Question: OS Vulnerabilities 1. Explain Windows vulnerabilities and Linux vulnerabilities. 2. Explain the Mac OS vulnerabilities, and vulnerabilities of mobile devices. 3. Explain the motives and
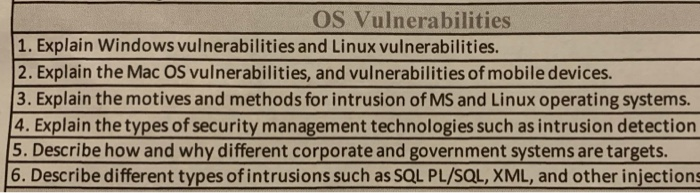
OS Vulnerabilities 1. Explain Windows vulnerabilities and Linux vulnerabilities. 2. Explain the Mac OS vulnerabilities, and vulnerabilities of mobile devices. 3. Explain the motives and methods for intrusion of MS and Linux operating systems. 4. Explain the types of security management technologies such as intrusion detection 5. Describe how and why different corporate and government systems are targets. 6. Describe different types of intrusions such as SQL PL/SQL, XML, and other injections
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


