Question: Question 2 7 A threat actor gains access to a system by compromising a user's account. The threat actor is then able to execute p
Question
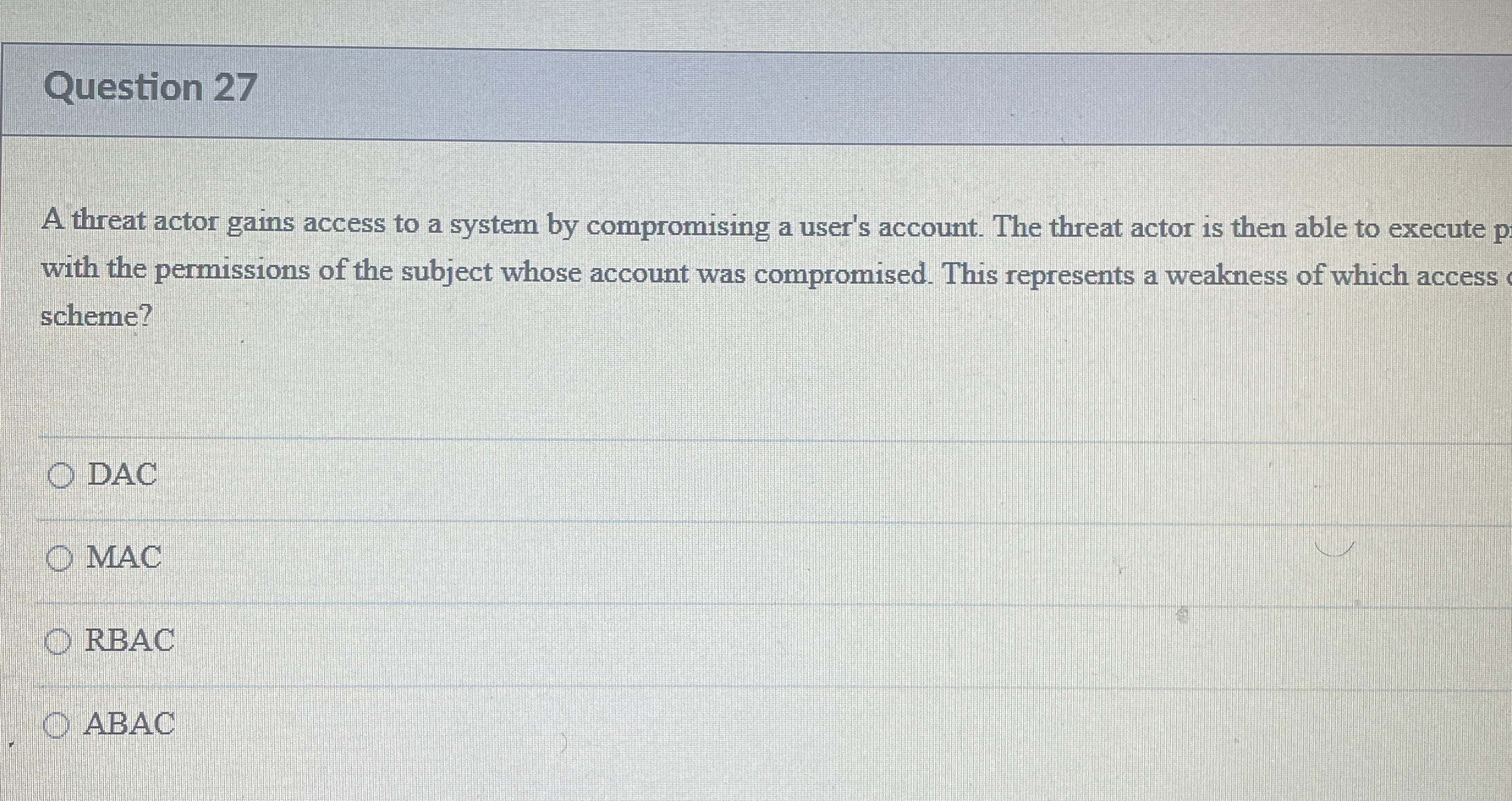
A threat actor gains access to a system by compromising a user's account. The threat actor is then able to execute with the permissions of the subject whose account was compromised. This represents a weakness of which access scheme?
DAC
MAC
RBAC
ABAC
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock

The scenario described suggests that a threat actor has gained access to a system by compromising a ... View full answer

Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


