Question: Q2. List with Hash Pointers (7 points) The linked list below uses hash pointers. Each item in this list has three fields: ID, previous item
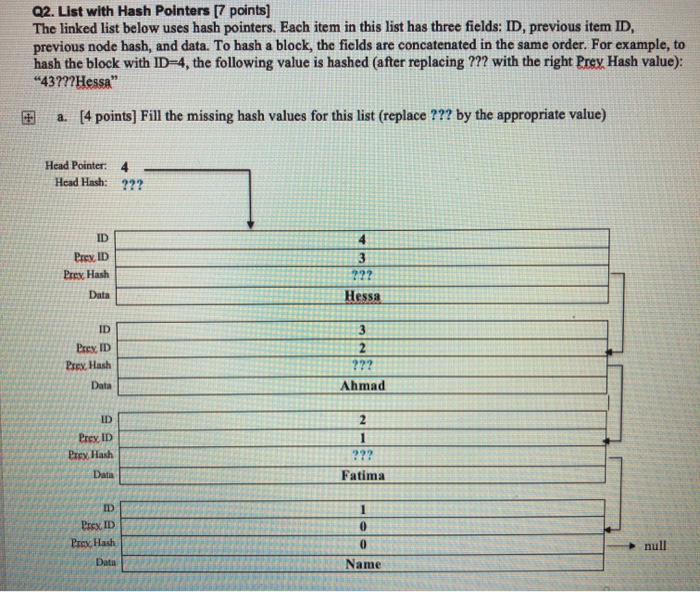
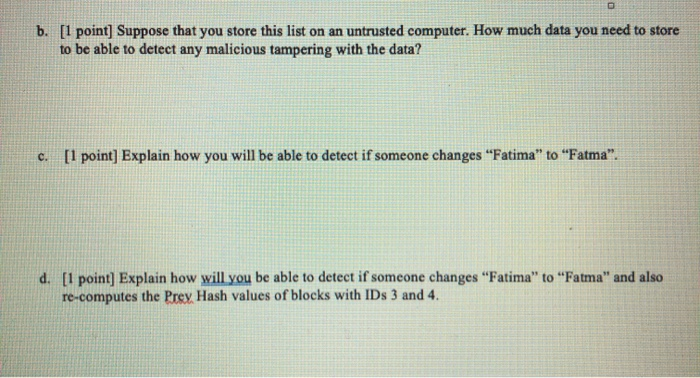
Q2. List with Hash Pointers (7 points) The linked list below uses hash pointers. Each item in this list has three fields: ID, previous item ID, previous node hash, and data. To hash a block, the fields are concatenated in the same order. For example, to hash the block with ID-4, the following value is hashed (after replacing ??? with the right Prey Hash value): "43???Hessa" a. [4 points] Fill the missing hash values for this list (replace ??? by the appropriate value) Head Pointer 4 Head Hash: ??? ID Prey ID Prey Hash Data Prex ID Prey, Hash ID Prey ID Prey, Hash Data Prex ID - b. [1 point] Suppose that you store this list on an untrusted computer. How much data you need to store to be able to detect any malicious tampering with the data? c. [1 point) Explain how you will be able to detect if someone changes "Fatima" to "Fatma". d. [1 point] Explain how will you be able to detect if someone changes "Fatima" to "Fatma" and also re-computes the Prey Hash values of blocks with IDs 3 and 4. Assume that the cryptographic hash function used is SHA256
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


