Question: issue. Answer: T/F 21. Unauthorized hardware and programs interfere with automated maintenance programs for 22. We will most certainly see a fall in the use
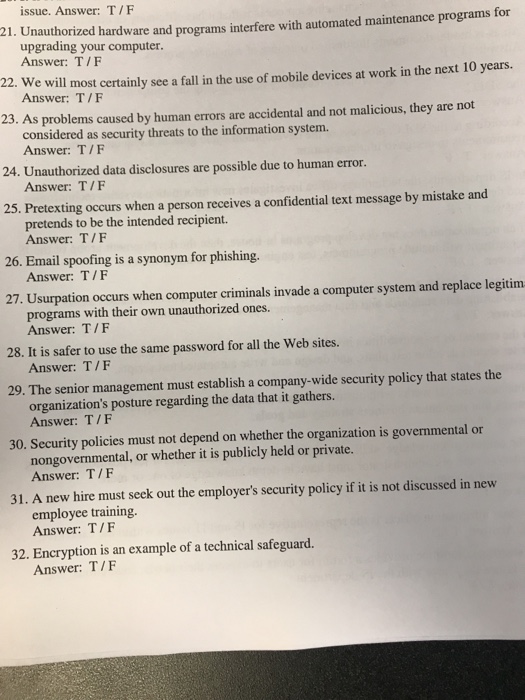
issue. Answer: T/F 21. Unauthorized hardware and programs interfere with automated maintenance programs for 22. We will most certainly see a fall in the use of mobile devices at work in the next 10 years. 23. As problems caused by human errors are accidental and not malicious, they are not 24. Unauthorized data disclosures are possible due to human error. 25. Pretexting occurs when a person receives a confidential text message by mistake and 26. Email spoofing is a synonym for phishing. 27. Usurpation occurs when computer criminals invade a computer system and replace legitinm upgrading your computer Answer: T/F Answer: T/F considered as security threats to the information system. Answer: T/F Answer: T/F pretends to be the intended recipient. Answer: T/F Answer: T/F programs with their own unauthorized ones. Answer: T/F 28. It is safer to use the same password for all the Web sites. Answer: T/F 29. The senior management must establish a company-wide security policy that states the organization's posture regarding the data that it gathers. Answer: T/F 30. Security policies must not depend on whether the organization is governmental or nongovernmental, or whether it is publicly held or private. Answer: T/F 31. A new hire must seek out the employer's security policy if it is not discussed in new employee training. Answer: T/F 32. Encryption is an example of a technical safeguard. Answer: T/F
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


