Question: Question 2: Explaining how the attack (as shown in the 2nd Figure) to the key exchange protocol (as shown in the 1st Figure) works. (34
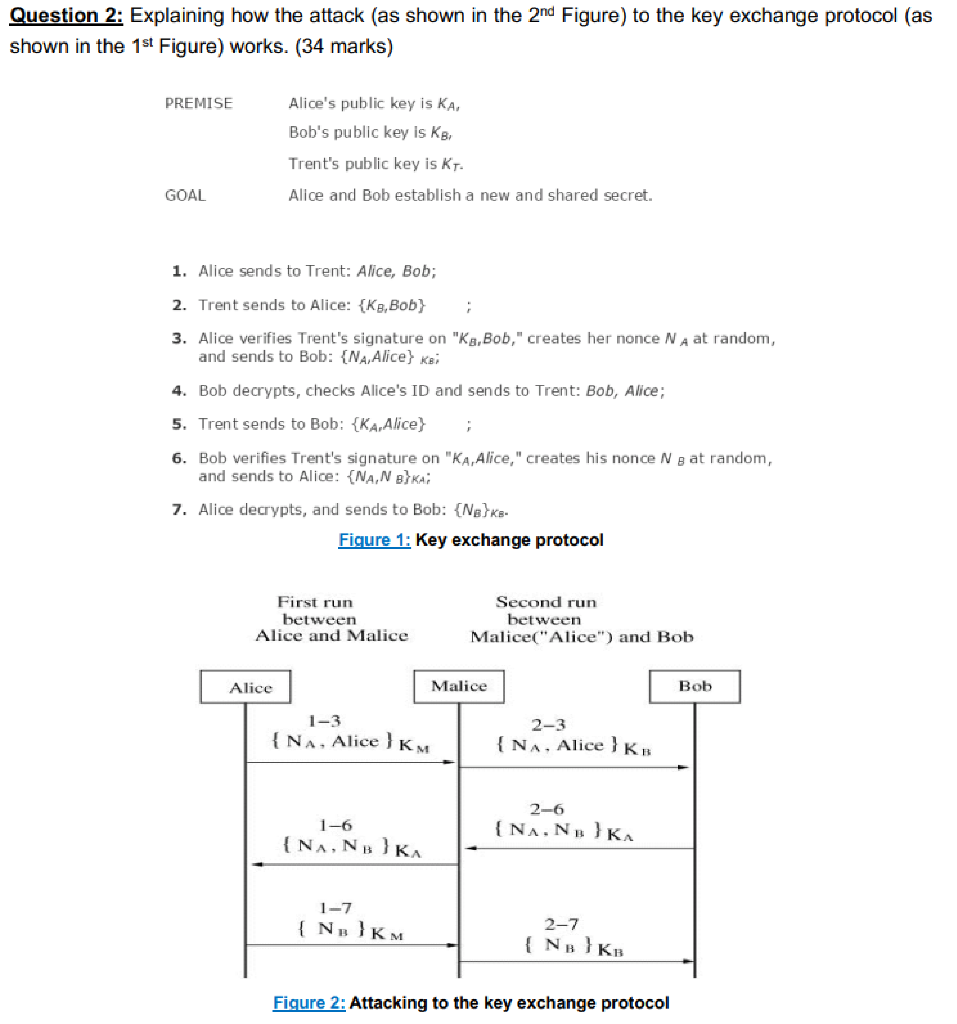
Question 2: Explaining how the attack (as shown in the 2nd Figure) to the key exchange protocol (as shown in the 1st Figure) works. (34 marks) PREMISE Alice's public key is KA, Bob's public key is KB, Trent's public key is kr. Alice and Bob establish a new and shared secret. GOAL 1. Alice sends to Trent: Alice, Bob; 2. Trent sends to Alice: {K8, Bob) 3. Alice verifies Trent's signature on "K,Bob,"creates her nonce NA at random, and sends to Bob: {NA, Alice) Kai 4. Bob decrypts, checks Alice's ID and sends to Trent: Bob, Alice; 5. Trent sends to Bob: {KA, Alice) 6. Bob verifies Trent's signature on "KA, Alice," creates his nonce Ng at random, and sends to Alice: {NAN BKA 7. Alice decrypts, and sends to Bob: {Nek- Figure 1: Key exchange protocol First run between Alice and Malice Second run between Malice("Alice") and Bob Alice Malice Bob 1-3 {NA, Alice } KM 2-3 {NA, Alice } KB 1-6 { NNBK 2-6 {NANKA 1-7 {N} KM 2-7 { NB) KB Figure 2: Attacking to the key exchange protocol
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


