Question: Consider the following code: module FF (Q, X, Clk, rst); output Q; input X, Clk, rst; reg Q; always @ (posedge CLK, negedge rst)
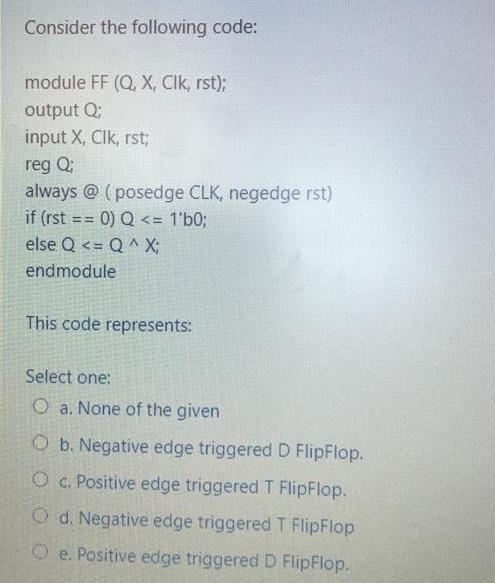
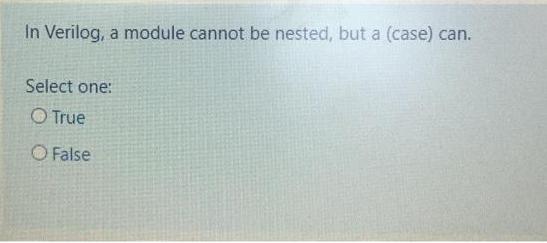
Consider the following code: module FF (Q, X, Clk, rst); output Q; input X, Clk, rst; reg Q; always @ (posedge CLK, negedge rst) if (rst = 0) Q In Verilog, a module cannot be nested, but a (case) can. Select one: O True O False
Step by Step Solution
3.39 Rating (158 Votes )
There are 3 Steps involved in it
T Pipflop Dflipflop Q Opreenat Onext Qnert Dprevant D Opresent 3D Gpregent T apresent h... View full answer

Get step-by-step solutions from verified subject matter experts


