Question: Please answer ALL the questions carefully. Thanks 62- A Security administrator needs to improve upon the current authentication system. The improved authentication system must require
Please answer ALL the questions carefully. Thanks
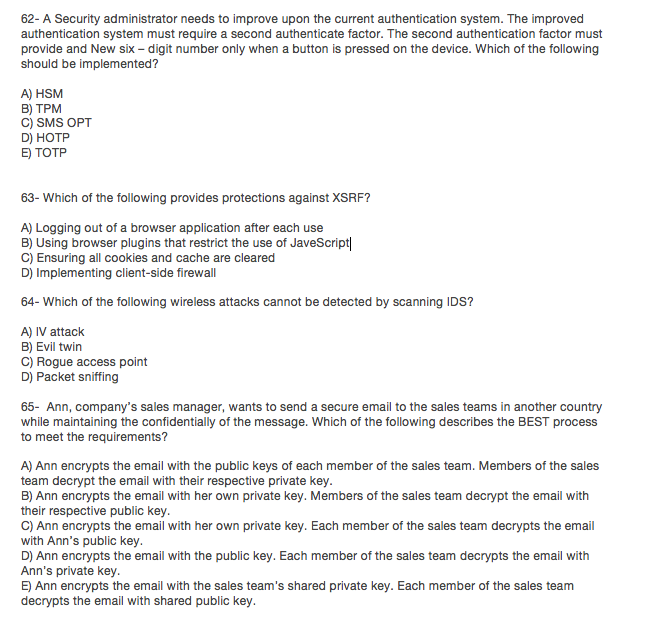
62- A Security administrator needs to improve upon the current authentication system. The improved authentication system must require a second authenticate factor. The second authentication factor must provide and New six - digit number only when a button is pressed on the device. Which of the following should be implemented? A) HSM B) TPM C) SMS OPT D) HOTP E) TOTP 63- Which of the following provides protections against XSRF? A) Logging out of a browser application after each use B) Using browser plugins that restrict the use of JaveScript C) Ensuring all cookies and cache are cleared D) Implementing client-side firewall 64- Which of the following wireless attacks cannot be detected by scanning IDS? A) IV attack B) Evil twin C) Rogue access point D) Packet sniffing 65- Ann, company's sales manager, wants to send a secure email to the sales teams in another country while maintaining the confidentially of the message. Which of the following describes the BEST process to meet the requirements? A) Ann encrypts the email with the public keys of each member of the sales team. Members of the sales team decrypt the email with their respective private key B) Ann encrypts the email with her own private key. Members of the sales team decrypt the email with their respective public key C) Ann encrypts the email with her own private key. Each member of the sales team decrypts the email with Ann's public key D) Ann encrypts the email with the public key. Each member of the sales team decrypts the email with Ann's private key E) Ann encrypts the email with the sales team's shared private key. Each member of the sales team decrypts the email with shared public key
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


