Question: Source A Cryptanalyst PR Destination B Source A Cryptanalyst X Message source Encryption algorithm Y-EXPUX Decryption algorithm Destination x- DIPR Message source Encryption algorithm
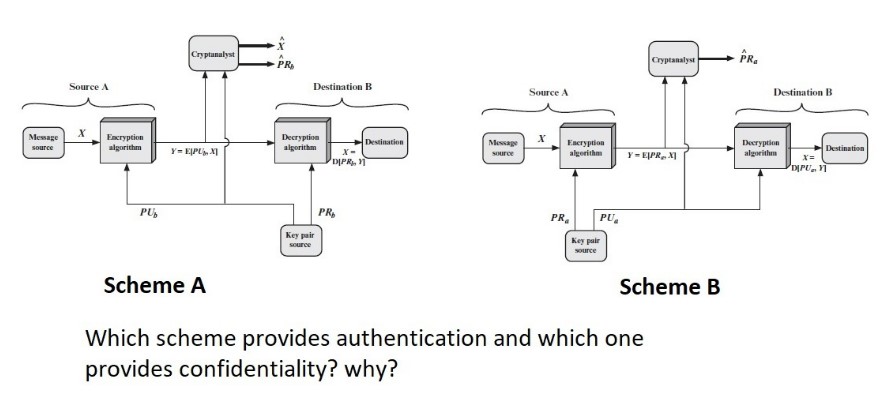
Source A Cryptanalyst PR Destination B Source A Cryptanalyst X Message source Encryption algorithm Y-EXPUX Decryption algorithm Destination x- DIPR Message source Encryption algorithm Y-EPRX] PU Key pair source PR PR Key pair source PU Scheme A Scheme B Which scheme provides authentication and which one provides confidentiality? why? PR. Destination B Decryption algorithm Destination x= DIPU
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


