Question: Please complete fully and thank you 3. (8 points) Using RSA, Alice and Bob set up their asymmetric communication method. Alice announces her public key
 Please complete fully and thank you
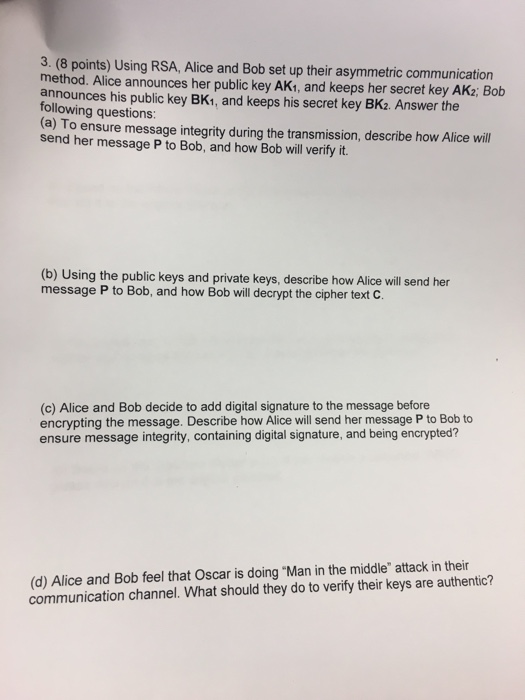
Please complete fully and thank you 3. (8 points) Using RSA, Alice and Bob set up their asymmetric communication method. Alice announces her public key AK1, and keeps her secret key AK2; Bob announces his public key BK1, and keeps his secret key BK2. Answer the following questions: (a) To ensure message integrity during the transmission, describe how Alice will send her message P to Bob, and how Bob will verify it. (b) Using the public keys and private keys, describe how Alice will send her message P to Bob, and how Bob will decrypt the cipher text C. (c) Alice and Bob decide to add digital signature to the message before encrypting the message. Describe how Alice will send her message P to Bob to ensure message integrity, containing digital signature, and being encrypted? (d) Alice and Bob feel that Oscar is doing "Man in the middle" attack in their communication channel. What should they do to verify their keys are authentic
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


