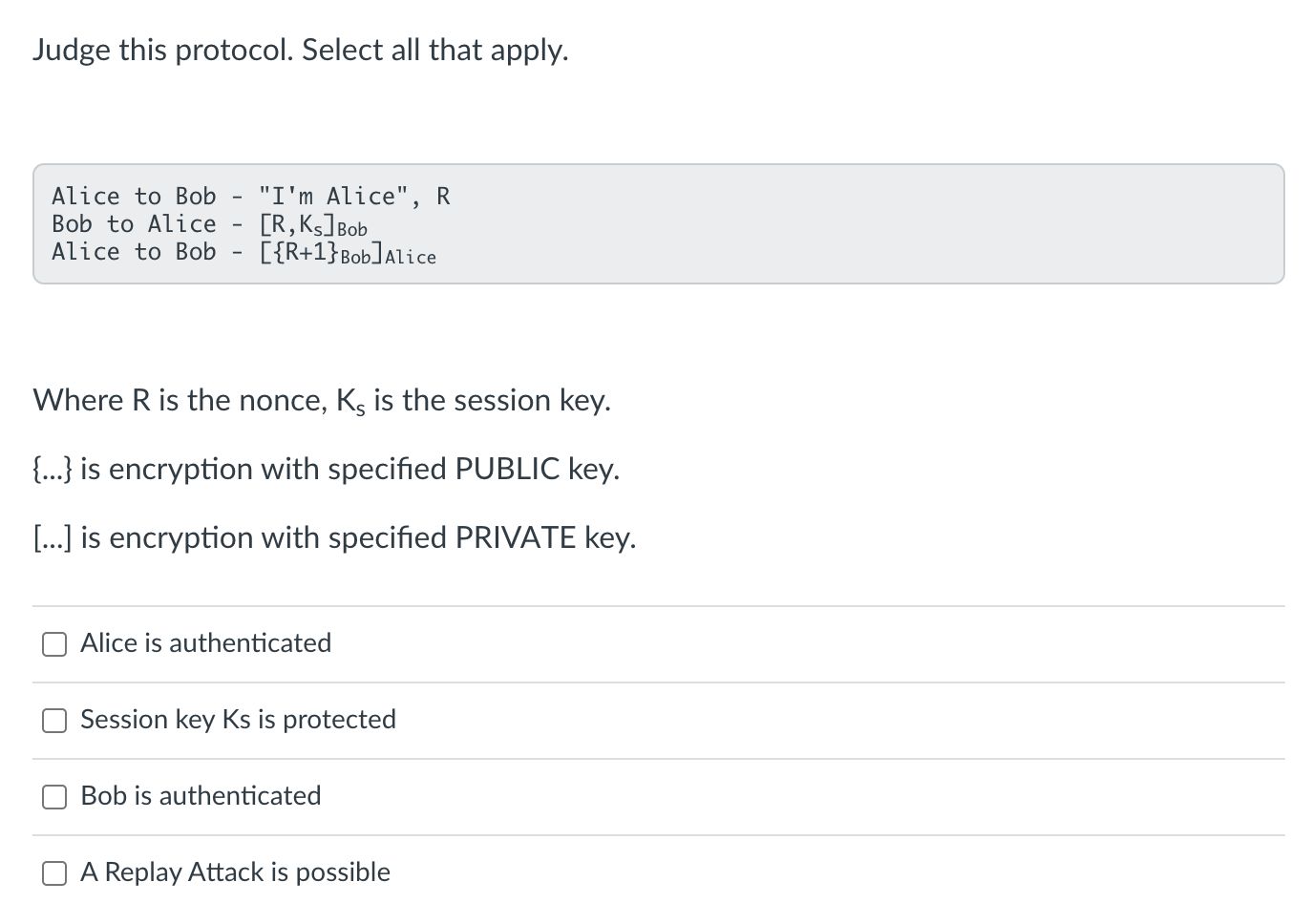
Question: Judge this protocol. Select all that apply. Alice t o Bob - I'mAlice, R Bob t o Alice - [ R , K s ]
Judge this protocol. Select all that apply.
Alice Bob I'mAlice,
Bob Alice
Alice Bob
Where R is the nonce, is the session key.
is encryption with specified PUBLIC key.
is encryption with specified PRIVATE key.
Alice is authenticated
Session key Ks is protected
Bob is authenticated
A Replay Attack is possible
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


