Question: Information Structures and Algorithms (a) Take an at first void hash table with five openings, with hash work h(x) = x mod 5, and with
Information Structures and Algorithms (a) Take an at first void hash table with five openings, with hash work h(x) = x mod 5, and with impacts settled by tying. Draw a sketch of what happens while embedding the accompanying succession of keys into it: 35, 2, 18, 6, 3, 10, 8, 5. [You are not mentioned to draw the moderate stages as discrete figures, nor to show every one of the fields of every section in detail.] [3 marks] (b) Repeat section (a) yet with the accompanying three changes: the hash table currently has ten openings, the hash work is h(x) = x mod 10, and impacts are settled by direct testing. [3 marks] (c) Imagine a hash table execution where impacts are settled by tying yet, every one of the information stays inside the spaces of the first table. All passages not containing key-esteem matches are set apart with a Boolean banner and connected together into a free rundown. (I) Give clear clarifications on the most proficient method to execute the set(key, esteem) technique in anticipated steady time, featuring striking focuses and utilizing significant level pseudocode where suitable. Utilize doubly-connected records in the event that fundamental. [8 marks] (ii) Assume the hash table has 5 openings, is at first vacant and utilizes the hash work h(x) = x mod 5. Draw five charts of the hash table addressing the at first void state and afterward the table after the inclusion of every one of the accompanying key-esteem matches: (2, A), (2, C), (12, T), (5, Z). In the last graph, draw every one of the fields and pointers of all the sections. [6 marks] 10 CST.2008.10.11 10 Operating System Foundations (a) Assume a 32-digit design with equipment support for paging, as a interpretation lookaside cushion (TLB), yet no equipment support for division. Accept that the TLB is shared as opposed to flushed on process exchanging and that the it are supporting "delicate" portions to work framework fashioners. (I) notwithstanding page number and page base, what fields would you anticipate to find in each TLB enlist? How might each of these be utilized? [4 marks] (ii) What fields could you hope to find in an interaction page table? How might every one of these fields be utilized? [6 marks] (b) (I) Outline the capacity of a planning gadget. [2 marks] (ii) Why are clocks fundamental in multiprogramming working frameworks?
(a) Outline the utilization of enum in Java programs and clear up any likenesses for and any distinctions from a Java class. [6 marks] The accompanying piece of code shows an early endeavor to compose and test a Java program to reenact the paper-scissors-stone game. In the technique fundamental() each of the identifiers an and b is allocated one of the things, paper, scissors or stone and the printf() technique then says whether the main beats, draws with or loses against the second. [The decide is that paper beats stone, scissors beat paper and stone beats scissors.] public class Game { public static void main(String[] args) { Thing a = allocateItem(); Thing b = allocateItem(); int res = a.versus(b); System.out.printf("%s %s %s%n", a, res>0 ? "beats" : res==0 ? "draws with" : "loses against", b); } private static Item allocateItem() { ... } } enum Item { PAPER... The three prospects PAPER, SCISSORS and STONE are proclaimed in enum Item along with a constructor, the technique versus() and any vital extra information fields. (b) Using the strategy Math.random() or in any case, give a body to the technique allocateItem() with the end goal that the technique returns an Item PAPER, SCISSORS or STONE equiprobably. [6 marks] (c) Complete the enum Item with the goal that the assertions in the strategy fundamental() work as planned.
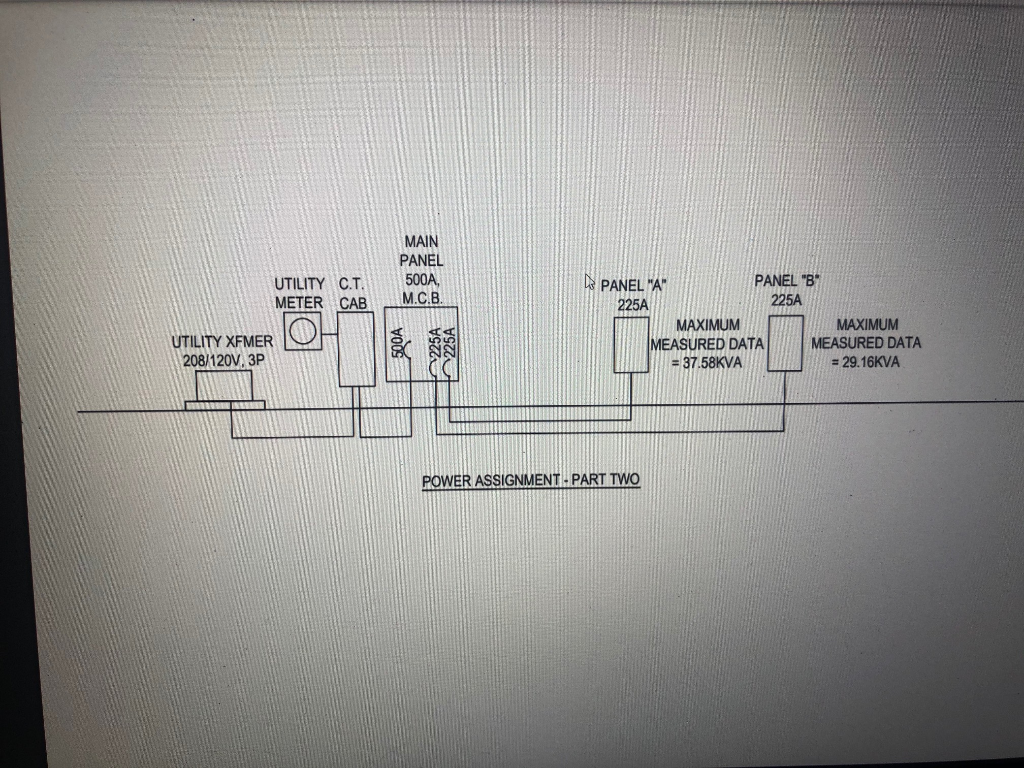
UTILITY C.T. sh UTILITY XFMER 208/120V, 3P MAIN PANEL 500A, METER CAB M.C.B. PANEL "A" 225A POWER ASSIGNMENT-PART TWO PANEL "B" 225A MAXIMUM MEASURED DATA = 37.58KVA MAXIMUM MEASURED DATA = 29.16KVA
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


