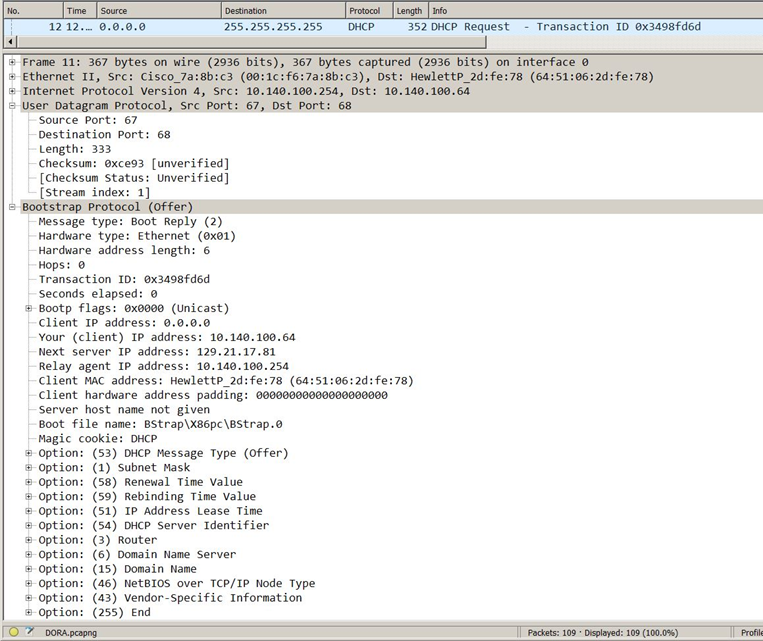
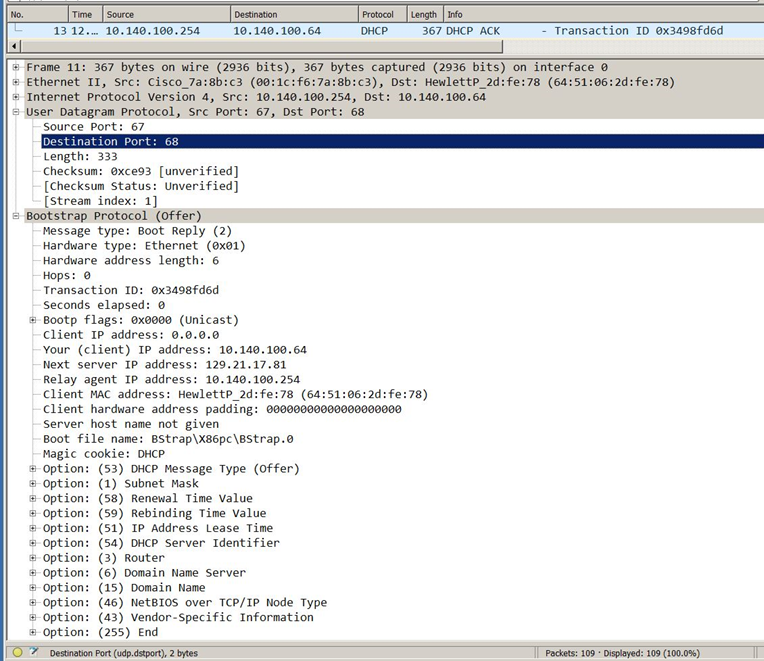
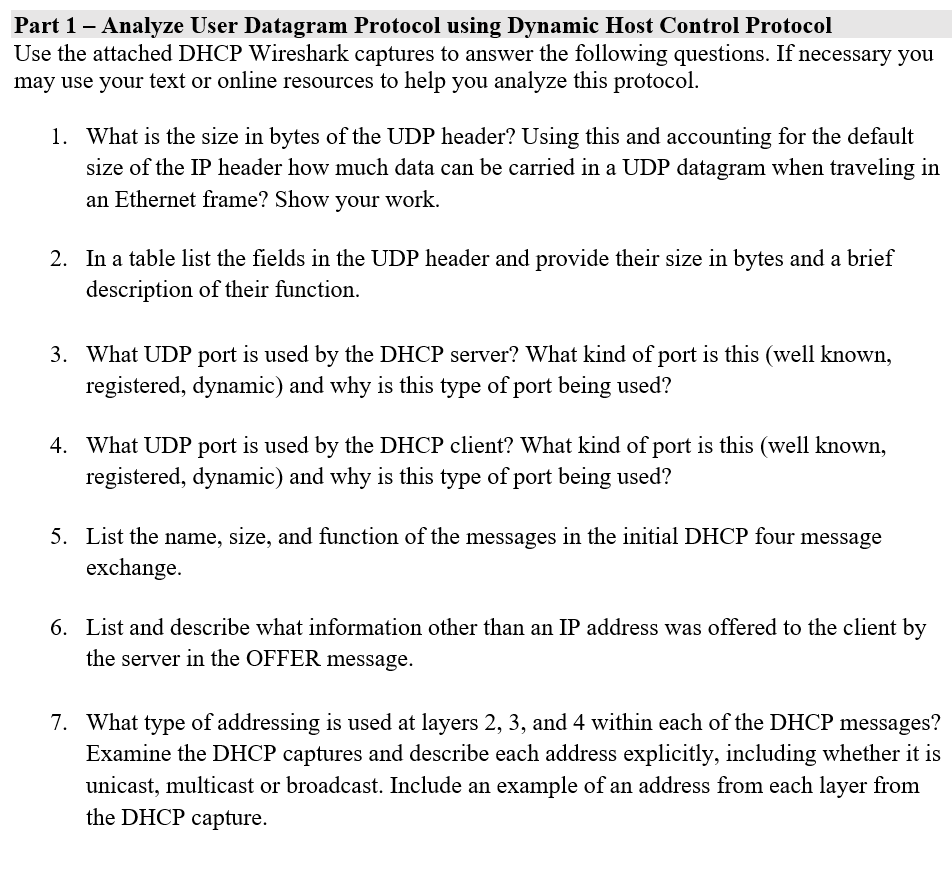
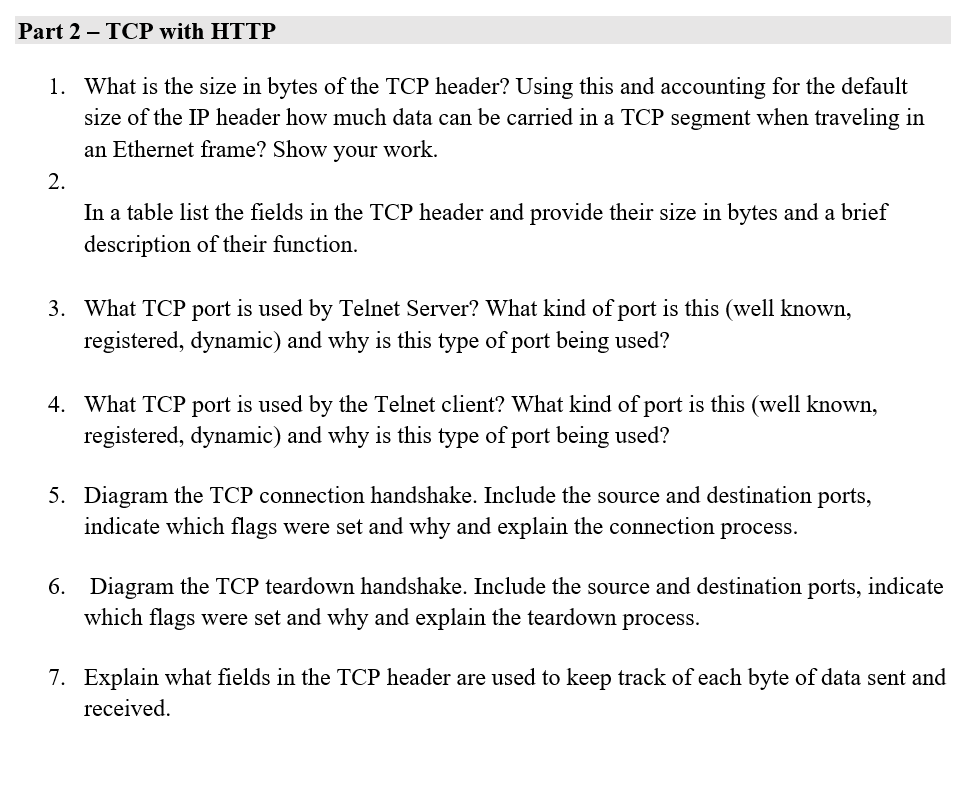
No. 4 Time Source 10 12. 0.0.0.0 Destination 255.255.255.255 Source Port: 67 Destination Port: 68 Length: 333 Checksum: exce93 [unverified] [Checksum Status: Unverified] [Stream index: 1] Frame 11: 367 bytes on wire (2936 bits), 367 bytes captured (2936 bits) on interface 0 Ethernet II, Src: Cisco_7a:8b:c3 (00:1c:f6:7a:8b:c3), Dst: Hewlettp_2d:fe:78 (64:51:06:2d:fe:78) Internet Protocol Version 4, Src: 10.140.100.254, Dst: 10.140.100.64 User Datagram Protocol, Src Port: 67, Dst Port: 68 Bootstrap Protocol (Offer) Message type: Boot Reply (2) Hardware type: Ethernet (0x01) Hardware address length: 6 Hops: 0 Transaction ID: 0x3498fd6d Seconds elapsed: 0 Bootp flags: ex0000 (Unicast) client IP address: 0.0.0.0 Your (client) IP address: 10.140.100.64 Next server IP address: 129.21.17.81 Relay agent IP address: 10.140.100.254 client MAC address: Hewlettp_2d:fe:78 (64:51:06:2d:fe:78) client hardware address padding: 00000000000000000000 Server host name not given Boot file name: BStrap\x86pc\BStrap.0 Magic cookie: DHCP Protocol Length Info DHCP Option: (53) DHCP Message Type (Offer) Option: (1) Subnet Mask Option: (58) Renewal Time Value Option: (59) Rebinding Time Value Option: (51) IP Address Lease Time Option: (54) DHCP Server Identifier Option: (3) Router Option: (6) Domain Name Server Option: (15) Domain Name 342 DHCP Discover Transaction ID 0x3498fd6d Option: (46) NetBIOS over TCP/IP Node Type Option: (43) Vendor-Specific Information Option: (255) End No. 4 Time Source 10 12. 0.0.0.0 Destination 255.255.255.255 Source Port: 67 Destination Port: 68 Length: 333 Checksum: exce93 [unverified] [Checksum Status: Unverified] [Stream index: 1] Frame 11: 367 bytes on wire (2936 bits), 367 bytes captured (2936 bits) on interface 0 Ethernet II, Src: Cisco_7a:8b:c3 (00:1c:f6:7a:8b:c3), Dst: Hewlettp_2d:fe:78 (64:51:06:2d:fe:78) Internet Protocol Version 4, Src: 10.140.100.254, Dst: 10.140.100.64 User Datagram Protocol, Src Port: 67, Dst Port: 68 Bootstrap Protocol (Offer) Message type: Boot Reply (2) Hardware type: Ethernet (0x01) Hardware address length: 6 Hops: 0 Transaction ID: 0x3498fd6d Seconds elapsed: 0 Bootp flags: ex0000 (Unicast) client IP address: 0.0.0.0 Your (client) IP address: 10.140.100.64 Next server IP address: 129.21.17.81 Relay agent IP address: 10.140.100.254 client MAC address: Hewlettp_2d:fe:78 (64:51:06:2d:fe:78) client hardware address padding: 00000000000000000000 Server host name not given Boot file name: BStrap\x86pc\BStrap.0 Magic cookie: DHCP Protocol Length Info DHCP Option: (53) DHCP Message Type (Offer) Option: (1) Subnet Mask Option: (58) Renewal Time Value Option: (59) Rebinding Time Value Option: (51) IP Address Lease Time Option: (54) DHCP Server Identifier Option: (3) Router Option: (6) Domain Name Server Option: (15) Domain Name 342 DHCP Discover Transaction ID 0x3498fd6d Option: (46) NetBIOS over TCP/IP Node Type Option: (43) Vendor-Specific Information Option: (255) End
Expert Answer:

Related Book For 

Posted Date:
Students also viewed these computer network questions
-
Write a Python Program to read and interpret a Hex file that contain "computer talk" Python Concepts: opening and reading a file, strings, lists, decisions, loops, conversion of data type and...
-
Design a Java class that represents a cache with a fixed size. It should support operations like add, retrieve, and remove, and it should evict the least recently used item when it reaches capacity.
-
Use any method to evaluate the limit or show that it does not exist. lim (x,y) (0,0) x - y x + y
-
A personal account earmarked as a retirement supplement contains $242,400. Suppose $200,000 is used to establish an annuity that earns 6%, compounded quarterly, and pays $4500 at the end of each...
-
A sedimentation process is to be used to separate pulverized coal from slate. A suspension of finely divided particles of galena (lead sulfide SG = 7.44) in water is prepared. The overall specific...
-
Predicting Used Car Prices (Bootstrap Forest and Boosted Trees). Return to the Toyota Corolla data, and refit the partition model. (Hint: Use the recall button in the partition dialog). This time,...
-
Match each term to the correct definition. Terms: a. Flexible budget b. Flexible budget variance c. Sales volume variance d. Static budget e. Variance Definitions: 1. A summarized budget for several...
-
Zina Chaburi has a full time job as a nurse in her local hospital. In her spare time she has a goat farming operation. The goat farm began in 2 0 2 1 , which resulted in a loss of $ 1 0 , 0 0 0 . She...
-
We need to swap the following registers. Do this using block moves. Before r1 r2 r3 r4 r5 r6 r7 After r3 r4 r5 r6 r7 r1 r2
-
On January 1, 2016, a company issues 3-year bonds with a face value of $200,000 and a stated interest rate of 8%. Because the market interest rate is higher than the stated interest rate, the company...
-
Among copper and gold, whose polarizability is higher? Justify your answer.
-
In this zone, we critically discuss the concepts of leadership and management and evaluate whether there is a clear dichotomy between them or whether definitional and practical overlaps exist. For...
-
In this zone, we critically examine the concept of performance management and evaluate whether it still has a role in the changing twenty-first century workplace. For over three decades, researchers...
-
Divide into two groups: one representing managers and the others representing employees. Separately, each group should come up with a number of arguments about the degree to which employees have a...
-
(a) To what extent do organisations have any responsibility to manage technical change in a way that preserves numbers of jobs? (b) Whatever your answer to the above question, to what extent do firms...
-
An old encryption system uses 24-bit keys. A cryptanalyst, who wants to brute-force attack the encryption system, is working on a computer system with a performance rate N keys per second. a- How...
-
One Way Cellular accountants have assembled the following data for the year ended September 30, 2014: Prepare the operating activities section using the indirect method for One Way Cellulars...
-
Explain with supporting examples how situational factors might influence a persons preferred style of management.
-
Discuss critically and with supporting practical examples the likely advantages and disadvantages of working in a small group or team.
-
Late in 2001, the founder and Chief Executive Officer (CEO) of Top-to-Toe, Joanne Dunne, announced the decision to open up distribution by using the device of house parties. The house party involves...
-
Action Quest Games adjusts its accounts annually. The following information is available for the year ended December 31, 2025. 1. Purchased a 1-year insurance policy on June 1 for $1,800 cash. 2....
-
Why is carbon such a special atom?
-
With each pass of a comet about the Sun, the comets mass (a) remains virtually unchanged. (b) actually increases. (c) is appreciably reduced.

Study smarter with the SolutionInn App