Question: int getBit(int bn, unsigned long val): extracts a single bit value at position on from the target variable val, and returns an integer 0
 = 0 && bn <64); if (1UL <" width="1149" height="1127">
= 0 && bn <64); if (1UL <" width="1149" height="1127">
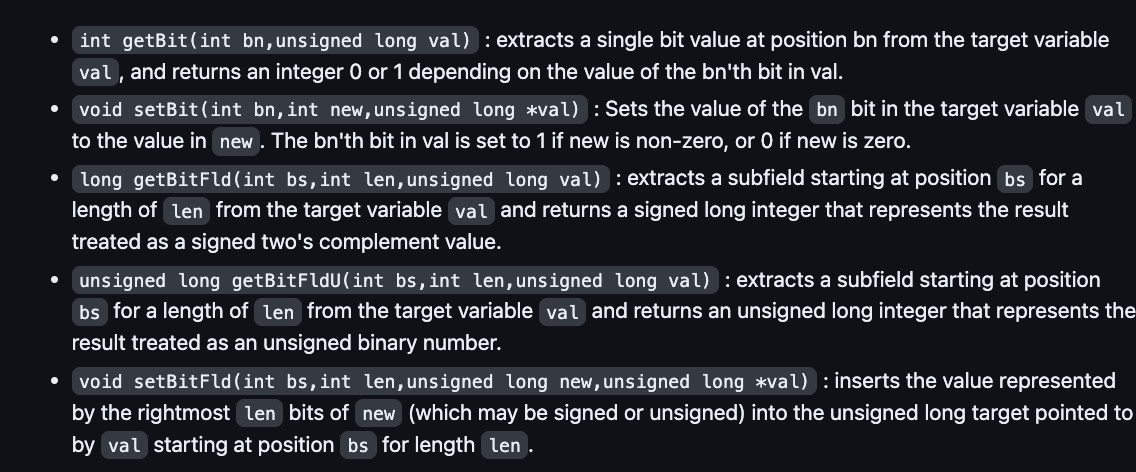
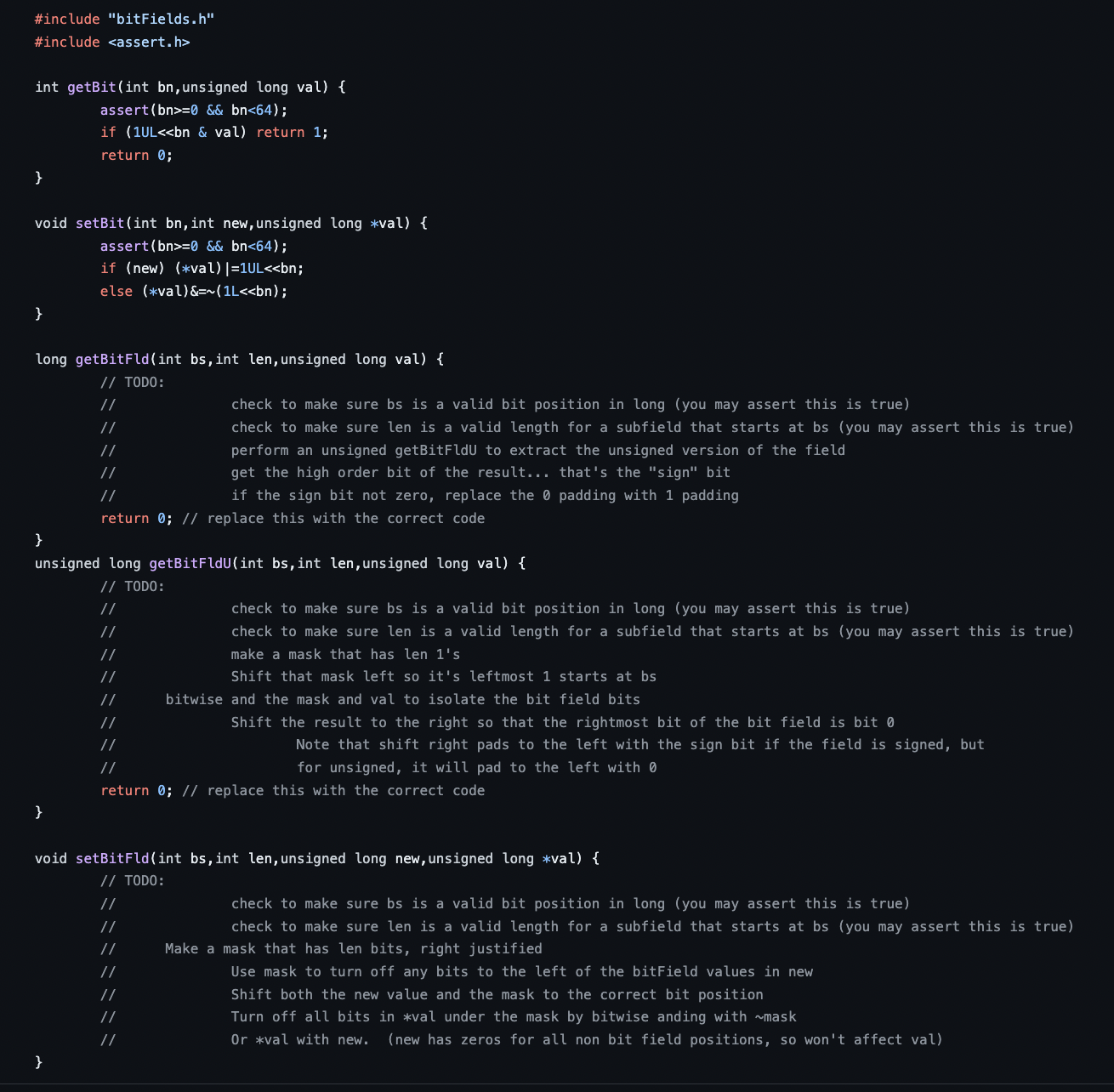
int getBit(int bn, unsigned long val): extracts a single bit value at position on from the target variable val, and returns an integer 0 or 1 depending on the value of the bn'th bit in val. void setBit(int bn, int new, unsigned long *val) : Sets the value of the bn bit in the target variable val to the value in new. The bn'th bit in val is set to 1 if new is non-zero, or 0 if new is zero. long getBit Fld (int bs,int len, unsigned long val): extracts a subfield starting at position bs for a length of len from the target variable val and returns a signed long integer that represents the result treated as a signed two's complement value. unsigned long getBitFldU(int bs, int len, unsigned long val): extracts a subfield starting at position bs for a length of len from the target variable val and returns an unsigned long integer that represents the result treated as an unsigned binary number. void setBitFld (int bs, int len, unsigned long new, unsigned long *val): inserts the value represented by the rightmost len bits of new (which may be signed or unsigned) into the unsigned long target pointed to by val starting at position bs for length len . #include "bitFields.h" #include int getBit(int bn, unsigned long val) { assert (bn>= 0 && bn
Step by Step Solution
3.35 Rating (167 Votes )
There are 3 Steps involved in it
It seems that you have provided images that contain descriptions and implementations of bit ... View full answer

Get step-by-step solutions from verified subject matter experts


