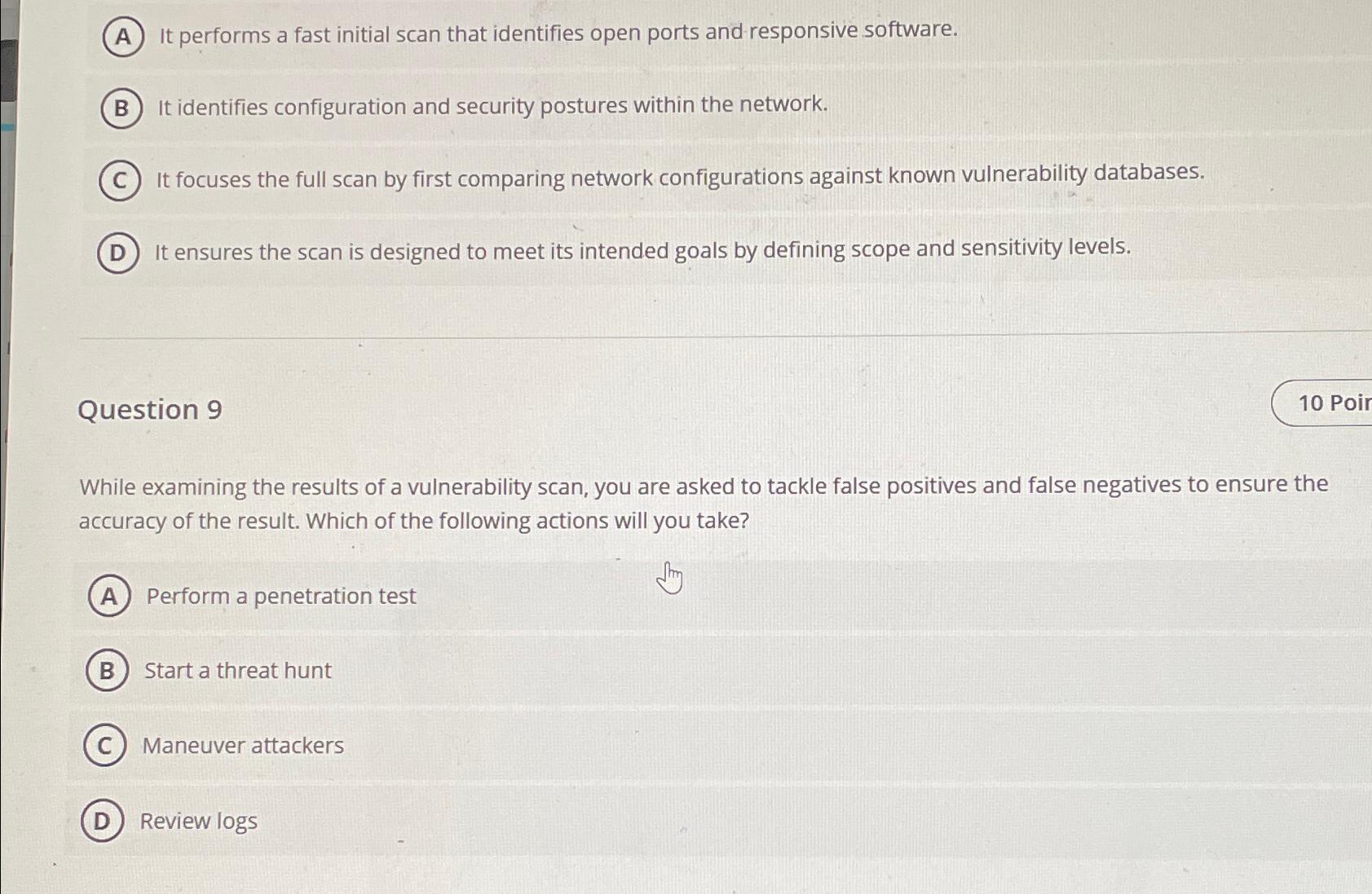
Question: It performs a fast initial scan that identifies open ports and responsive software. It identifies configuration and security postures within the network. It focuses the
It performs a fast initial scan that identifies open ports and responsive software.
It identifies configuration and security postures within the network.
It focuses the full scan by first comparing network configurations against known vulnerability databases.
It ensures the scan is designed to meet its intended goals by defining scope and sensitivity levels.
Question
Poir
While examining the results of a vulnerability scan, you are asked to tackle false positives and false negatives to ensure the accuracy of the result. Which of the following actions will you take?
Perform a penetration test
Start a threat hunt
Maneuver attackers
Review logs
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


