Question: Part 3 ( Password Cracking ) ( 1 0 points ) Objective 1 SSH Dictionary Attack In this part, you are required to set up
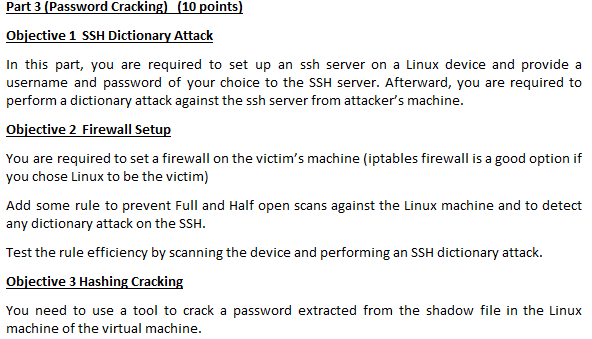
Part Password Cracking points
Objective SSH Dictionary Attack
In this part, you are required to set up an ssh server on a Linux device and provide a
username and password of your choice to the SSH server. Afterward, you are required to
perform a dictionary attack against the ssh server from attacker's machine.
Objective Firewall Setup
You are required to set a firewall on the victim's machine iptables firewall is a good option if
you chose Linux to be the victim
Add some rule to prevent Full and Half open scans against the Linux machine and to detect
any dictionary attack on the SSH
Test the rule efficiency by scanning the device and performing an SSH dictionary attack.
Objective Hashing Cracking
You need to use a tool to crack a password extracted from the shadow file in the Linux
machine of the virtual machine.
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


