Question: Long Answer Questions: Answer all the following questions: C1. Answer the following questions: C1.1: Classify the following scenario to their type of social engineering attack
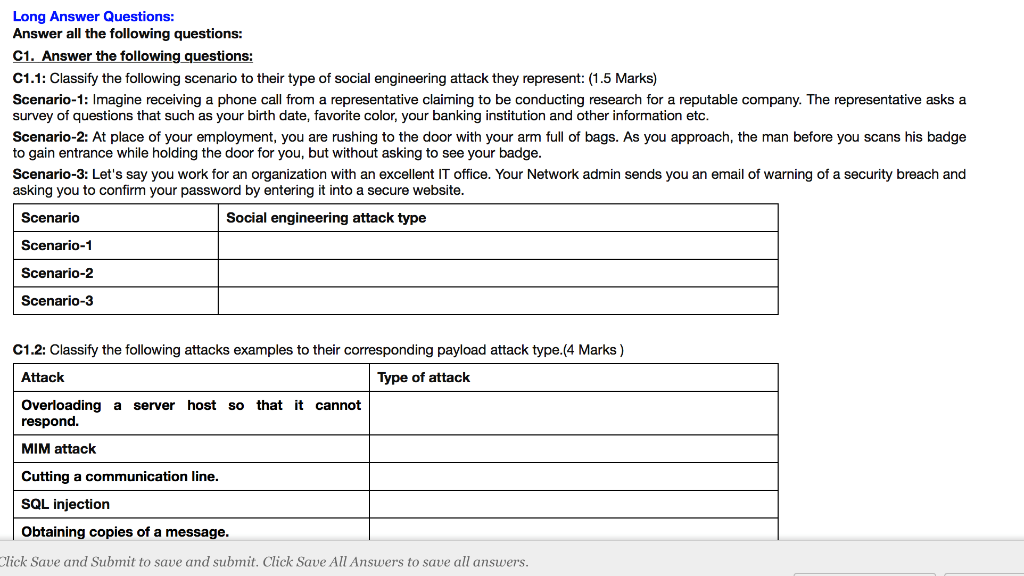
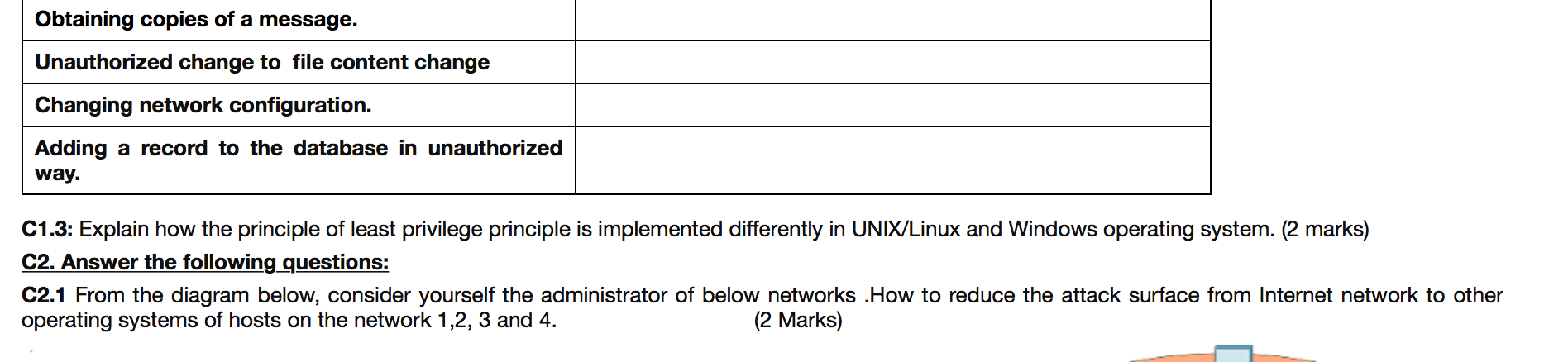
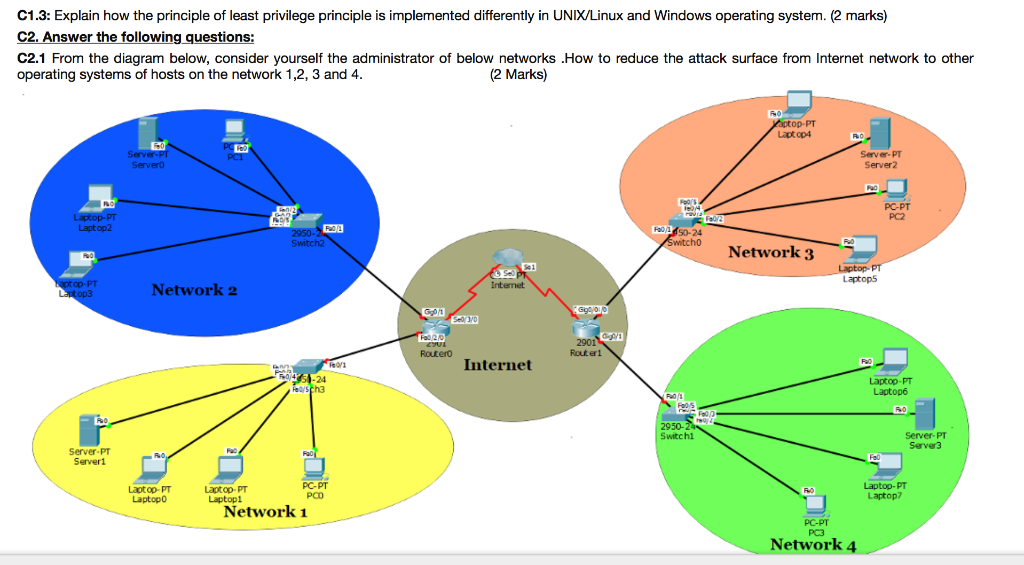
Long Answer Questions: Answer all the following questions: C1. Answer the following questions: C1.1: Classify the following scenario to their type of social engineering attack they represent: (1.5 Marks) Scenario-1: Imagine receiving a phone call from a representative claiming to be conducting research for a reputable company. The representative asks a survey of questions that such as your birth date, favorite color, your banking institution and other information etc. Scenario-2: At place of your employment, you are rushing to the door with your arm full of bags. As you approach, the man before you scans his badge to gain entrance while holding the door for you, but without asking to see your badge. Scenario-3: Let's say you work for an organization with an excellent IT office. Your Network admin sends you an email of warning of a security breach and asking you to confirm your password by entering it into a secure website. Scenario Social engineering attack type Scenario-1 Scenario-2 Scenario-3 C1.2: Classify the following attacks examples to their corresponding payload attack type (4 Marks) Attack Type of attack Overloading a server host so that it cannot respond. MIM attack Cutting a communication line. SQL injection Obtaining copies of a message. Click Save and Submit to save and submit. Click Save All Answers to save all answers. Obtaining copies of a message. Unauthorized change to file content change Changing network configuration. Adding a record to the database in unauthorized way. C1.3: Explain how the principle of least privilege principle is implemented differently in UNIX/Linux and Windows operating system. (2 marks) C2. Answer the following questions: C2.1 From the diagram below, consider yourself the administrator of below networks .How to reduce the attack surface from Internet network to other operating systems of hosts on the network 1,2, 3 and 4. (2 Marks) C1.3: Explain how the principle of least privilege principle is implemented differently in UNIX/Linux and Windows operating system. (2 marks) C2. Answer the following questions: C2.1 From the diagram below, consider yourself the administrator of below networks .How to reduce the attack surface from Internet network to other operating systems of hosts on the network 1,2, 3 and 4. (2 Marks) yaptop.PT Laptop4 RO Server PT Server Server.PT Server2 RO Laptop.PT Laptop2 POV PC-PT PC2 Fala 2950-2 Switch 50-24 Switcho FO POO Network 3 Laptop-PT Laptops Laptop.PT Laptop3 Network 2 Internet COU G010 Sell3/0 Fa 20 Routero 2901 Router1 Internet R01 PA 30123-24 Fellsch Laptop.PT Laptop R01 FO 10 2950-24 Switchi Server PT Server Server.PT Serveri PC-PT Laptop-PT Laptop Laptop-PT Laptopi Laptop-PT Laptop PCO Network 1 PC-PT PC3 Network 4
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


