Question: Q.1.3 Q.1.4 Using suitable examples, differentiate between the launch and evade actions of malware. Your answer must give the types of malware as examples
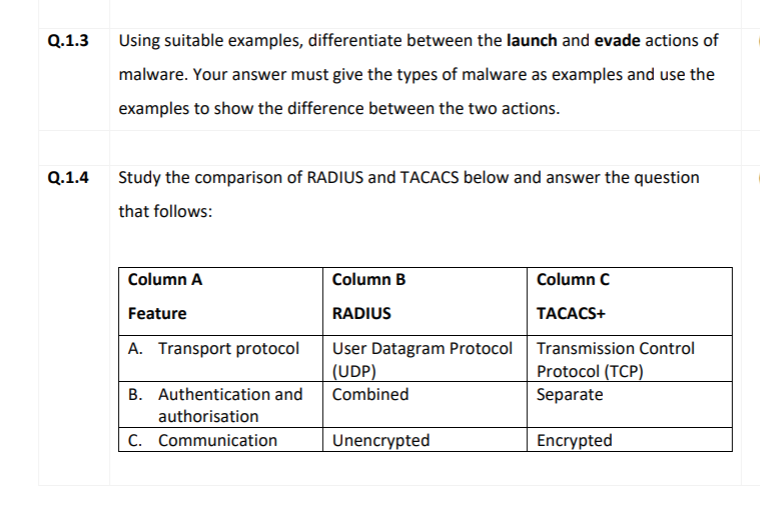
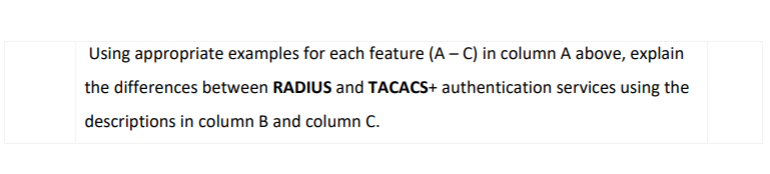
Q.1.3 Q.1.4 Using suitable examples, differentiate between the launch and evade actions of malware. Your answer must give the types of malware as examples and use the examples to show the difference between the two actions. Study the comparison of RADIUS and TACACS below and answer the question that follows: Column A Feature A. Transport protocol B. Authentication and authorisation C. Communication Column B RADIUS User Datagram Protocol (UDP) Combined Unencrypted Column C TACACS+ Transmission Control Protocol (TCP) Separate Encrypted Using appropriate examples for each feature (A - C) in column A above, explain the differences between RADIUS and TACACS+ authentication services using the descriptions in column B and column C. Q.1.3 Q.1.4 Using suitable examples, differentiate between the launch and evade actions of malware. Your answer must give the types of malware as examples and use the examples to show the difference between the two actions. Study the comparison of RADIUS and TACACS below and answer the question that follows: Column A Feature A. Transport protocol B. Authentication and authorisation C. Communication Column B RADIUS User Datagram Protocol (UDP) Combined Unencrypted Column C TACACS+ Transmission Control Protocol (TCP) Separate Encrypted Using appropriate examples for each feature (A - C) in column A above, explain the differences between RADIUS and TACACS+ authentication services using the descriptions in column B and column C.
Step by Step Solution
There are 3 Steps involved in it
The question is asking to explain the differences between RADIUS and TACACS authentication services by referring to each of their characteristics list... View full answer

Get step-by-step solutions from verified subject matter experts


