Question: QUESTION 1 - Wireless Network in Business a) Discuss the connectivity, accessibility and availability of wireless communications with a simple case example that you can
QUESTION 1 - Wireless Network in Business
a) Discuss the connectivity, accessibility and availability of wireless communications with a simple case example that you can construct [e.g., your school, home or business in your surrounding area]
b) Discuss the disadvantage of wireless communication in high rise building CBD or mountainous regions.
c) Recommend a wireless communication technology suitable to support seamless network connectivity between two adjacent buildings that are about 500 meters apart.
QUESTION 2 - Wireless Signal Processing
a) Explain the advantages of PSK [phase shift keying] over ASK [amplitude shift keying].
b) Explain the effects of multipath signal interference.
c) Discuss the effects of radio waves on human health. Rationalise your answer on the topic and support your answer with external references.
QUESTION 3 - Wireless Personal Area Networks
a) Describe the operations of ScatterNet.
b) Appraise how NFC [near field communication] can accelerate business operations with a simple case example.
c) Investigate and report the limitations of infrared light communications in daily home use.
QUESTION 4 - Wireless Network Security
a) Explain the advantages of WPA2 to WPA and WEP.
b) Recommend an appropriate wireless network security technology if you are to secure a large park with more than 1000 visitors. Would 4G more useful than WIFI? Justify your answer.
QUESTION 5 - Mobile Communications
a) Explain the use of mobile base stations and describe how the mobile call hand-offs are handled with an appropriate figure or diagram.
b) You are using a mobile phone to call your relative living in another country [using International calls]; list the communication components that are required to establish your call connection. Explain the steps to establish the call connection.
c) Critique the use of PicoCells and highlight its applications in 5G networks.
QUESTION 6: Wireless Enterprise Security
Consider the enterprise network in picture below
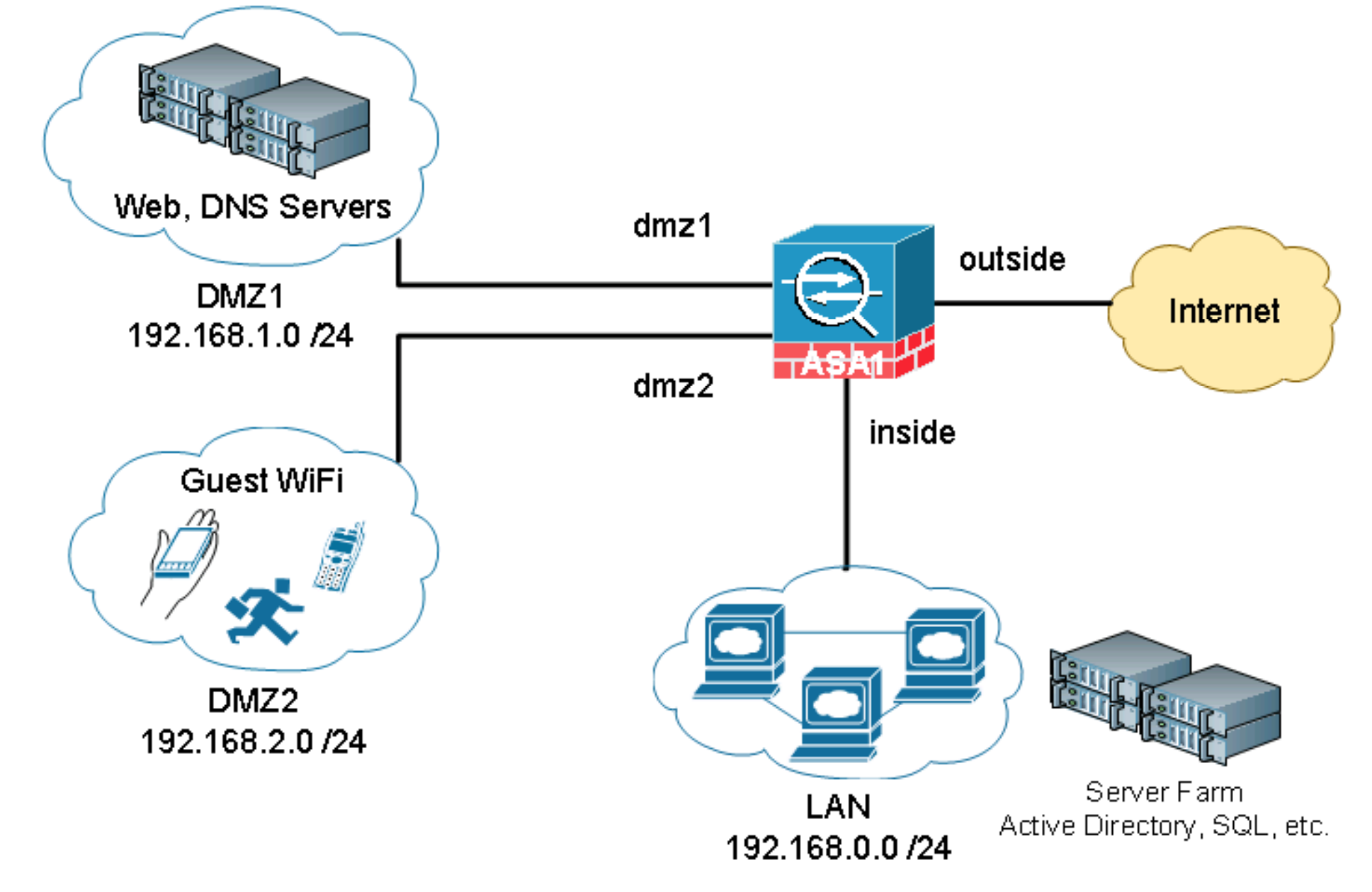
Web, DNS Servers DMZ1 192.168.1.0/24 Guest WiFi DMZ2 192.168.2.0/24 dmz1 dmz2 IID ASA inside outside Internet Server Farm LAN 192.168.0.0/24 Active Directory, SQL, etc.
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


