Question: Please answer asap. I will upvote if correct. An Ethernet network has computers PC4 and PC5, and a router which connects the network to the
Please answer asap. I will upvote if correct.
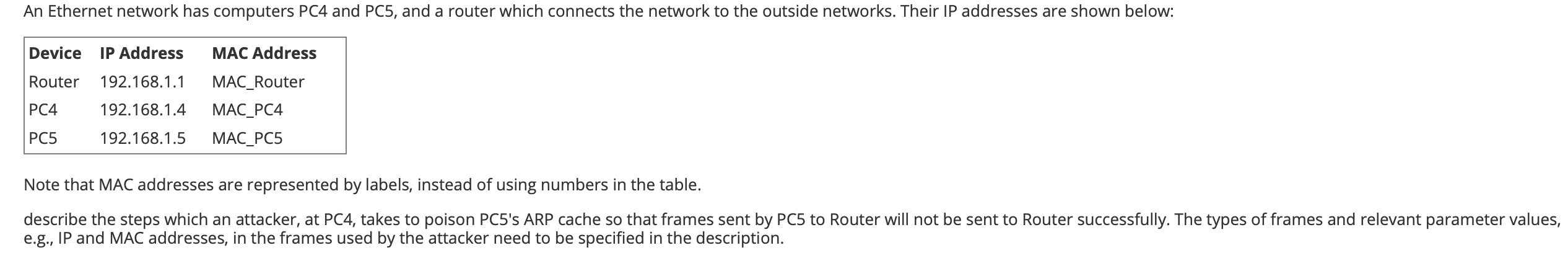
An Ethernet network has computers PC4 and PC5, and a router which connects the network to the outside networks. Their IP addresses are shown below: Device IP Address MAC Address Router 192.168.1.1 PC4 192.168.1.4 PC5 192.168.1.5 MAC_Router MAC_PC4 MAC_PC5 Note that MAC addresses are represented by labels, instead of using numbers in the table. describe the steps which an attacker, at PC4, takes to poison PC5's ARP cache so that frames sent by PC5 to Router will not be sent to Router successfully. The types of frames and relevant parameter values, e.g., IP and MAC addresses, in the frames used by the attacker need to be specified in the description.
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


