Instructions: Justifications and explanations for answers are always required, and answers without them may not get...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
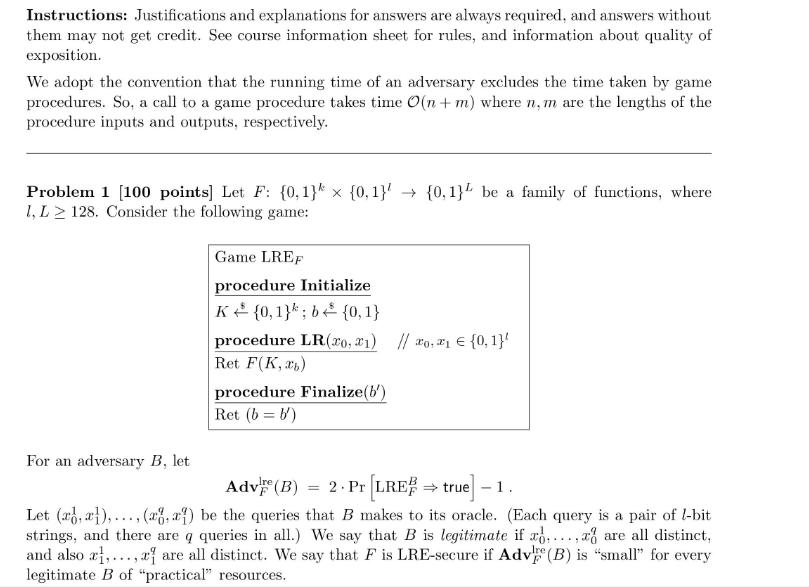
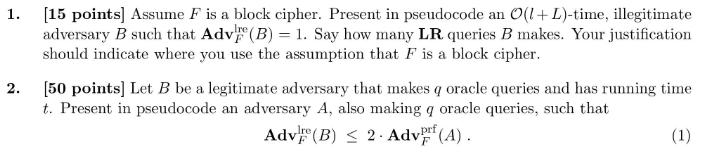
Instructions: Justifications and explanations for answers are always required, and answers without them may not get credit. See course information sheet for rules, and information about quality of exposition. We adopt the convention that the running time of an adversary excludes the time taken by game procedures. So, a call to a game procedure takes time O(n + m) where n. m are the lengths of the procedure inputs and outputs, respectively. Problem 1 [100 points] Let F: {0,1} {0,1} {0,1} be a family of functions, where 1, L2 128. Consider the following game: For an adversary B, let Game LREF procedure Initialize K (0,1); b {0,1} procedure LR(20, 1) // 0,1 {0,1}' Ret F(K, b) procedure Finalize(b') Ret (b= b) Adv (B) = 2. Pr [LRE true] - 1. Let (x,x),(a, a) be the queries that B makes to its oracle. (Each query is a pair of l-bit strings, and there are q queries in all.) We say that B is legitimate if ..... are all distinct, and also x,..., are all distinct. We say that F is LRE-secure if Adv (B) is "small" for every legitimate B of "practical" resources. Ire 1. [15 points] Assume F is a block cipher. Present in pseudocode an O(l+L)-time, illegitimate adversary B such that Adv (B) = 1. Say how many LR queries B makes. Your justification should indicate where you use the assumption that F is a block cipher. 2. [50 points] Let B be a legitimate adversary that makes q oracle queries and has running time t. Present in pseudocode an adversary A, also making q oracle queries, such that Adv (B) 2. Adv (A). F (1) 3. 4. The running time of A, which you should state, should be close to t, and you should prove that Eq. (1) holds. [5 points] Explain why (2.) shows that if F is a secure PRF then it is LRE-secure. [30 points] Is the converse true? Namely, if F is LRE-secure, then is it a secure PRF? Answer YES or NO. If you say YES, justify this via a reduction-based proof, and, if NO, via a counterexample. (The latter means a particular family of functions F which you prove is LRE-secure but which you show via an attack is not PRF-secure.) Instructions: Justifications and explanations for answers are always required, and answers without them may not get credit. See course information sheet for rules, and information about quality of exposition. We adopt the convention that the running time of an adversary excludes the time taken by game procedures. So, a call to a game procedure takes time O(n + m) where n. m are the lengths of the procedure inputs and outputs, respectively. Problem 1 [100 points] Let F: {0,1} {0,1} {0,1} be a family of functions, where 1, L2 128. Consider the following game: For an adversary B, let Game LREF procedure Initialize K (0,1); b {0,1} procedure LR(20, 1) // 0,1 {0,1}' Ret F(K, b) procedure Finalize(b') Ret (b= b) Adv (B) = 2. Pr [LRE true] - 1. Let (x,x),(a, a) be the queries that B makes to its oracle. (Each query is a pair of l-bit strings, and there are q queries in all.) We say that B is legitimate if ..... are all distinct, and also x,..., are all distinct. We say that F is LRE-secure if Adv (B) is "small" for every legitimate B of "practical" resources. Ire 1. [15 points] Assume F is a block cipher. Present in pseudocode an O(l+L)-time, illegitimate adversary B such that Adv (B) = 1. Say how many LR queries B makes. Your justification should indicate where you use the assumption that F is a block cipher. 2. [50 points] Let B be a legitimate adversary that makes q oracle queries and has running time t. Present in pseudocode an adversary A, also making q oracle queries, such that Adv (B) 2. Adv (A). F (1) 3. 4. The running time of A, which you should state, should be close to t, and you should prove that Eq. (1) holds. [5 points] Explain why (2.) shows that if F is a secure PRF then it is LRE-secure. [30 points] Is the converse true? Namely, if F is LRE-secure, then is it a secure PRF? Answer YES or NO. If you say YES, justify this via a reduction-based proof, and, if NO, via a counterexample. (The latter means a particular family of functions F which you prove is LRE-secure but which you show via an attack is not PRF-secure.)
Expert Answer:

Related Book For 

Income Tax Fundamentals 2013
ISBN: 9781285586618
31st Edition
Authors: Gerald E. Whittenburg, Martha Altus Buller, Steven L Gill
Posted Date:
Students also viewed these algorithms questions
-
Determine the minimum expression for each K map in Figure 4-70. Pay particular attention to step 5 for the map in (a). Figure 4-70 AB AB CD CD 1 AB 1 0 0 S 1 1 0 0 (a)* CD 1 0 0 1 CD 1 0 1 1 AB 1 ...
-
Let A, B be sets. Define: (a) the Cartesian product (A B) (b) the set of relations R between A and B (c) the identity relation A on the set A [3 marks] Suppose S, T are relations between A and B, and...
-
1. If an industry is formed by six companies. Four companies have sales of $ 10 each, and two companies have sales of $ 5 each. a. What is the concentration ratio of four companies for this industry?...
-
The electron in a certain hydrogen atom has an angular momentum of 8.948 x 10-34 J.s. What is the largest possible magnitude for the z component of the angular momentum of this electron? For...
-
(a) In Figure 3 . 3, are the \(x\) components of the velocity represented by the \(x(t)\) curves positive or negative? (b) Are the speeds increasing or decreasing? (c) Are the \(x\) components of...
-
Catastrophe Management Solutions is a customer service support center for insurance companies. In 2010, the company put out a help wanted ad for customer service representatives who had basic...
-
Cougar, Inc., is a calendar year S corporation. Cougars Form 1120S shows nonseparately stated ordinary income of $80,000 for the year. Johnny owns 40% of the Cougar stock throughout the year. The...
-
Mr. Mutwiri opened a business in Meru town at the beginning of the year. During the first month of operation the following transactions were completed. 2014. January 1 Deposited sh 20,000 in the bank...
-
In most countries, personal identification information such as name and surname are considered immutable and often require legal proceedings to change. On the other hand, information like height,...
-
Find the indefinite integral. Check your answer by differentiation. [2x(x +3) dx = +C
-
1. (1 point) Draw the diagram for a multi-class mapper function with LDA, Perceptron and Logistic Regression classifiers, and write down their respective objective functions. Make sure to properly...
-
Discuss and explain the 2020 variance of the industries. $25,000,000,000 $20,000,000,000 $15,000,000,000 $10,000,000,000 $5,000,000,000 8 $0 Jan-20 Feb-20 Total Performance of all of Colorado...
-
Let F be a field. Two variations of the ring of polynomial over F are the ring of formal power series F[[X]] and the ring of formal Laurent series F((X)) defined as follows: and F[[X]] = {a0 + aX +...
-
d) What are the differences between Static RAM and Dynamic RAM? Explain in transistor level RAM cell circuit, Addressing scheme, Speed etc. Explain major types of DRAMs including special...
-
Explain the difference between the variable-costing approach to the absorption-costing approach. short answer please
-
D Which of the following is considered part of the Controlling activity of managerial accounting? O Choosing to purchase raw materials from one supplier versus another O Choosing the allocation base...
-
Russell (age 50) and Linda (age 45) Long have brought you the following information regarding their income and expenses for the current year. Russell owns and operates a landscaping business called...
-
Indicate whether each of the items listed below would be included (I) in or excluded (E) from gross income for the 2012 tax year. ________a. Welfare payments ________b. Commissions ________c. Hobby...
-
Matthew borrows $250,000 to invest in bonds. During 2012, his interest on the loan is $30,000. Matthew's interest income from the bonds is $10,000. This is Matthew's only investment income. a....
-
True or False: Build-Operate-Transfer (BOT) makes use of a public-private partnership.
-
Do an Internet search on "build operate transfer." Identify a BOT project, preferably from your home continent (e.g., AF, AS, EU, Pacific, NA, SA), and copy a small portion of what you find (a page...
-
Using an Internet-based search on 'build operate transfer," find an additional definition from a source other than used in Section 14.2. Copy and paste it, as well as any graphics, examples,...

Study smarter with the SolutionInn App


