Question: Port Number Protocol Application FTP Data FTP Control SSH Telnet SMTP DNS HTTP POP3 SSL Message SYN Description SYN-ACK ACK 1. 2. 3. 4.
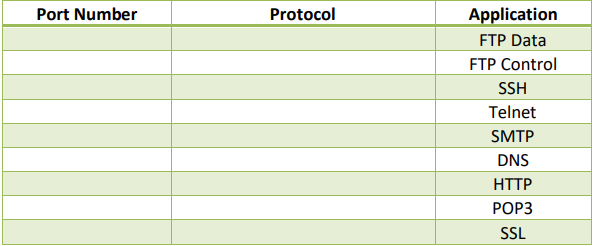
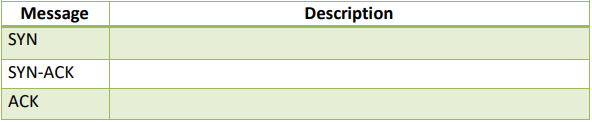
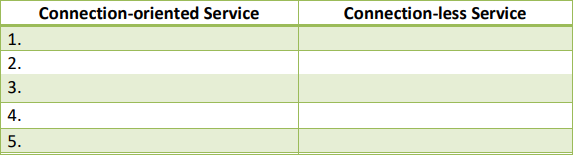
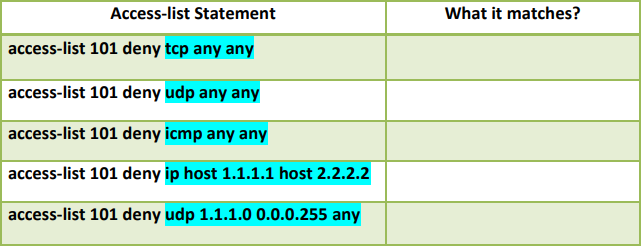
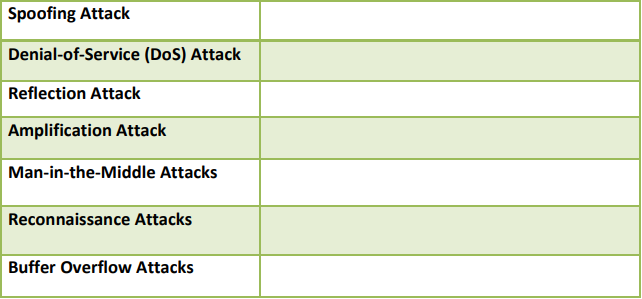
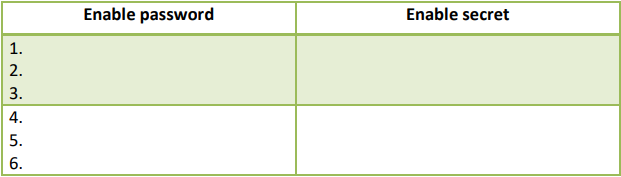
Port Number Protocol Application FTP Data FTP Control SSH Telnet SMTP DNS HTTP POP3 SSL Message SYN Description SYN-ACK ACK 1. 2. 3. 4. 5. Connection-oriented Service Connection-less Service Access-list Statement access-list 101 deny tcp any any access-list 101 deny udp any any access-list 101 deny icmp any any access-list 101 deny ip host 1.1.1.1 host 2.2.2.2 access-list 101 deny udp 1.1.1.0 0.0.0.255 any What it matches? Spoofing Attack Denial-of-Service (DoS) Attack Reflection Attack Amplification Attack Man-in-the-Middle Attacks Reconnaissance Attacks Buffer Overflow Attacks Enable password Enable secret 1. 2. 3. 4. 5. 6. 123456
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


