Question: Question 3 (1 point) Saved In which of these attack scenarios is the attacker most powerful? Ciphertext only attacks Known plaintext attacks Chosen plaintext attack
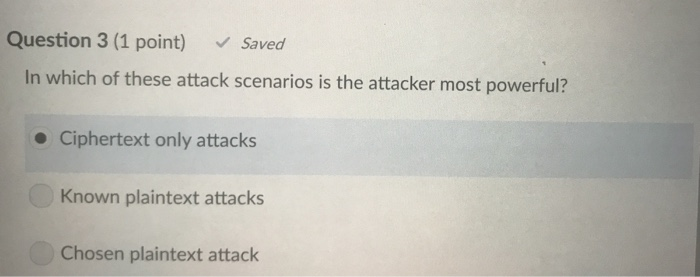
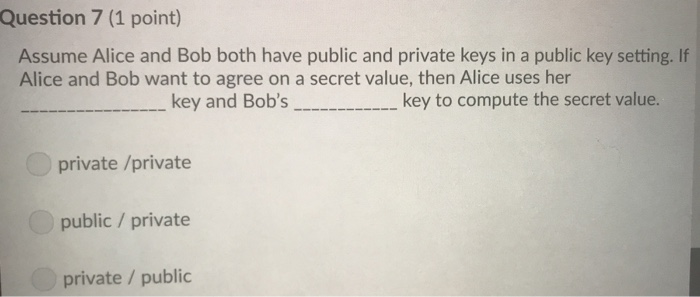
Question 3 (1 point) Saved In which of these attack scenarios is the attacker most powerful? Ciphertext only attacks Known plaintext attacks Chosen plaintext attack Question 7 (1 point) Assume Alice and Bob both have public and private keys in a public key setting. If Alice and Bob want to agree on a secret value, then Alice uses her key and Bob's_key to compute the secret value. private /private public / private private / public
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


