Question: QUESTION 7 When system logs are used to determine if someone is trying to gain unauthorized access to a system, this is an example of
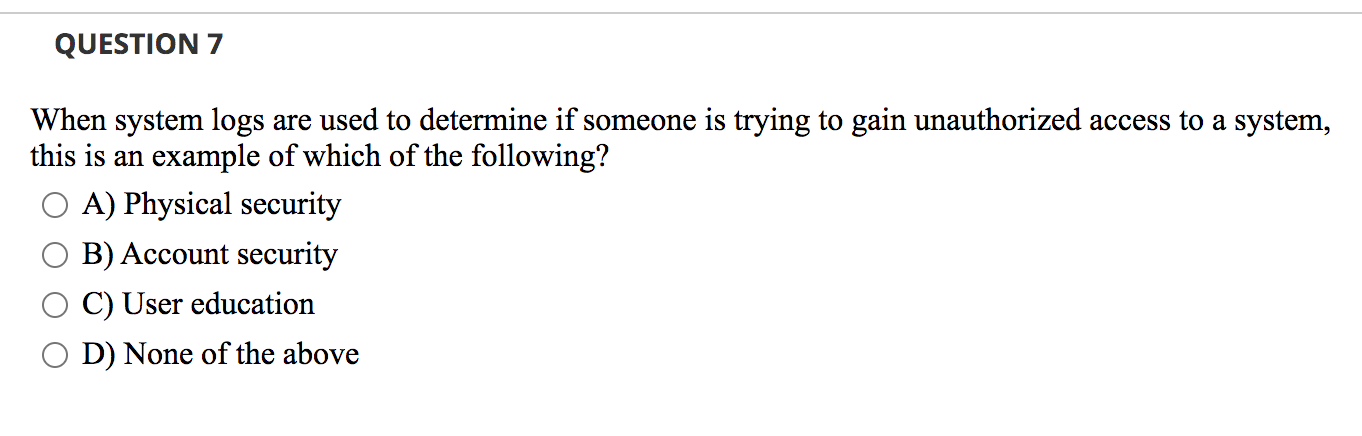
QUESTION 7 When system logs are used to determine if someone is trying to gain unauthorized access to a system, this is an example of which of the following? A) Physical security B) Account security C) User education D) None of the above
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


