Question: The approach used when the IDS defines the attacks and considers anything outside the defined scope as normal is called Select one O a. Signature
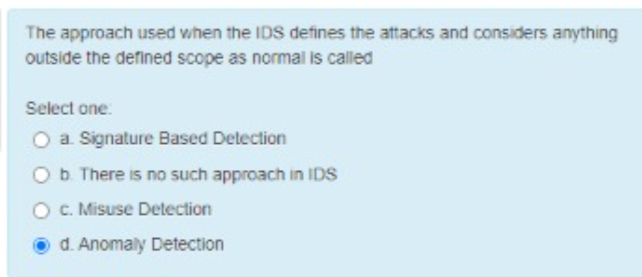
The approach used when the IDS defines the attacks and considers anything outside the defined scope as normal is called Select one O a. Signature Based Detection Ob There is no such approach in IDS c. Misuse Detection d. Anomaly Detection
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


