Question: Que. Kevin has captured crypto keys and he will use them to decrypt an email sent between Host A and Host C and intercepted on
Que. Kevin has captured crypto keys and he will use them to decrypt an email sent between Host A and Host C and intercepted on the Internet. Which crypto keys will help him? Answer Yes or No to each of the following keys and briefly explain the reason.
a. Keys for Gateway A
b. Keys for Gateway B
c. Keys for Gateway C
Info:
The gateways provide cryptographic protection.
Gateway A provides WPA2 crypto protection. Gateways B and C provide IPsec crypto protection for traffic between Site 1 and Site 2. They provide no crypto protection between other Internet destinations.
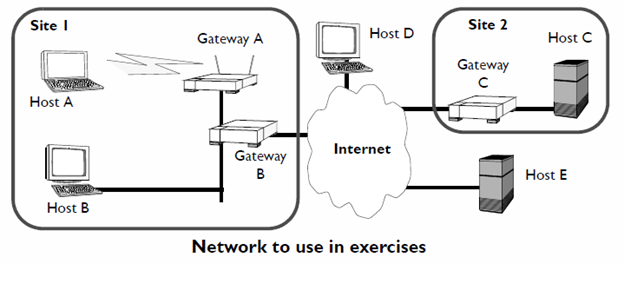
Site I Host A Host B Host D Gateway A Internet Gateway Network to use in exercises Site 2 Host C Gateway Host E
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


