Question: Suppose you would like to select a method to protect the privacy and integrity of wireless data. Which one of the following methods should you
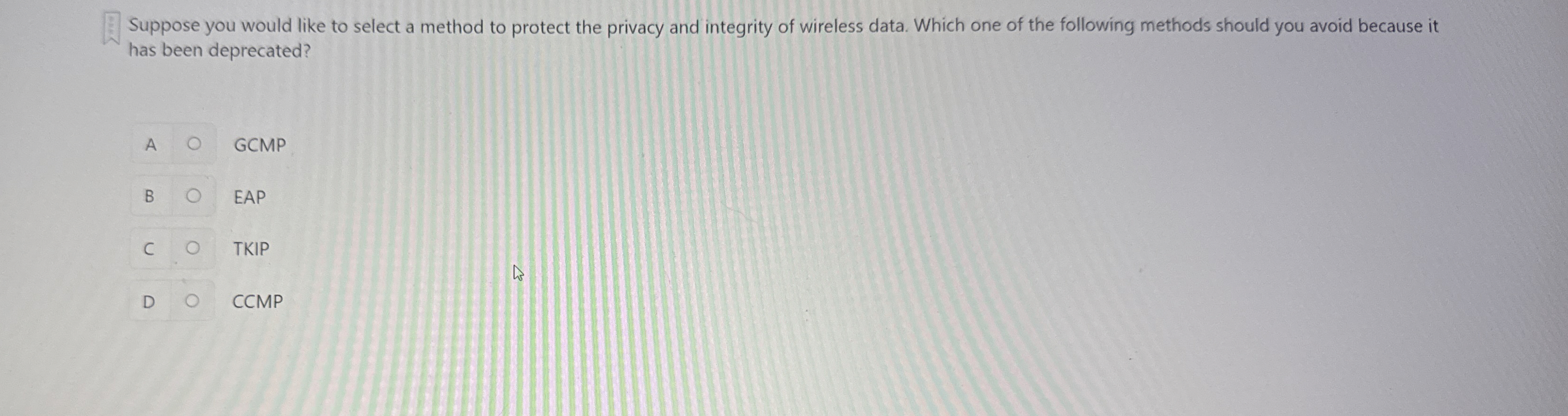
Suppose you would like to select a method to protect the privacy and integrity of wireless data. Which one of the following methods should you avoid because it has been deprecated?
A GCMP
B EAP
TKIP
D CCMP
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


