Question: Layering is a common approach to tackling large problems in Computers. There are a few common ways of dividing responsibilities on the Internet. One
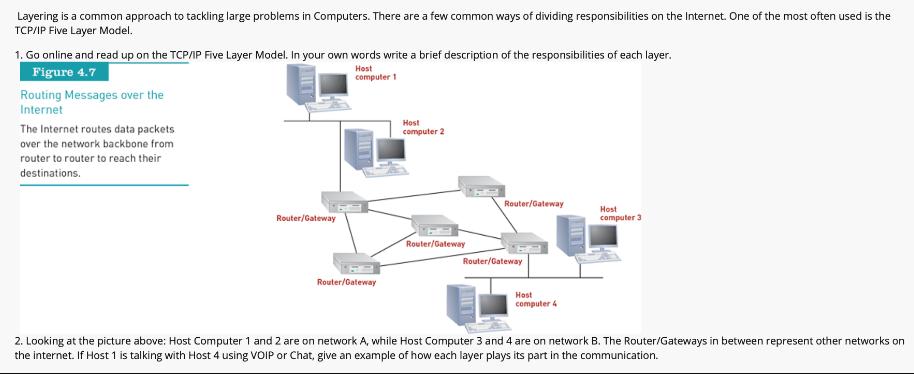
Layering is a common approach to tackling large problems in Computers. There are a few common ways of dividing responsibilities on the Internet. One of the most often used is the TCP/IP Five Layer Model. 1. Go online and read up on the TCP/IP Five Layer Model. In your own words write a brief description of the responsibilities of each layer. Host computer 1 Figure 4.7 Routing Messages over the Internet The Internet routes data packets over the network backbone from router to router to reach their destinations. Router/Gateway Router/Gateway Host computer 2 Router/Gateway Router/Gateway Router/Gateway Host computer 4 Host computer 3 2. Looking at the picture above: Host Computer 1 and 2 are on network A, while Host Computer 3 and 4 are on network B. The Router/Gateways in between represent other networks on the internet. If Host 1 is talking with Host 4 using VOIP or Chat, give an example of how each layer plays its part in the communication.
Step by Step Solution
3.41 Rating (154 Votes )
There are 3 Steps involved in it
Question 1 The TCPIP FiveLayer Model is a conceptual model that describes how data is communicated over a network It is a layered architecture which m... View full answer

Get step-by-step solutions from verified subject matter experts


