Question: In which of the following methods does an attacker try every possible password or key in a methodical order until the attacker finds the right
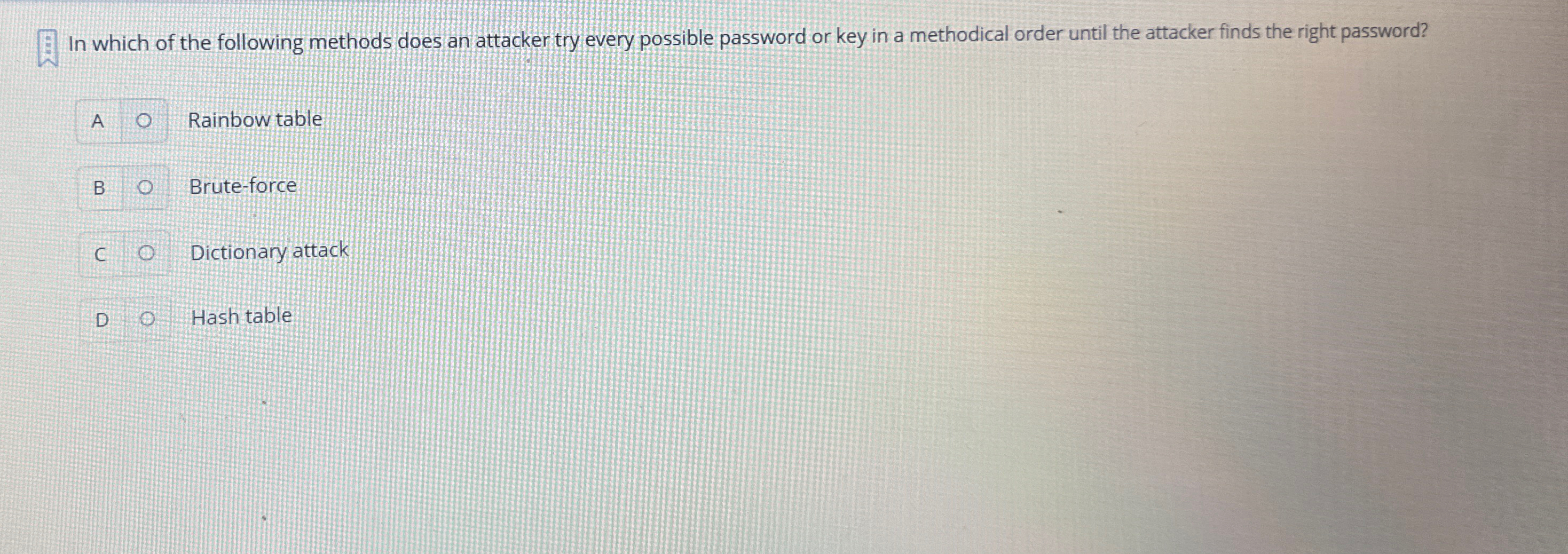
In which of the following methods does an attacker try every possible password or key in a methodical order until the attacker finds the right password?
A Rainbow table
B Bruteforce
C Dictionary attack
D Hash table
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


