Question: Often a successful attack on an information system is due to poor system design or implementation. Once such a vulnerability is discovered, software developers quickly
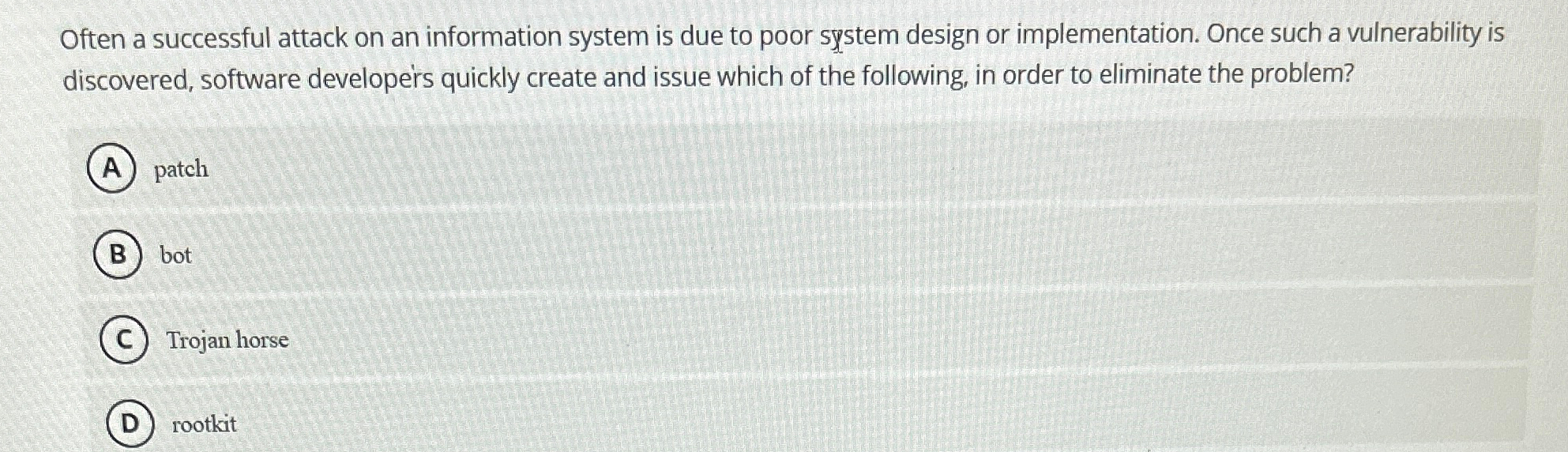
Often a successful attack on an information system is due to poor system design or implementation. Once such a vulnerability is discovered, software developers quickly create and issue which of the following, in order to eliminate the problem?
patch
bot
Trojan horse
rootkit
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


