Question: In addition to artifacts already found on the suspect computer, where else might an investigator find information from external sources regarding what that computer had
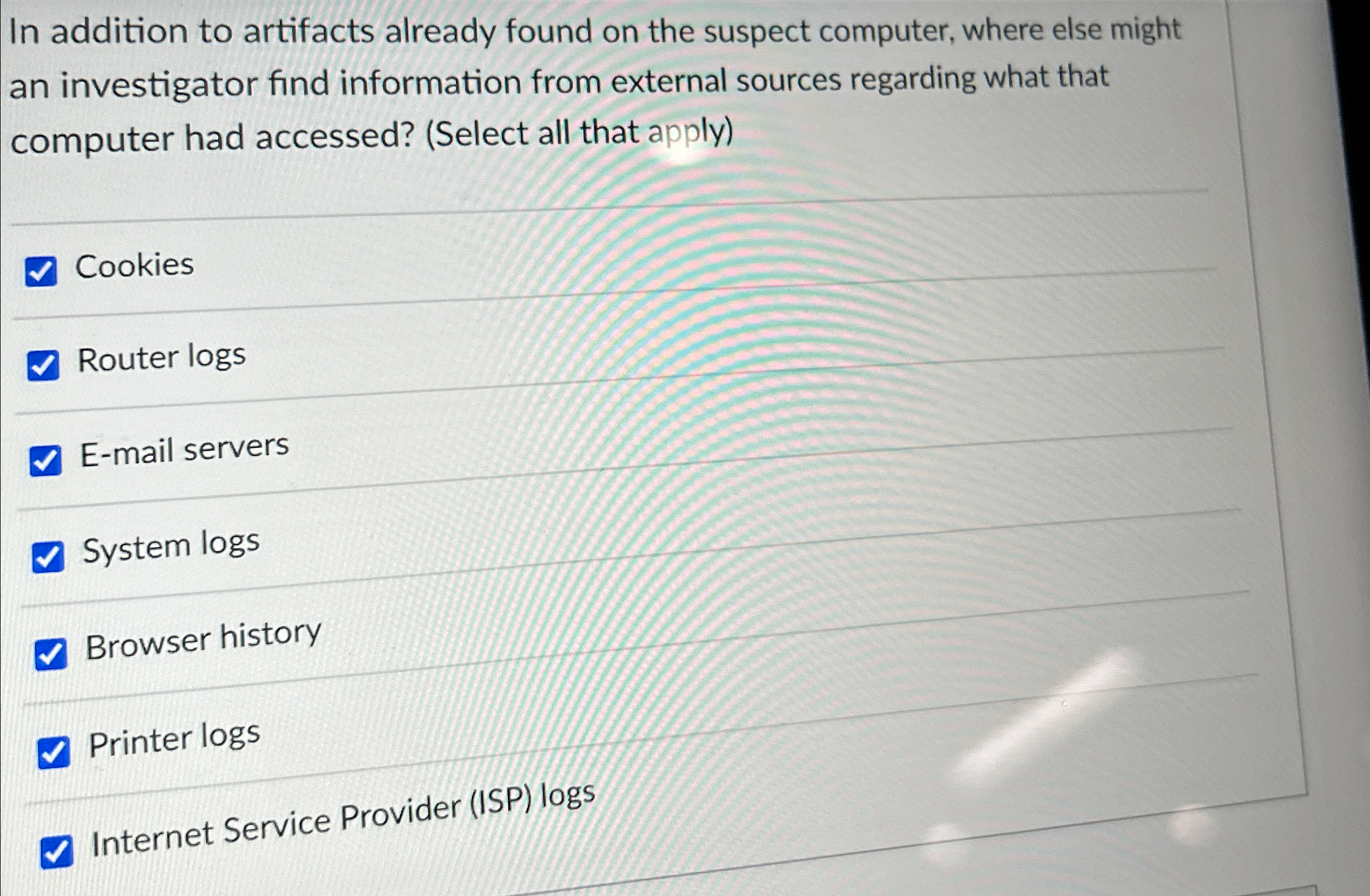
In addition to artifacts already found on the suspect computer, where else might an investigator find information from external sources regarding what that computer had accessed? Select all that apply
Cookies
Router logs
Email servers
System logs
Browser history
Printer logs
Internet Service Provider ISP logs
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


