Question: Server 1 Physical Config Services Desktop Programming Attributes IP Configuration IP Configuration DHCP IPv4 Address Subnet Mask Default Gateway DNS Server IPv6 Configuration Automatic
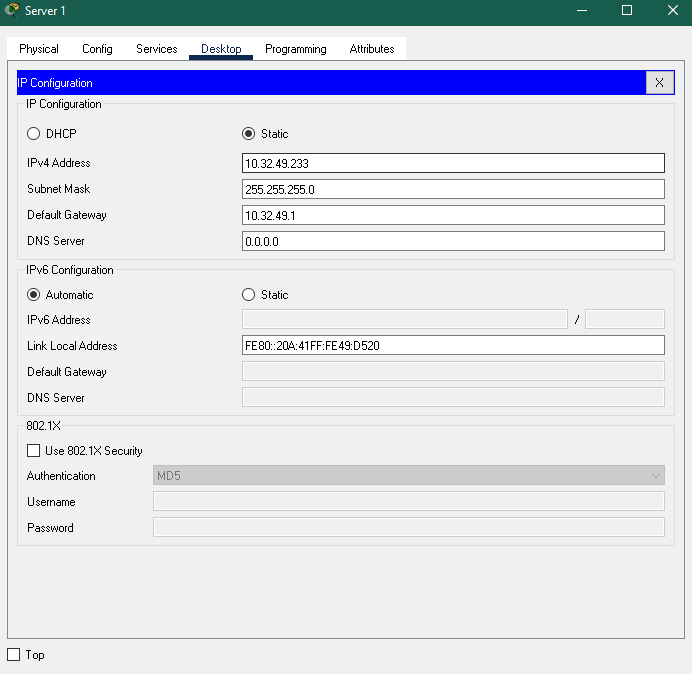
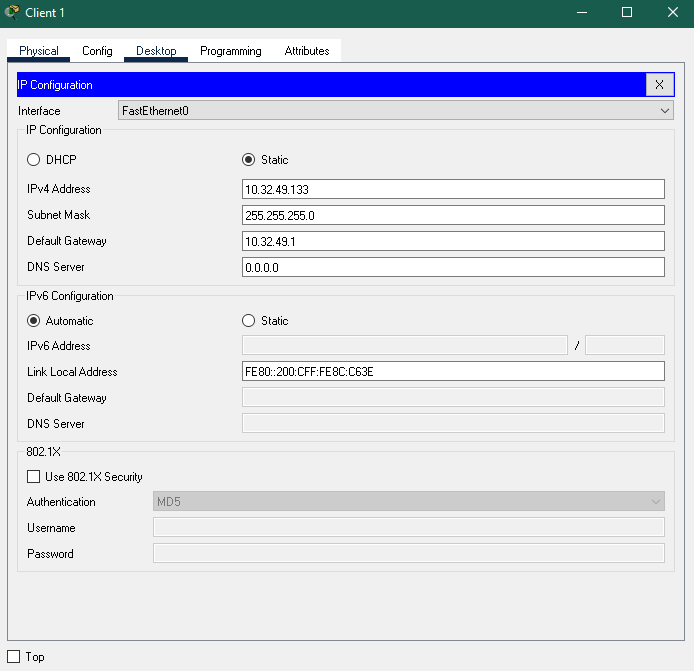
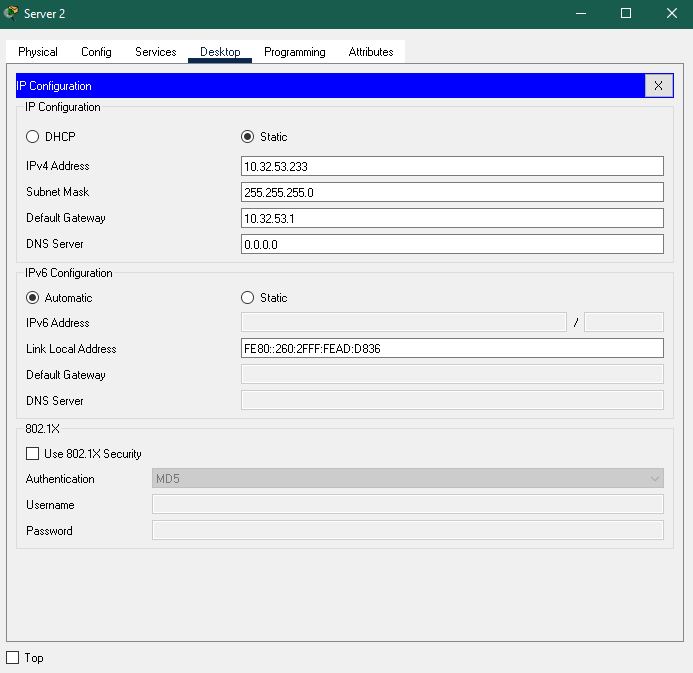
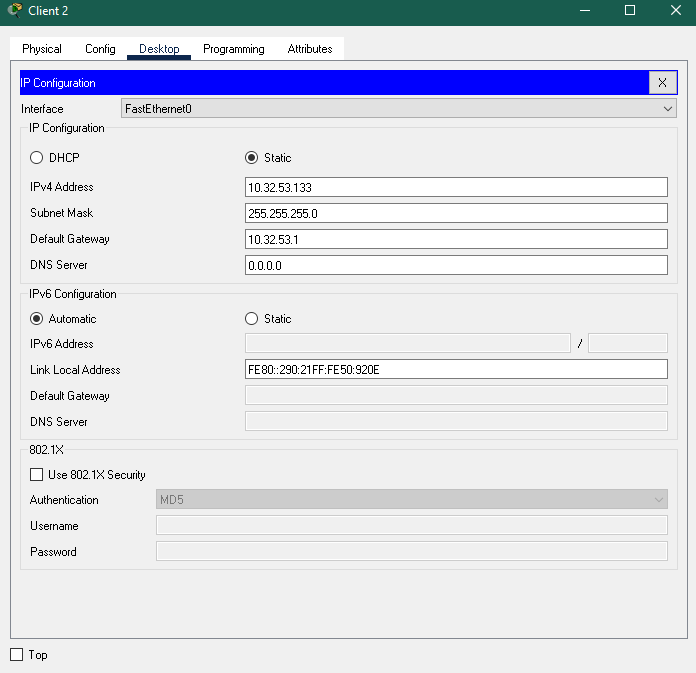
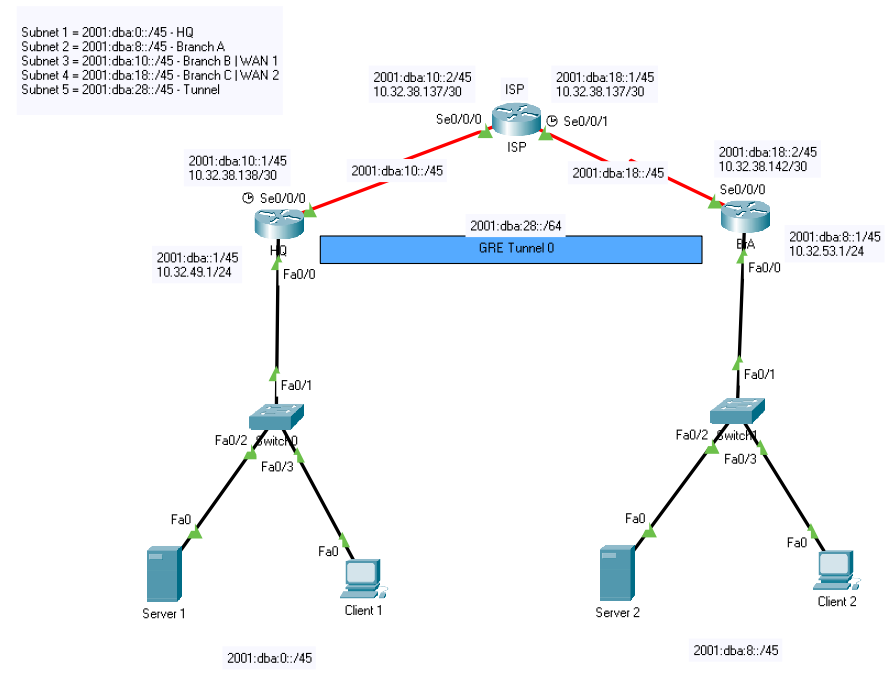
Server 1 Physical Config Services Desktop Programming Attributes IP Configuration IP Configuration DHCP IPv4 Address Subnet Mask Default Gateway DNS Server IPv6 Configuration Automatic IPv6 Address Link Local Address Default Gateway Static 10.32.49.233 255.255.255.0 10.32.49.1 0.0.0.0 Static FE80::20A:41FF:FE49:D520 DNS Server 802.1X Use 802.1X Security Authentication Username Password Top MD5 Client 1 Physical Config Desktop IP Configuration Interface FastEthernet0 IP Configuration DHCP Programming Attributes Static 10.32.49.133 IPv4 Address Subnet Mask Default Gateway DNS Server IPv6 Configuration Automatic IPv6 Address Link Local Address Default Gateway DNS Server 802.1X Use 802.1X Security Authentication Username Password MD5 255.255.255.0 10.32.49.1 0.0.0.0 Static FE80::200:CFF:FE8C:C63E Top Server 2 Physical Config Services Desktop Programming Attributes IP Configuration IP Configuration DHCP IPv4 Address Subnet Mask Default Gateway DNS Server IPv6 Configuration Automatic IPv6 Address Link Local Address Default Gateway DNS Server 802.1X Use 802.1X Security Authentication Username Password MD5 Static 10.32.53.233 255.255.255.0 10.32.53.1 0.0.0.0 Static FE80::260:2FFF:FEAD:D836 Top Client 2 Physical Config Desktop IP Configuration Interface FastEthernet0 IP Configuration DHCP IPv4 Address Subnet Mask Programming Attributes Static 10.32.53.133 255.255.255.0 Default Gateway 10.32.53.1 0.0.0.0 DNS Server IPv6 Configuration Automatic IPv6 Address Link Local Address Default Gateway DNS Server 802.1X Use 802.1X Security Authentication Username Password Top MD5 Static FE80::290:21FF:FE50:920E X Subnet 1 2001:dba:0::/45 - HQ Subnet 2 = 2001:dba:8::/45- Branch A Subnet 3=2001:dba:10::/45 - Branch B | WAN 1 Subnet 4 2001:dba:18::/45-Branch CIWAN 2 Subnet 5=2001:dba:28::/45 - Tunnel 2001:dba:10::2/45 10.32.38.137/30 2001:dba:10::1/45 10.32.38.138/30 2001:dba:18::1/45 ISP 10.32.38.137/30 Se0/0/0 Se0/0/1 ISP 2001:dba:10::/45 Se0/0/0 2001:dba::1/45 10.32.49.1/24 Fa0/0 Fa0 Server 1 Fa0/1 Fa0/2 witch Fa0/3 2001:dba:0::/45 Fa0 2001:dba:28::/64 GRE Tunnel 0 2001:dba:18::2/45 10.32.38.142/30 2001:dba:18::/45 Se0/0/0 Fa0 Client 1 Server 2 2001:dba:8::1/45 BTA 10.32.53.1/24 Fa0/0 Fa0/1 Fa0/2 witch Fa0/3 2001:dba:8::/45 Fa0 g Client 2
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


