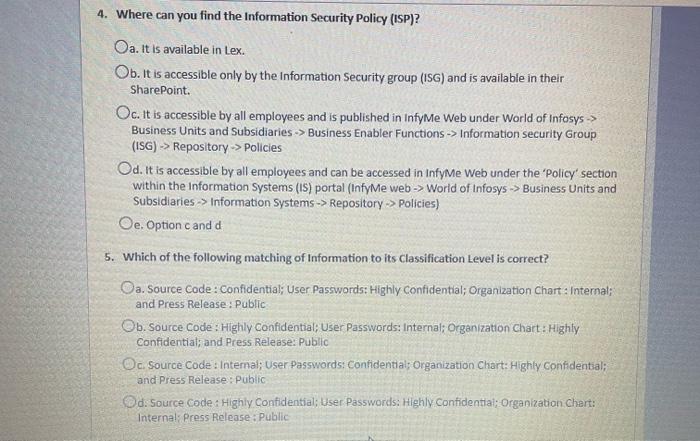
4. Where can you find the Information Security Policy (ISP)? Oa. It is available in Lex....
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
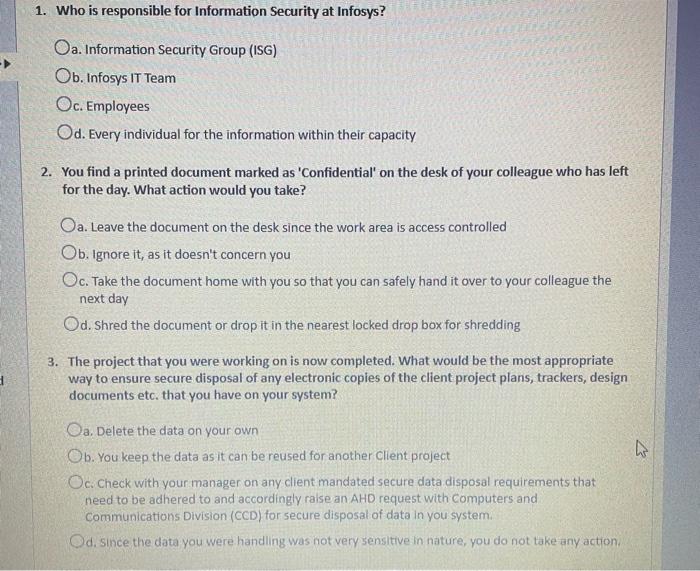
4. Where can you find the Information Security Policy (ISP)? Oa. It is available in Lex. Ob. It is accessible only by the Information Security group (ISG) and is available in their SharePoint. Oc. It is accessible by all employees and is published in InfyMe Web under World of Infosys > Business Units and Subsidiaries > Business Enabler Functions -> Information security Group (ISG) -> Repository-> Policies Od. It is accessible by all employees and can be accessed in InfyMe Web under the 'Policy' section within the Information Systems (IS) portal (InfyMe web-> World of Infosys > Business Units and Subsidiaries > Information Systems -> Repository-> Policies) Oe. Option c and d 5. Which of the following matching of Information to its Classification Level is correct? Oa. Source Code : Confidential; User Passwords: Highly Confidential; Organization Chart: Internal; and Press Release: Public Ob. Source Code: Highly Confidential; User Passwords: Internal; Organization Chart: Highly Confidential; and Press Release: Public Oc. Source Code: Internal; User Passwords: Confidential; Organization Chart: Highly Confidential; and Press Release: Public Od: Source Code: Highly Confidential; User Passwords: Highly Confidential; Organization Chart: Internal; Press Release: Public 1. Who is responsible for Information Security at Infosys? Oa. Information Security Group (ISG) Ob. Infosys IT Team Oc. Employees Od. Every individual for the information within their capacity 2. You find a printed document marked as 'Confidential' on the desk of your colleague who has left for the day. What action would you take? Oa. Leave the document on the desk since the work area is access controlled Ob. Ignore it, as it doesn't concern you Oc. Take the document home with you so that you can safely hand it over to your colleague the next day Od. Shred the document or drop it in the nearest locked drop box for shredding 3. The project that you were working on is now completed. What would be the most appropriate way to ensure secure disposal of any electronic copies of the client project plans, trackers, design documents etc. that you have on your system? Oa. Delete the data on your own Ob. You keep the data as it can be reused for another Client project Oc. Check with your manager on any client mandated secure data disposal requirements that need to be adhered to and accordingly raise an AHD request with Computers and Communications Division (CCD) for secure disposal of data in you system. Od. Since the data you were handling was not very sensitive in nature, you do not take any action, 4 4. Where can you find the Information Security Policy (ISP)? Oa. It is available in Lex. Ob. It is accessible only by the Information Security group (ISG) and is available in their SharePoint. Oc. It is accessible by all employees and is published in InfyMe Web under World of Infosys > Business Units and Subsidiaries > Business Enabler Functions -> Information security Group (ISG) -> Repository-> Policies Od. It is accessible by all employees and can be accessed in InfyMe Web under the 'Policy' section within the Information Systems (IS) portal (InfyMe web-> World of Infosys > Business Units and Subsidiaries > Information Systems -> Repository-> Policies) Oe. Option c and d 5. Which of the following matching of Information to its Classification Level is correct? Oa. Source Code : Confidential; User Passwords: Highly Confidential; Organization Chart: Internal; and Press Release: Public Ob. Source Code: Highly Confidential; User Passwords: Internal; Organization Chart: Highly Confidential; and Press Release: Public Oc. Source Code: Internal; User Passwords: Confidential; Organization Chart: Highly Confidential; and Press Release: Public Od: Source Code: Highly Confidential; User Passwords: Highly Confidential; Organization Chart: Internal; Press Release: Public 1. Who is responsible for Information Security at Infosys? Oa. Information Security Group (ISG) Ob. Infosys IT Team Oc. Employees Od. Every individual for the information within their capacity 2. You find a printed document marked as 'Confidential' on the desk of your colleague who has left for the day. What action would you take? Oa. Leave the document on the desk since the work area is access controlled Ob. Ignore it, as it doesn't concern you Oc. Take the document home with you so that you can safely hand it over to your colleague the next day Od. Shred the document or drop it in the nearest locked drop box for shredding 3. The project that you were working on is now completed. What would be the most appropriate way to ensure secure disposal of any electronic copies of the client project plans, trackers, design documents etc. that you have on your system? Oa. Delete the data on your own Ob. You keep the data as it can be reused for another Client project Oc. Check with your manager on any client mandated secure data disposal requirements that need to be adhered to and accordingly raise an AHD request with Computers and Communications Division (CCD) for secure disposal of data in you system. Od. Since the data you were handling was not very sensitive in nature, you do not take any action, 4
Expert Answer:
Answer rating: 100% (QA)
Question Answer 1 The Information Security group ISC Reason The Information Security group ISG is th... View the full answer

Related Book For 

Income Tax Fundamentals 2013
ISBN: 9781285586618
31st Edition
Authors: Gerald E. Whittenburg, Martha Altus Buller, Steven L Gill
Posted Date:
Students also viewed these finance questions
-
urgent, please help me get the output of GAMS code, but it is too large to post it here so please if you can provide help answer me with your email address to send it, if not please tell me to find...
-
Conductance is analogous to O a. Flux O b. Permeance O C. Inductance O d. Reluctance
-
waiting someone to get me help with it please try to solve as soon as possible..thanks i appreciate Simple Harmonic Motion IsoinnosT ylggA ANO0ESMEM Q1). A simple harmonic system (energy is...
-
Consider a group of 12 employees of whom five are in management and seven do clerical work. Select at random a sample of size 4. What is the probability that there will be one manager in this sample?
-
What are the major differences between independent auditors reports on financial statements and internal and governmental reports on efficiency, economy, and program results audits?
-
A All-cis Cyclodecapentaene is a stable molecule that shows a single absorption in its 1H NMR spectrum at 5.67 ?. Tell whether it is aromatic, and explain its NMR spectrum.
-
Fantastic Sams and Defendants PSTEVO, LLC and Jeremy Baker entered into a franchise agreement pursuant to which Fantastic Sams granted PSTEVO a franchise to operate a Fantastic Sams Salon. According...
-
Ginocera Inc. is a designer, manufacturer, and distributor of low-cost, high-quality stainless steel kitchen knives. A new kitchen knife series called the Kitchen Ninja was released for production in...
-
One way financial managers evaluate a firm's current financial condition is by computing ratios based on current accounts listed on the firm's financial statements. Financial managers look at four...
-
Paul and Wayne equally own the PW Partnership. Paul's basis was $30,000 and Wayne's basis was $22,000 at the beginning of the year. PW Partnership had the following income and expense items:...
-
A hydrodynamic journal bearing is subjected to 3000N load at rotational speed of 2000rpm. The bearing diameter and length are 40mm. If radial clearance is 30m and bearing is lubricated with an oil...
-
Based on the Law, the Administration of Criminal Law, Law Enforcement, and Criminal Prosecution select one to address the general idea in relation to the topic. Critique every thought. Clarify your...
-
Blocks of granite are to be hauled up a 15 slope out of a quarry, and dirt is to be dumped into the quarry to fill up old holes. To sim- plify the process, you design a system in which a granite...
-
A segment of wire carries a current of 18 A along the x axis from x = 3.5 m to x = 0 and then along the y axis from y = 0 to y = 5.0 m. In this region of space, the magnetic field is equal to 38 mT...
-
What are the mechanisms underlying inflammatory responses and cytokine storm syndromes, including the dysregulation of cytokine signaling pathways such as interleukin-6 (IL-6) and tumor necrosis...
-
Analyse the role of budgets in assisting and supporting an organisation's operations. Give at least two examples
-
From the following information on the income statement and the balance sheet, what is EBT (earnings before tax) in 2019? Assume that the tax rate is 30%. Income Statement Items Revenue Cost of goods...
-
In Exercises delete part of the domain so that the function that remains is one-to-one. Find the inverse function of the remaining function and give the domain of the inverse function. f(x) = 16x4 -3...
-
Sally and Charles Heck received the following dividends and interest during 2012: Assuming the Hecks file a joint tax return, complete Schedule B of Form 1040 (on page 2-33) for them for the 2012 tax...
-
Please answer the following questions regarding the taxability of Social Security: a. A 68-year-old taxpayer has $20,000 in Social Security income and $100,000 in tax-free municipal bond income. Does...
-
For each of the following situations, indicate whether the taxpayer(s) is (are) required to file a tax return for 2012. Explain your answer. a. Helen is a single taxpayer with interest income in 2012...
-
Last year, Miley decided to terminate the S corporation election of her solely owned corporation on October 17, 2018 (effective immediately), in preparation for taking it public. At the time of the...
-
You have been assigned to compute the income tax provision for Motown Memories Inc. (MM) as of December 31, 2019. The companys income statement for 2019 is provided below: MM prepared the following...
-
Jane has been operating Mansfield Park as a C corporation and decides she would like to make an S election. What is the earliest the election will become effective under each of these alternative...

Study smarter with the SolutionInn App


