Question: Question 8 (1 point) A flaw or weakness in a system's design, implementation, or operation and management that could be exploited to violate the system's
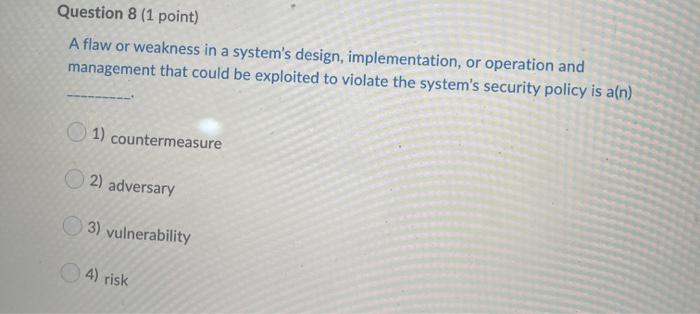
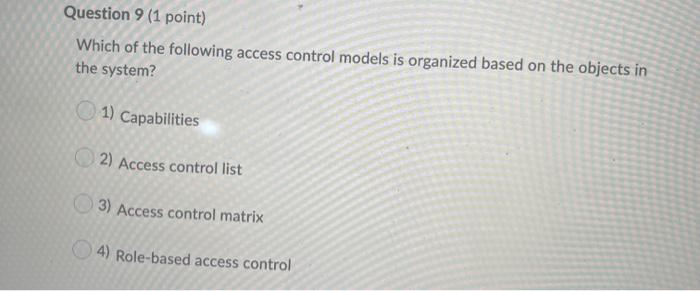
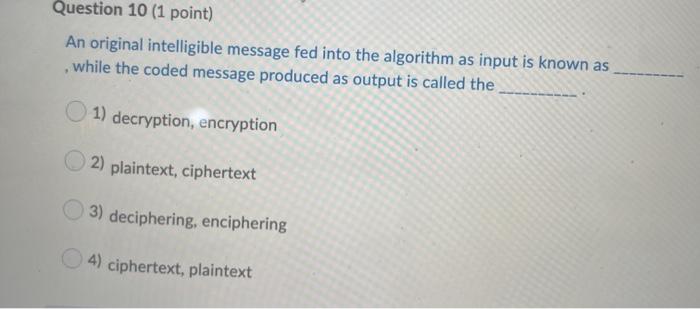
Question 8 (1 point) A flaw or weakness in a system's design, implementation, or operation and management that could be exploited to violate the system's security policy is a(n) 1) countermeasure 2) adversary 3) vulnerability 4) risk Question 9 (1 point) Which of the following access control models is organized based on the objects in the system? 1) Capabilities 2) Access control list 3) Access control matrix 4) Role-based access control Question 10 (1 point) An original intelligible message fed into the algorithm as input is known as while the coded message produced as output is called the 1) decryption, encryption 2) plaintext, ciphertext 3) deciphering, enciphering 4) ciphertext, plaintext
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


