Question: Question 15 1 pts What can you learn from a Ping command? The MAC address and other info for your comptuer. Speed of response from
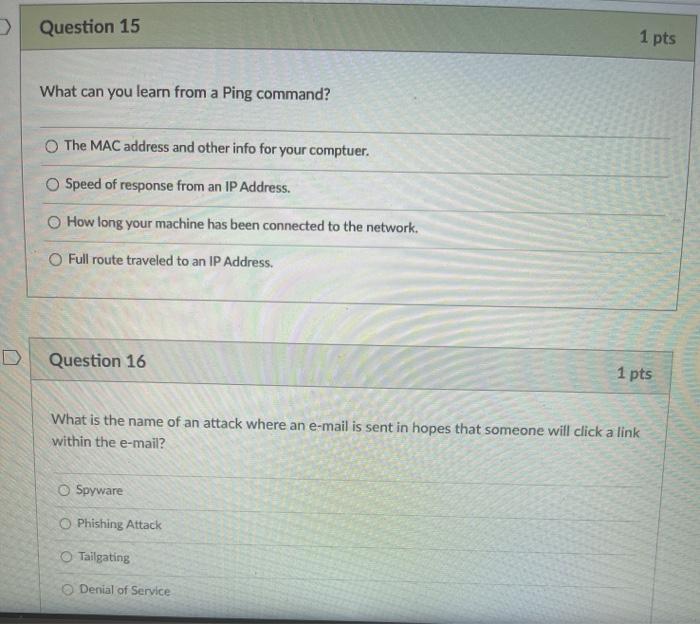
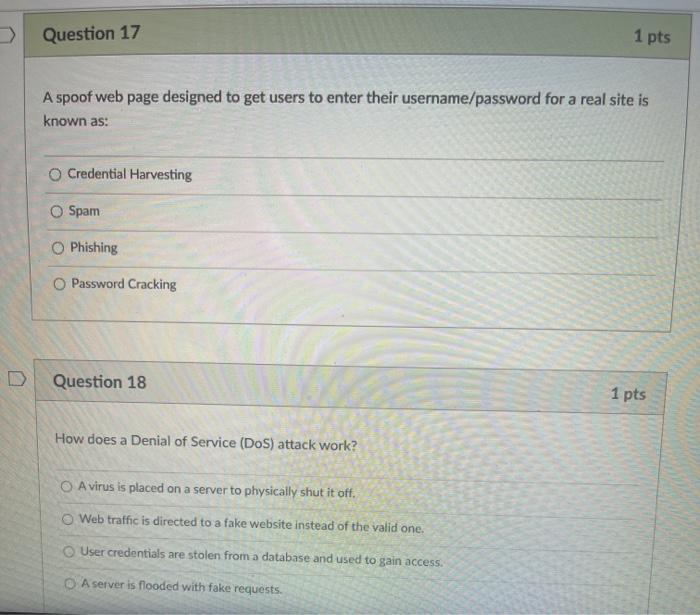
Question 15 1 pts What can you learn from a Ping command? The MAC address and other info for your comptuer. Speed of response from an IP Address. How long your machine has been connected to the network Full route traveled to an IP Address. Question 16 1 pts What is the name of an attack where an e-mail is sent in hopes that someone will click a link within the e-mail? Spyware Phishing Attack O Tailgating Denial of Service Question 17 1 pts A spoof web page designed to get users to enter their username/password for a real site is known as: Credential Harvesting Spam Phishing O Password Cracking Question 18 1 pts How does a Denial of Service (DoS) attack work? A virus is placed on a server to physically shut it off. Web traffic is directed to a fake website instead of the valid one. User credentials are stolen from a database and used to gain access. A server is flooded with fake requests
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


