Question: Social engineering attacks rely on which of the following? Developing exploits for unpatched vulnerabilities. Convincing people to perform a harmful action. Infecting trusted applications with
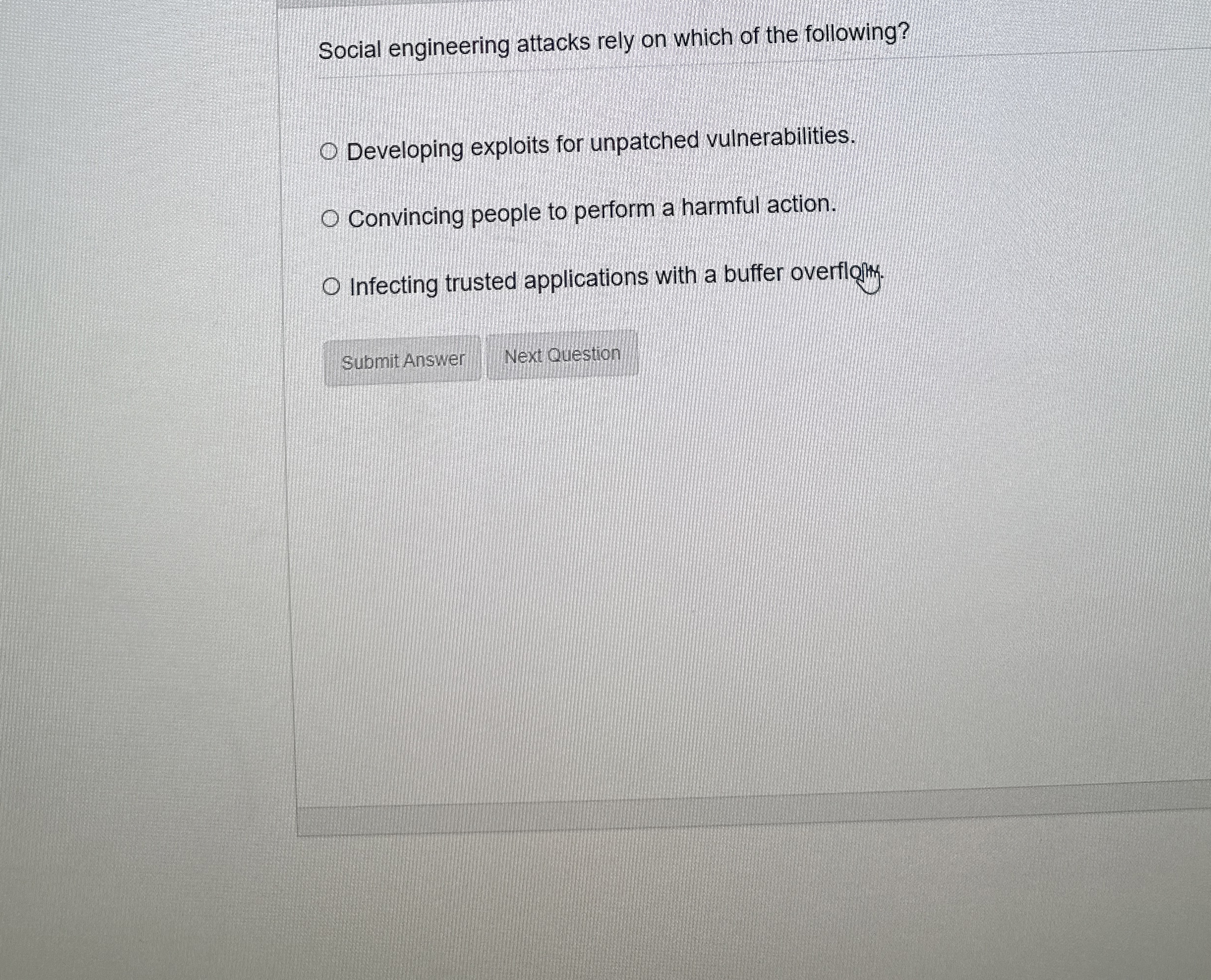
Social engineering attacks rely on which of the following?
Developing exploits for unpatched vulnerabilities.
Convincing people to perform a harmful action.
Infecting trusted applications with a buffer overflofty.
Next Question
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


