Question: T or F Statement per-router control (traditional), and logically centralized control (software defined networking) are two approaches for structuring network control plane In SDN
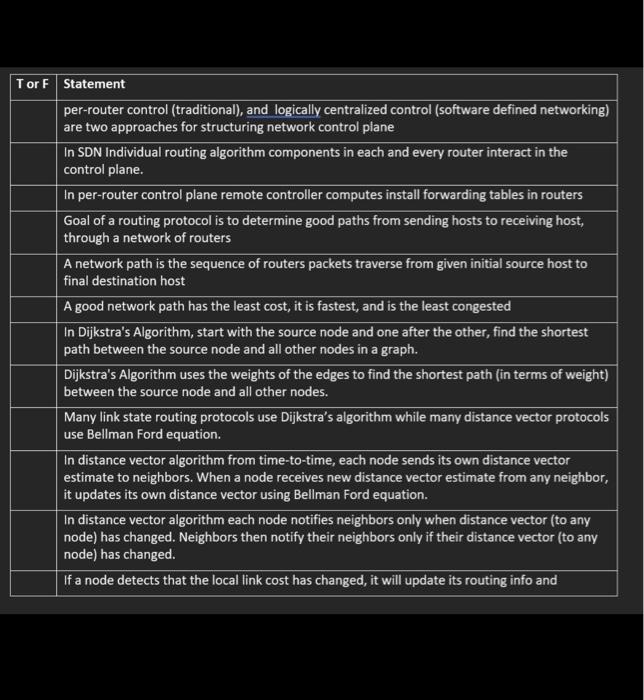
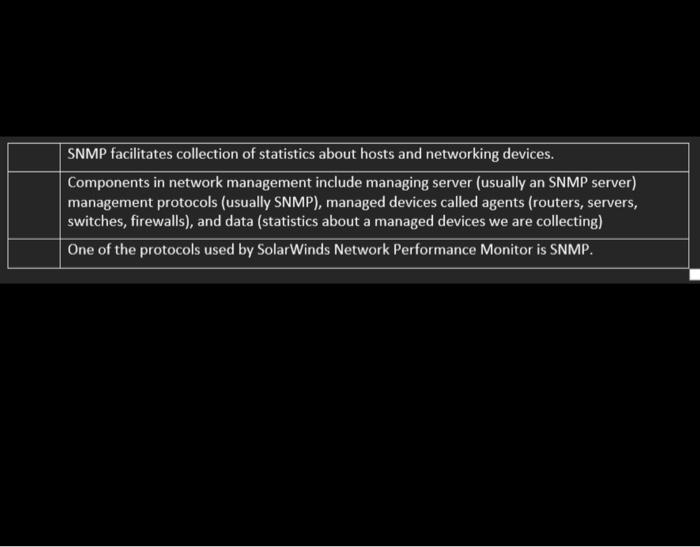
T or F Statement per-router control (traditional), and logically centralized control (software defined networking) are two approaches for structuring network control plane In SDN Individual routing algorithm components in each and every router interact in the control plane. In per-router control plane remote controller computes install forwarding tables in routers Goal of a routing protocol is to determine good paths from sending hosts to receiving host, through a network of routers A network path is the sequence of routers packets traverse from given initial source host to final destination host A good network path has the least cost, it is fastest, and is the least congested In Dijkstra's Algorithm, start with the source node and one after the other, find the shortest path between the source node and all other nodes in a graph. Dijkstra's Algorithm uses the weights of the edges to find the shortest path (in terms of weight) between the source node and all other nodes. Many link state routing protocols use Dijkstra's algorithm while many distance vector protocols use Bellman Ford equation. In distance vector algorithm from time-to-time, each node sends its own distance vector estimate to neighbors. When a node receives new distance vector estimate from any neighbor, it updates its own distance vector using Bellman Ford equation. In distance vector algorithm each node notifies neighbors only when distance vector (to any node) has changed. Neighbors then notify their neighbors only if their distance vector (to any node) has changed. If a node detects that the local link cost has changed, it will update its routing info and SNMP facilitates collection of statistics about hosts and networking devices. Components in network management include managing server (usually an SNMP server) management protocols (usually SNMP), managed devices called agents (routers, servers, switches, firewalls), and data (statistics about a managed devices we are collecting) One of the protocols used by SolarWinds Network Performance Monitor is SNMP.
Step by Step Solution
There are 3 Steps involved in it
True T or False F True T perrouter control traditional and logically centralized control softwaredefined networking are two approaches for structuring ... View full answer

Get step-by-step solutions from verified subject matter experts


