Question: Program 3: Make a program that counts infected computers on a computer network. The virus spreads through the network, and every computer that is
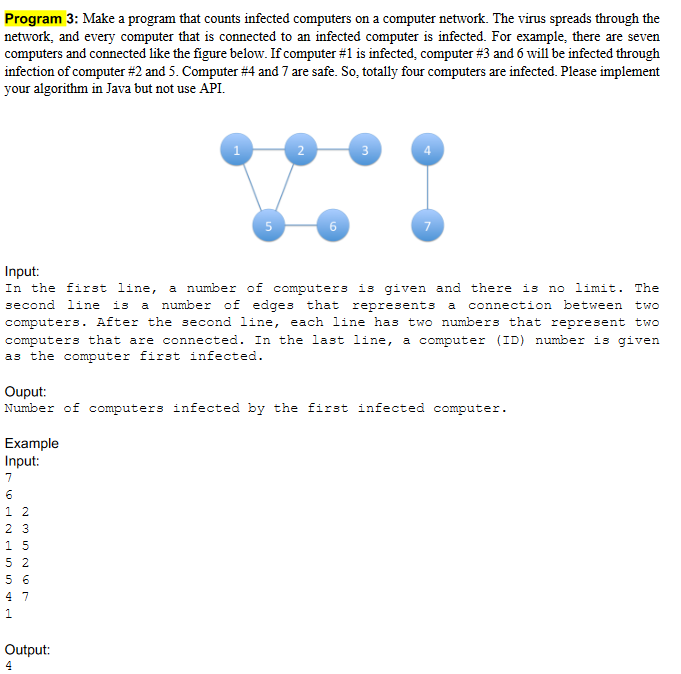
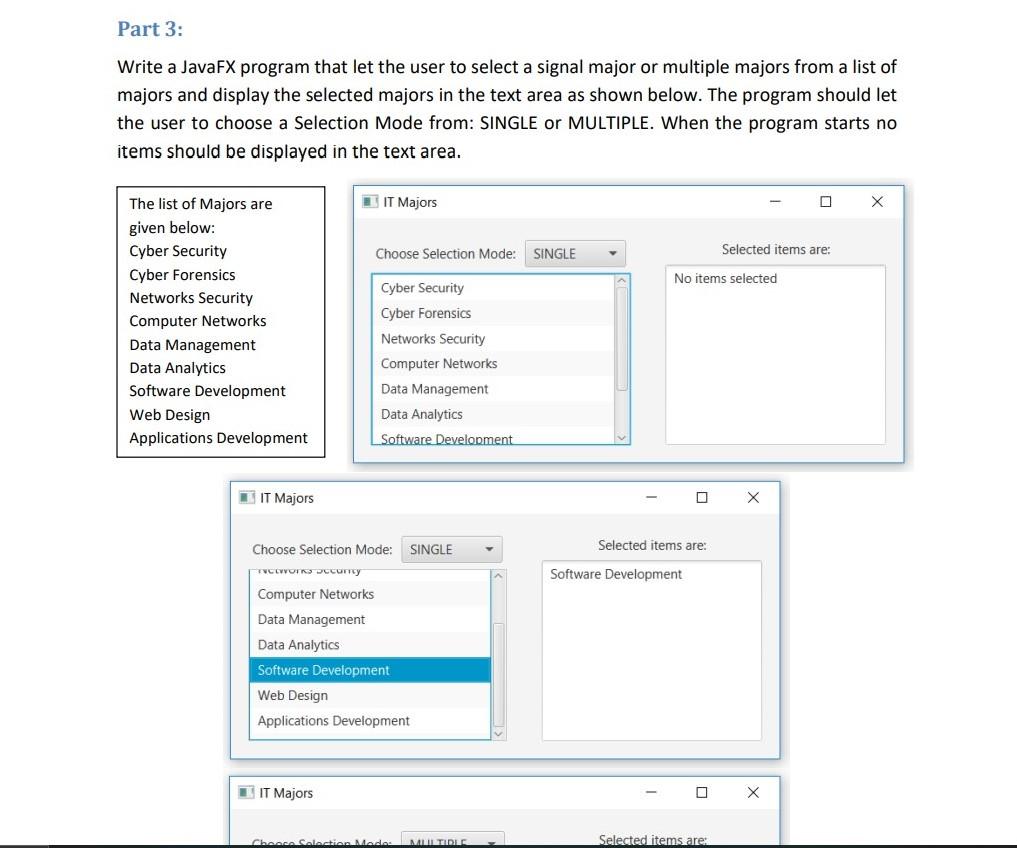
Program 3: Make a program that counts infected computers on a computer network. The virus spreads through the network, and every computer that is connected to an infected computer is infected. For example, there are seven computers and connected like the figure below. If computer #1 is infected, computer #3 and 6 will be infected through infection of computer #2 and 5. Computer #4 and 7 are safe. So, totally four computers are infected. Please implement your algorithm in Java but not use API. Example Input: 7 6 12 23 15 52 56 1 Input: In the first line, a number of computers is given and there is no limit. The second line is a number of edges that represents a connection between two computers. After the second line, each line has two numbers that represent two computers that are connected. In the last line, a computer (ID) number is given as the computer first infected. 4 7 1 2 Ouput: Number of computers infected by the first infected computer. Output: 4 6 3 7 Part 3: Write a JavaFX program that let the user to select a signal major or multiple majors from a list of majors and display the selected majors in the text area as shown below. The program should let the user to choose a Selection Mode from: SINGLE or MULTIPLE. When the program starts no items should be displayed in the text area. The list of Majors are given below: Cyber Security Cyber Forensics Networks Security Computer Networks Data Management Data Analytics Software Development Web Design Applications Development IT Majors TYCOWORKS Securty Computer Networks IT Majors Choose Selection Mode: SINGLE Cyber Security Cyber Forensics IT Majors Networks Security Computer Networks Choose Selection Mode: SINGLE Data Management Data Analytics Software Development Data Management Data Analytics Software Development Web Design Applications Development Choose Selection Mode MULTIDIE No items selected Selected items are: Software Development 0 Selected items are: Selected items are: X X X
Step by Step Solution
3.54 Rating (151 Votes )
There are 3 Steps involved in it
Part 1 Counting Infected Computers on a Computer Network Heres a Java program that implements the algorithm to count the number of infected computers on a computer network java import javautilArrayLis... View full answer

Get step-by-step solutions from verified subject matter experts


