Question: Let us consider the following program, where the copy function is a (naive) attempt to protect the execution against buffer overflow vulnerabilities. Let us consider
Let us consider the following program, where the copy function is a (naive) attempt to protect the execution against buffer overflow vulnerabilities.
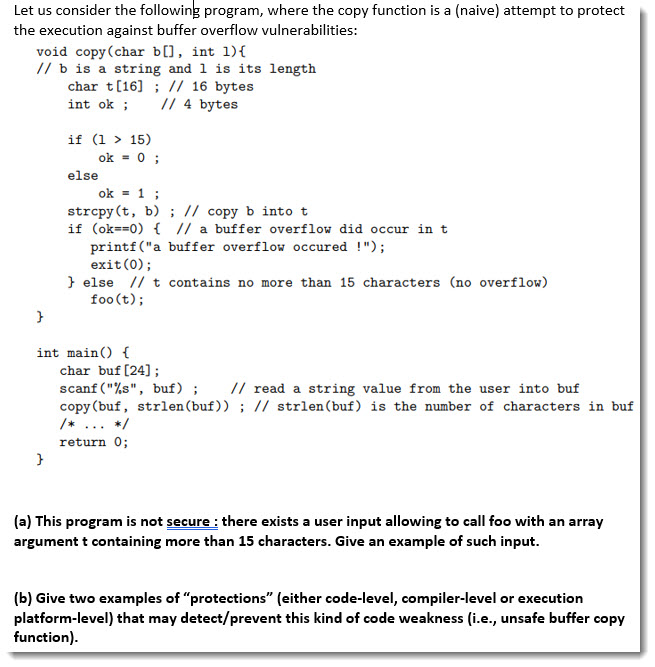
Let us consider the following program, where the copy function is a (naive) attempt to protect the execution against buffer overflow vulnerabilities: void copy (char b[], int 1){ // b is a string and 1 is its length char t(16) ; // 16 bytes int ok ; 1/4 bytes if (1 > 15) ok = 0; else ok = 1; strcpy(t, b); // copy b into t if (ok==0) { // a buffer overflow did occur in t printf ("a buffer overflow occured !"); exit(0); } else 11 t contains no more than 15 characters (no overflow) foo(t); int main() { char buf [24] ; scanf("%s", buf); // read a string value from the user into buf copy (buf, strlen(buf)); // strlen(buf) is the number of characters in buf return 0; (a) This program is not secure : there exists a user input allowing to call foo with an array argument t containing more than 15 characters. Give an example of such input. (b) Give two examples of "protections" (either code-level, compiler-level or execution platform-level) that may detect/prevent this kind of code weakness (i.e., unsafe buffer copy function)
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


