Question: Question - 3 4 4 Let f f ( x ) d x = 2, (1 g ( x ) d x z 3
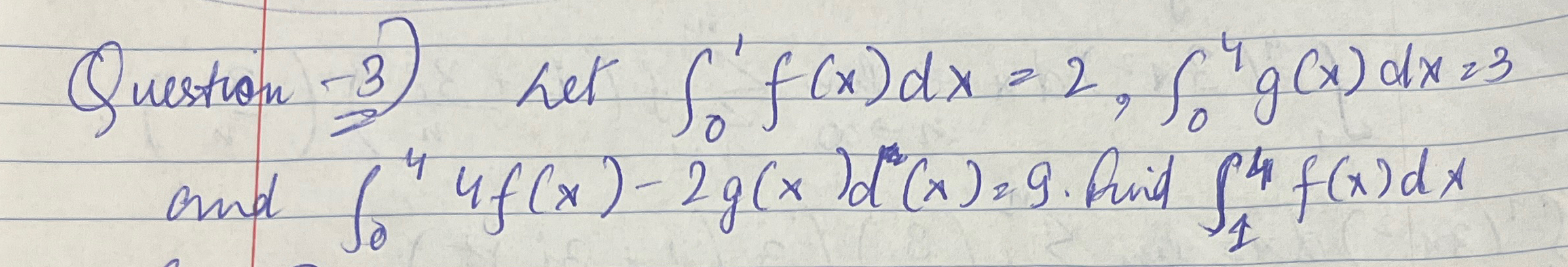
Question - 3 4 4 Let f f ( x ) d x = 2, (1 g ( x ) d x z 3 So and for 4 f ( x ) - 2 g ( x ) d ( x ) = 9. find ft f ( x ) d x 4
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


