Question: Short Answer Question: B.1 How the attacker can exploits data input validation of the application. Give example that clarifies this issue. (2 Marks) Attacker User
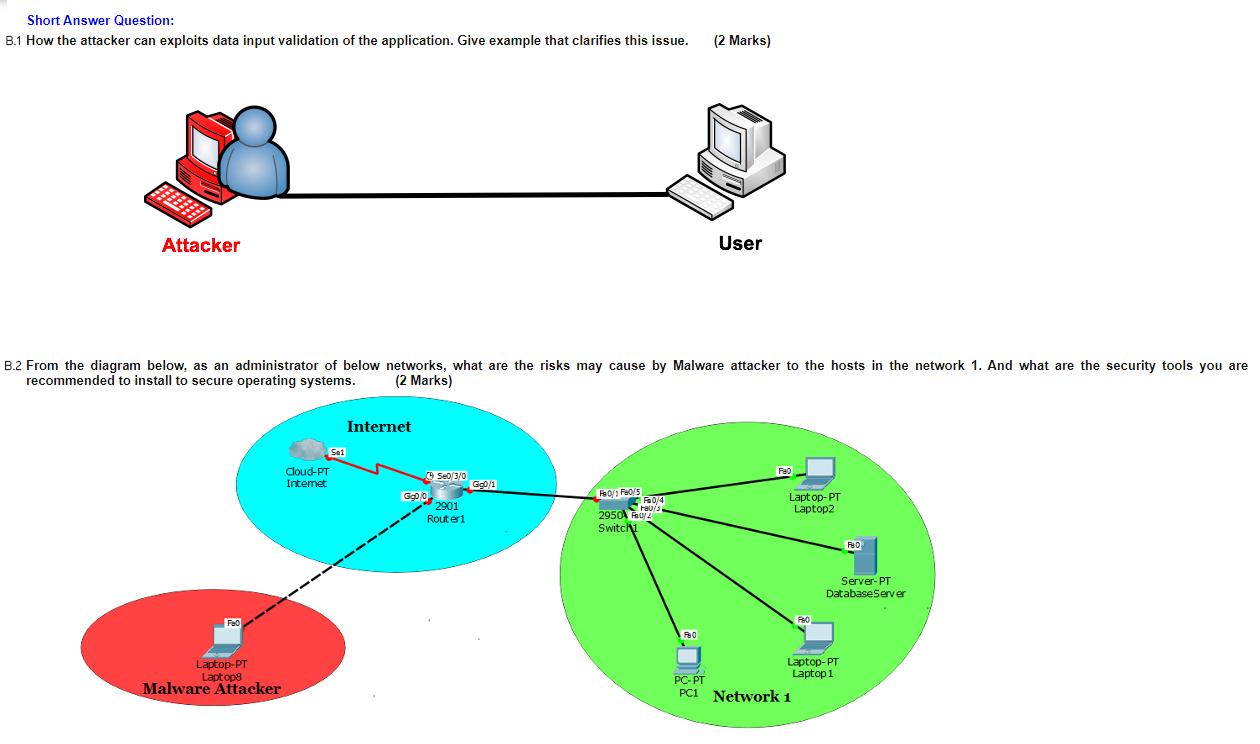
Short Answer Question: B.1 How the attacker can exploits data input validation of the application. Give example that clarifies this issue. (2 Marks) Attacker User B.2 From the diagram below, as an administrator of below networks, what are the risks may cause by Malware attacker to the hosts in the network 1. And what are the security tools you are recommended to install to secure operating systems. (2 Marks) Internet Set Cloud-PT Intemet 52013 G90/1 G900 2901 Routeri Iso Feos hapa 2950A FUZ Laptop-PT Laptop Switch AD Server-PT Database Server FO Laptop-PT Laptops Malware Attacker Laptop-PT PC-PT Laptop 1 PCI Network 1
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


