I need some assistance with these snort rules. 1. Alert on any traffic with the RST flag
Fantastic news! We've Found the answer you've been seeking!
Question:
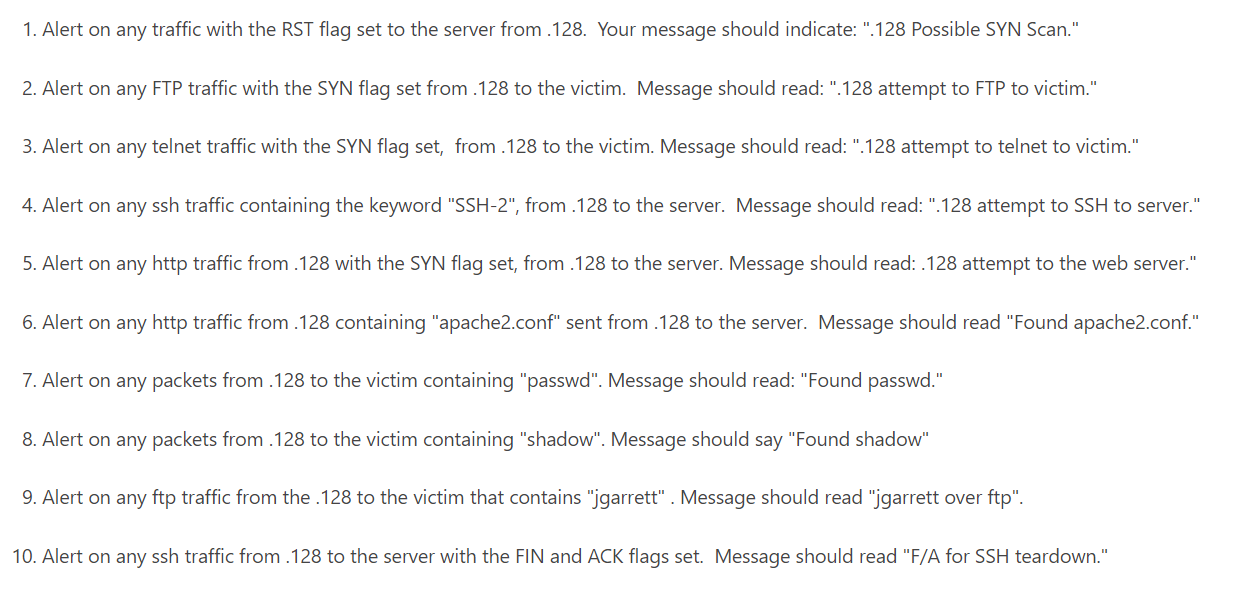
I need some assistance with these snort rules.
Transcribed Image Text:
1. Alert on any traffic with the RST flag set to the server from .128. Your message should indicate: ".128 Possible SYN Scan." 2. Alert on any FTP traffic with the SYN flag set from .128 to the victim. Message should read: ".128 attempt to FTP to victim." 3. Alert on any telnet traffic with the SYN flag set, from .128 to the victim. Message should read: ".128 attempt to telnet to victim." 4. Alert on any ssh traffic containing the keyword "SSH-2", from .128 to the server. Message should read: ".128 attempt to SSH to server." 5. Alert on any http traffic from .128 with the SYN flag set, from .128 to the server. Message should read: .128 attempt to the web server." 6. Alert on any http traffic from .128 containing "apache2.conf" sent from .128 to the server. Message should read "Found apache2.conf." 7. Alert on any packets from .128 to the victim containing "passwd". Message should read: "Found passwd." 8. Alert on any packets from .128 to the victim containing "shadow". Message should say "Found shadow" 9. Alert on any ftp traffic from the .128 to the victim that contains "jgarrett". Message should read "jgarrett over ftp". 10. Alert on any ssh traffic from .128 to the server with the FIN and ACK flags set. Message should read "F/A for SSH teardown." 1. Alert on any traffic with the RST flag set to the server from .128. Your message should indicate: ".128 Possible SYN Scan." 2. Alert on any FTP traffic with the SYN flag set from .128 to the victim. Message should read: ".128 attempt to FTP to victim." 3. Alert on any telnet traffic with the SYN flag set, from .128 to the victim. Message should read: ".128 attempt to telnet to victim." 4. Alert on any ssh traffic containing the keyword "SSH-2", from .128 to the server. Message should read: ".128 attempt to SSH to server." 5. Alert on any http traffic from .128 with the SYN flag set, from .128 to the server. Message should read: .128 attempt to the web server." 6. Alert on any http traffic from .128 containing "apache2.conf" sent from .128 to the server. Message should read "Found apache2.conf." 7. Alert on any packets from .128 to the victim containing "passwd". Message should read: "Found passwd." 8. Alert on any packets from .128 to the victim containing "shadow". Message should say "Found shadow" 9. Alert on any ftp traffic from the .128 to the victim that contains "jgarrett". Message should read "jgarrett over ftp". 10. Alert on any ssh traffic from .128 to the server with the FIN and ACK flags set. Message should read "F/A for SSH teardown."
Expert Answer:

Related Book For 

Business and Administrative Communication
ISBN: 978-0073403182
10th edition
Authors: Kitty o. locker, Donna s. kienzler
Posted Date:
Students also viewed these computer network questions
-
Design a Java class that represents a cache with a fixed size. It should support operations like add, retrieve, and remove, and it should evict the least recently used item when it reaches capacity.
-
CANMNMM January of this year. (a) Each item will be held in a record. Describe all the data structures that must refer to these records to implement the required functionality. Describe all the...
-
In Exercises 912, use the given conditions to write an equation for each line in point-slope form and general form Passing through (4, -7) and perpendicular to the line whose equation is x - 2y - 3 =...
-
Devaney Foods Company manufactures single-serve mustard packets used in fast-food restaurants. Al Devaney, the company's CFO, prepared the following standard cost card for a box of mustard packets...
-
RELATIVE DATING WORKSHEET Principles of Geology Law of Superposition: The youngest layer of rock is on the top. The oldest layer of rock is on the bottom Law of Original Horizontality: All...
-
Describe the first three industrial revolutions discussed in the text. Why do people believe that artificial intelligence will create a new age of industrial revolution?
-
Consider the following Cobb-Douglas production function for the bus transportation system in a particular city: Q = L1F2K3 Where L = labor input in worker hours F = fuel input in gallons K = capital...
-
ACCOUNTS AMOUNTS IN PESO June July 1 Cash on hand 20,000.00 45,000.00 2 Accounts Receivable 10,000.00 15,000.00 3 Sales 230,000.00 220,000.00 4 Allowance for doubtful accounts 5,000.00 5,000.00 5...
-
Shauna Coleman is single. She is employed as an architectural designer for Streamline Design (SD). Shauna wanted to determine her taxable income for this year. She correctly calculated her AGI....
-
Consider the following information: Portfolio Expected Return Beta Risk-free 6% 0 Market 10.8 1.0 A 8.8 1.7 Required: a. Calculate the return predicted by CAPM for a portfolio with a beta of 1.7 b....
-
According to the benefit principle of taxation, a businesss tax in a state should be related to the benefits to the business from services provided by the state and local governments. Practically, a...
-
Suppose that a state government levies an ad valorem sales tax on the purchase of all goods at retail but not on the purchases of services. The tax is levied only on final sales of goods and not on...
-
The two most important state taxes are income and general sales taxes, although states also make substantial use of excise taxes, direct business taxes (usually a corporate income tax), and others....
-
In the United States, primary and secondary education is usually provided by local government, although partly financed by state government grants. As a result, there are often substantial...
-
Explain why it may be necessary for state governments to begin to replace unit (per gallon) gasoline excise taxes with an alternative tax or different revenue source. Make the case for a user fee...
-
Utility from clean air (public good) is us(A) = 55A A^2 and Leo's utility from clean air is ul(A) = 45A2A^2. A is the amount of clean air in their apartment. In order to clean up the air in their...
-
Suppose the government bond described in problem 1 above is held for five years and then the savings institution acquiring the bond decides to sell it at a price of $940. Can you figure out the...
-
What are ways to de-emphasize costs or donation requests?
-
When should you not apologize?
-
What are some ethical components of communication?
-
What are the PMI and PRINCE2?
-
What are the differences between a framework, a methodology and a standard?
-
Individually identify what you consider to be the greatest achievements accomplished by human kind in the last decade. Now share your list with other students in the class and come up with an...

Study smarter with the SolutionInn App