Question: Q1: Using S-DES block cipher, do the following: IP 1. Generate the keys, K1 and K2 from key= 1011001011 2. Encrypt the hexadecimal number:
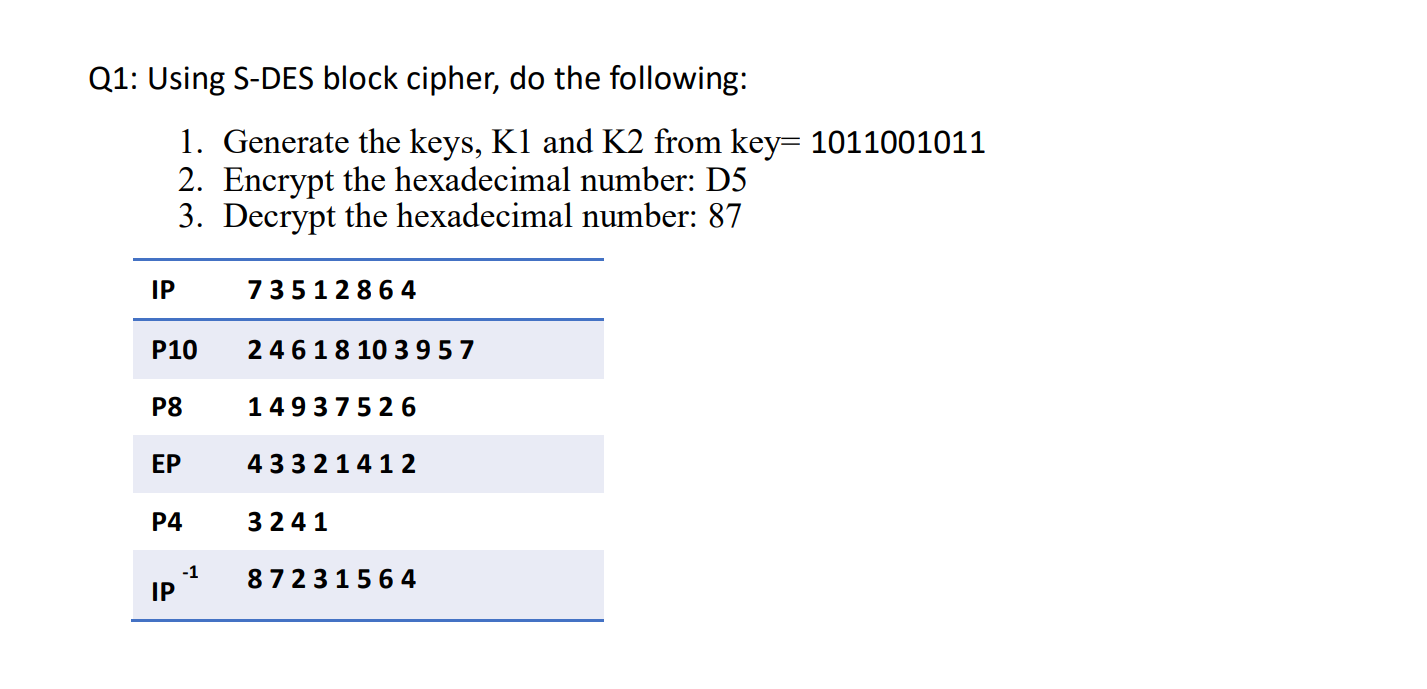
Q1: Using S-DES block cipher, do the following: IP 1. Generate the keys, K1 and K2 from key= 1011001011 2. Encrypt the hexadecimal number: D5 3. Decrypt the hexadecimal number: 87 P10 P8 EP P4 IP -1 73512864 2461810 3 957 14937526 43321412 3241 87231564
Step by Step Solution
3.37 Rating (150 Votes )
There are 3 Steps involved in it
here are the steps to generate the keys K1 and K2 from key 1011001011 encrypt the hexadecimal number D5 and decrypt the hexadecimal number 87 using the SDES block cipher Key Generation Permute the key ... View full answer

Get step-by-step solutions from verified subject matter experts


