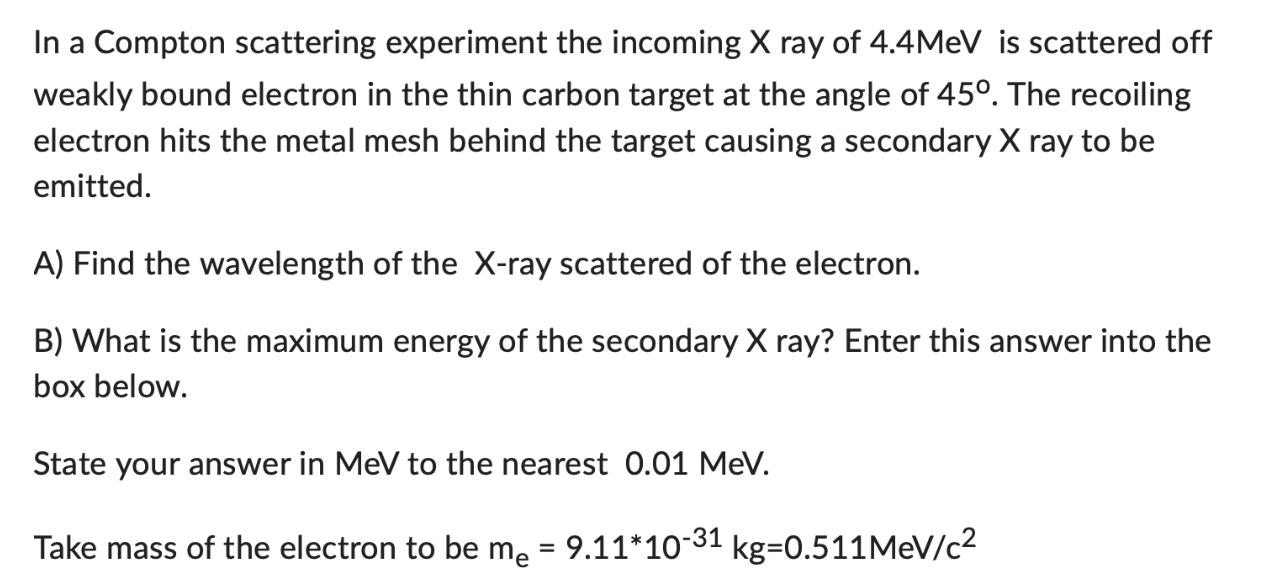
In a Compton scattering experiment the incoming X ray of 4.4MeV is scattered off weakly bound...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
In a Compton scattering experiment the incoming X ray of 4.4MeV is scattered off weakly bound electron in the thin carbon target at the angle of 450. The recoiling electron hits the metal mesh behind the target causing a secondary X ray to be emitted. A) Find the wavelength of the X-ray scattered of the electron. B) What is the maximum energy of the secondary X ray? Enter this answer into the box below. State your answer in MeV to the nearest 0.01 MeV. Take mass of the electron to be me = 9.11*10-31 kg=0.511MeV/c In a Compton scattering experiment the incoming X ray of 4.4MeV is scattered off weakly bound electron in the thin carbon target at the angle of 450. The recoiling electron hits the metal mesh behind the target causing a secondary X ray to be emitted. A) Find the wavelength of the X-ray scattered of the electron. B) What is the maximum energy of the secondary X ray? Enter this answer into the box below. State your answer in MeV to the nearest 0.01 MeV. Take mass of the electron to be me = 9.11*10-31 kg=0.511MeV/c
Expert Answer:
Answer rating: 100% (QA)
This is a problem involving Compton scattering which is a phenomenon where Xray or gamma ray photons scatter off electrons and in doing so transfer so... View the full answer

Related Book For 

Physics
ISBN: 978-0077339685
2nd edition
Authors: Alan Giambattista, Betty Richardson, Robert Richardson
Posted Date:
Students also viewed these physics questions
-
Water is used to cool R134a in the condenser of Fig. 4.61. The refrigerant enters the counter flow heat exchanger at 800 kPa, 80°C and a mass flow rate of 2 kg/s. The refrigerant exits as a...
-
A Compton scattering experiment is performed using an aluminum target. The incident photons have wavelength . The scattered photons have wavelengths and energies E that depend on the scattering...
-
To some U.S. manufacturers and labor unions, a cheap yuan value gives China's advantage in the global economy. bankers exports importers subsidies an unfair
-
Cunnington Furniture doesn't expect prices to change dramatically and wants to use a method that averages price changes. 1. Which inventory method would best meet Cunnington Furniture's goal? 2. What...
-
I got 5 quetion which is about dabase system NoSQL . just need some answer fot these quetion . What advantage does the aggregate data model offer for development of applications in a clustered...
-
What is the plain-meaning rule?
-
Ratio Computation and Analysis; Liquidity) as loan analyst for Madison Bank, you have been presented the following information. Each of these companies has requested a loan of $50,000 for 6 months...
-
1. Two-point boundary value problem with Dirichlet condition. Consider the following second order elliptic boundary value problem in the one-dimensional space: - -u" (x) = 2, x = (0, 1), u(0) = 0,...
-
You are asked to prepare a presentation entitled "Planning Principles for Our Multistate Clients" for colleagues in the corporate tax department. The company has already work with clients operating...
-
Fahrenheit to Celsius using multiple statements Given a Fahrenheit value temperature Fahrenheit, write a statement that assigns temperature Celsius with the equivalent Celsius value. While the...
-
Question 5 (a) The current market price of a three-month European put option on a non-dividend paying stock with a strike price of 43 is 5.50. The stock price is 45.00, and the risk-free interest...
-
Explain how the activities relate to processes and the development of a software system for either enhancement or new deployment in an organization. Be sure to provide an example of a software system...
-
ni ari 6. If a system is designed to have backup servers and redundancy to ensure continuous operation, which aspect of the CIA triad is being emphasized? a) Confidentiality b) Integrity c)...
-
A memory management technique that takes into consideration the programmer's view to the memory and how the programmer divides the process is called O a. Lazy swapping O b. Swapping O c. Caching O d....
-
a. Suppose in relation schema R(acc,name.branch,sal,loc) has the following functional dependencies: [(6) {{acc,loc)-nameB loc-sal; acc--branch). Find out the candidate key(s) and super key(s) which...
-
For the vector whose polar components are (Vr = 1, Vθ = 0), compute in polars all components of the second covariant derivative Vα;μ;ν. To find...
-
A crate of books is to be put on a truck by rolling it up an incline of angle using a dolly. The total mass of the crate and the dolly is m. Assume that rolling the dolly up the incline is the same...
-
A certain radioactive nuclide has a half-life of 200.0 s. A sample containing just this one radioactive nuclide has an initial activity of 80,000.0 s1. (a) What is the activity 600.0 s later? (b) How...
-
According to Figure 30.2, higher energies correspond with times that are closer to the origin of the universe, so particle accelerators at higher energies probe conditions that existed shortly after...
-
Verify the color SU(3) representations for combinations of three or fewer quarks and antiquarks given in Eq. (19.28). Data from Eq. 19.28 qq=303=108 qq 3 3 603, 999 3 3 3 = 36315, qqq 3 3 3 1088 10,
-
Prove that Eq. (19.34) gives the simplest multi-gluon and gluon-quark states that contain an \(\mathrm{SU}(3)\) color singlet in the decomposition. Data from Eq. 19.34 (GG)1: (88)1 (Gqq) : [8 (383)8]...
-
A textile manufacturer is concerned about the strength of cotton yarn. In order to nd out whether fiber length is an important factor in determining the strength of yarn, the quality control manager...

Study smarter with the SolutionInn App