Question: Match each social engineering description on the left with the appropriate attack type on the right. Keyboard Instructions Drag An attacker searches through an organization's
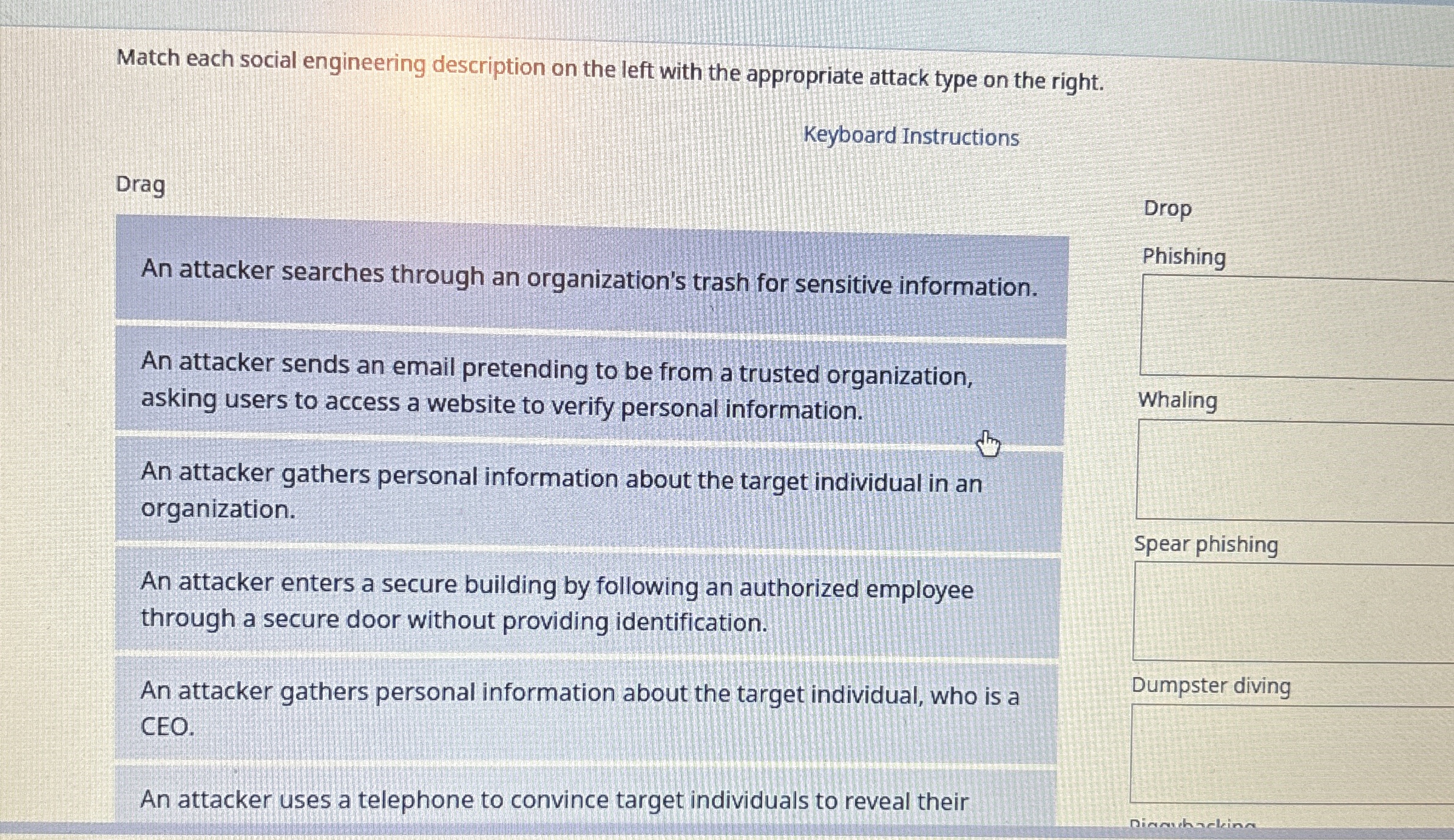
Match each social engineering description on the left with the appropriate attack type on the right.
Keyboard Instructions
Drag
An attacker searches through an organization's trash for sensitive information.
An attacker sends an email pretending to be from a trusted organization, asking users to access a website to verify personal information.
Drop
Phishing
An attacker gathers personal information about the target individual in an organization.
An attacker enters a secure building by following an authorized employee through a secure door without providing identification.
An attacker gathers personal information about the target individual, who is a CEO.
An attacker uses a telephone to convince target individuals to reveal their
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


