Question: In class, we discussed challenge/response-based authentication using timestamp: Alice rightarrow Bob: I am Alice, E_k(timestamp) This protocol assumes that Alice and Bob already have a
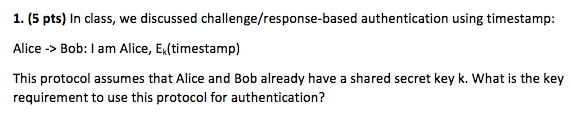
In class, we discussed challenge/response-based authentication using timestamp: Alice rightarrow Bob: I am Alice, E_k(timestamp) This protocol assumes that Alice and Bob already have a shared secret key k. What is the key requirement to use this protocol for authentication
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


